Forescout FSCP Exam Questions
- Topic 1: General Review of FSCA Topics: This section of the exam measures skills of network security engineers and system administrators, and covers a broad refresh of foundational platform concepts, including architecture, asset identification, and initial deployment considerations. It ensures you are fluent in relevant baseline topics before moving into more advanced areas.
- Topic 2: . Policy Best Practices: This section of the exam measures skills of security policy architects and operational administrators, and covers how to design and enforce robust policies effectively, emphasizing maintainability, clarity, and alignment with organizational goals rather than just technical configuration.
- Topic 3: Policy Functionality: This section of the exam meas-ures skills of policy implementers and integration specialists, and covers how policies operate within the platform, including dependencies, rule order, enforcement triggers, and how they interact with device classifications and dynamic attributes.
- Topic 4: Advanced Product Topics Licenses, Extended Modules and Redundancy: This section of the exam measures skills of product deployment leads and solution engineers, and covers topics such as licensing models, optional modules or extensions, high availability or redundancy configurations, and how those affect architecture and operational readiness.
- Topic 5: Advanced Product Topics Certificates and Identity Tracking: This section of the exam measures skills of identity and access control specialists and security engineers, and covers the management of digital certificates, PKI integration, identity tracking mechanisms, and how those support enforcement and audit capability within the system.
- Topic 6: Notifications: This section of the exam measures skills of monitoring and incident response professionals and system administrators, and covers how notifications are configured, triggered, routed, and managed so that alerts and reports tie into incident workflows and stakeholder communication.
- Topic 7: Plugin Tuning HPS: This section of the exam measures skills of plugin developers and endpoint integration engineers, and covers tuning the Host Property Scanner (HPS) plugin: how to profile endpoints, refine scanning logic, handle exceptions, and ensure accurate host attribute collection for enforcement.
- Topic 8: Plugin Tuning User Directory: This section of the exam measures skills of directory services integrators and identity engineers, and covers tuning plugins that integrate with user directories: configuration, mapping of directory attributes to platform policies, performance considerations, and security implications.
- Topic 9: Plugin Tuning Switch: This section of the exam measures skills of network switch engineers and NAC (network access control) specialists, and covers tuning switch related plugins such as switch port monitoring, layer 2/3 integration, ACL or VLAN assignments via network infrastructure and maintaining visibility and control through those network assets.
- Topic 10: Advanced Troubleshooting: This section of the exam measures skills of operations leads and senior technical support engineers, and covers diagnosing complex issues across component interactions, policy enforcement failures, plugin misbehavior, and end to end workflows requiring root cause analysis and corrective strategy rather than just surface level fixes.
- Topic 11: Customized Policy Examples: This section of the exam measures skills of security architects and solution delivery engineers, and covers scenario based policy design and implementation: you will need to understand business case requirements, craft tailored policy frameworks, adjust for exceptional devices or workflows, and document or validate those customizations in context.
Free Forescout FSCP Exam Actual Questions
Note: Premium Questions for FSCP were last updated On May. 25, 2026 (see below)
If the condition of a sub-rule in your policy is looking for Windows Antivirus updates, how should the scope and main rule read?
Comprehensive and Detailed Explanation From Exact Extract of Forescout Platform Administration and Deployment:
According to theForescout Administration Guide - Define Policy Scope documentationandWindows Update Compliance Template configuration, when the condition of a sub-rule is looking for Windows Antivirus updates, the scope and main rule should read:Scope 'corporate range', filter by group 'windows managed', main rule 'No conditions'.
Policy Scope Definition:
According to the policy scope documentation:
When defining the scope for a Windows Antivirus/Updates policy:
Scope- Should be set to 'corporate range' (endpoints within the corporate IP address range)
Filter by group- Should filter by the 'windows managed' group (Windows endpoints that are manageable)
Main rule- Should have 'No conditions' (meaning the policy applies to all endpoints matching the scope and group)
Why 'No conditions' for the Main Rule:
According to the Windows Update Compliance Template documentation:
The main rule is designed to be:
Broad in scope- Applies to all eligible Windows managed endpoints
Without specific conditions- Specific conditions are handled by sub-rules
Efficient filtering- The scope and group filter do the initial endpoint selection
The sub-rules then contain the specific conditions (e.g., 'Windows Antivirus Update Date < 30 days ago') to evaluate each endpoint's compliance.
