Free Isaca CRISC Exam Dumps - Page 2
MultipleChoice
It is MOST appropriate for changes to be promoted to production after they are;
OptionsMultipleChoice
A WiFi access points on the enterprise network. Which of the following would be MOST important to include in a report to senior management?
OptionsMultipleChoice
Which of the following should be a risk practitioner s MOST important consideration when developing IT risk scenarios?
OptionsMultipleChoice
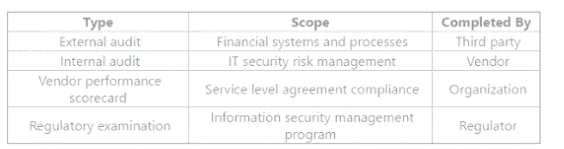
After a high-profile systems breach at an organization s key vendor, the vendor has implemented additional mitigating controls. The vendor has voluntarily shared the following set of assessments:
After a high-profile systems breach at an organization s key vendor, the vendor has implemented additional mitigating controls. The vendor has voluntarily shared the following set of assessments:
Which of the assessments provides the MOST reliable input to evaluate residual risk in the vendor's control environment?
MultipleChoice
Which of the following can be interpreted from a single data point on a risk heat map7
OptionsMultipleChoice
When an organization's disaster recovery plan has a reciprocal agreement, which of the following risk treatment options is being applied?
OptionsMultipleChoice
Establishing ao organizational code of conduct is an example of which type of control?
OptionsMultipleChoice
Which of the following is MOST important to review when determining whether a potential IT service provider s control environment is effective?
OptionsMultipleChoice
A risk assessment has identified that departments have installed their own WiFi access points on the enterprise network. Which of the following would be MOST important to include in a report to senior management?
OptionsMultipleChoice
A risk practitioner observed Vial a high number of pokey exceptions were approved by senior management. Which of the following is the risk practitioner s BEST course of action to determine root cause?
Options
