Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
IFoA_CAA_M0 Exam - Topic 8 Question 40 Discussion
Actual exam question for
IFoA's
IFoA_CAA_M0 exam
Question #: 40
Topic #: 8
[All IFoA_CAA_M0 Questions]
Topic #: 8
The stem and leaf chart below shows the ages of all the pensioners in a small village.
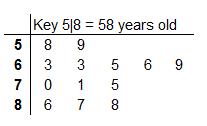
Identify which of the following is not true.
Suggested Answer:
C
Carey
7 months agoElza
7 months agoBernardo
7 months agoCarey
7 months agoShakira
8 months agoLoren
8 months agoKattie
8 months agoRoselle
8 months agoAnna
8 months agoRozella
8 months agoErinn
8 months agoCraig
8 months ago