Policy Structure for Windows Updates:
According to the documentation:
text
Policy Scope: 'Corporate Range'
Filter by Group: 'windows managed'
Main Rule: 'No Conditions'
Sub-rule 1: 'Windows Antivirus Update Date > 30 days'
Action: Trigger update
Sub-rule 2: 'Windows Antivirus Running = False'
Action: Start Antivirus Service
Sub-rule 3: 'Windows Updates Missing = True'
Action: Initiate Windows Updates
'Windows Managed' Group:
According to the policy template documentation:
The 'windows managed' group specifically includes:
Windows endpoints that can be remotely managed
Endpoints with proper connectivity to management services
Systems with necessary admin accounts configured
Machines capable of executing remote scripts and commands
Why Other Options Are Incorrect:
A . Scope 'all ips', filter by group blank, main rule member of group 'Windows'- Too broad scope (includes non-Windows systems); 'all ips' is inefficient
B . Scope 'corporate range', filter by group 'None', main rule 'member of Group = Windows'- Correct scope and filtering wrong (should filter by group, not in main rule)
C . Scope 'threat exemptions', filter by group 'windows managed', main rule 'member of group = windows'- Wrong scope (threat exemptions is for excluding systems); redundant main rule
E . Scope 'all ips', filter by group 'windows', main rule 'No Conditions'- Too broad initial scope; 'all ips' is inefficient and includes non-corporate systems
Recommended Policy Configuration:
According to the documentation:
For Windows Antivirus/Updates policies:
Scope- Define as 'corporate range' to limit to organizational endpoints
Filter by Group- Set to 'windows managed' to exclude non-manageable systems
Main Rule- Set to 'No conditions' for simplicity; let scope/group do the filtering
Sub-rules- Define specific compliance conditions (e.g., patch level, antivirus status)
This structure ensures:
Efficient policy evaluation
Only applicable Windows endpoints are assessed
Manageable systems are prioritized
Specific compliance checks occur in sub-rules
Referenced Documentation:
Define Policy Scope documentation
Windows Update Compliance Template v2
Defining a Policy Main Rule
Which of the following requires secure connector to resolve?
Comprehensive and Detailed Explanation From Exact Extract of Forescout Platform Administration and Deployment:
According to theForescout HPS Inspection Engine Configuration Guide and Remote Inspection Feature Support documentation,'Authentication login' requires SecureConnector to resolve.
Authentication Login Property:
According to the Remote Inspection and SecureConnector Feature Support documentation:
The'Authentication login'property requires SecureConnector because:
Interactive User Information- Requires access to active user session data
Real-Time Verification- Must check current login status
Endpoint Agent Needed- Cannot be determined via passive network monitoring or remote registry
SecureConnector Required- Installed agent must report login status
SecureConnector vs. Remote Inspection:
According to the HPS Inspection Engine guide:
Some properties require different capabilities:
Property
Remote Inspection (MS-WMI/RPC)
SecureConnector
Authentication login
No
Yes
Authentication login (advanced)
No
Yes
Signed-In status
No
Yes
HTTP login user
No
Yes
Authentication certificate status
Yes
Yes
Why Other Options Are Incorrect:
A . Authentication login (advanced)- While this also requires SecureConnector, the base 'Authentication login' is the more accurate answer
B . Authentication certificate status- This can be resolved via Remote Inspection using certificate stores
C . HTTP login user- This is resolved by SecureConnector, but not listed as requiring it in the same way
E . Signed-In status- While this requires SecureConnector, the more specific answer is 'Authentication login'
SecureConnector Capabilities:
According to the documentation:
SecureConnector resolves endpoint properties that require:
Active user session information
Real-time application/browser monitoring
Deep endpoint inspection
Interactive user credentials
Referenced Documentation:
Remote Inspection and SecureConnector -- Feature Support
Using Certificates to Authenticate the SecureConnector Connection
Which of the following are included in System backups?
Comprehensive and Detailed Explanation From Exact Extract of Forescout Platform Administration and Deployment:
According to theForescout Upgrade Guide and System Backup documentation,Policies are included in System backups.
What System Backups Include:
According to the official documentation:
'Each backup saves all Forescout Platform device and Console settings. This data includes the following:
Configuration
License
Operating System settings
Policies
Profiles
Reports
Administrator accounts
And other system data'
System Backup Contents:
According to the backup documentation:
System backups include:
Policies- All configured policies and policy templates
Configuration- System configuration settings
License Information- License keys and licensing data
Administrator Accounts- User accounts and access controls
Reports- Scheduled and saved reports
System Settings- Mail, network, and other system configurations
Profiles- User profiles and system profiles
What System Backups DO NOT Include:
According to the documentation:
System backups are encrypted using AES-256 and include most system data but are separate from:
Appliance-specific firmware- May require separate backup
Component-specific backups- Some modules have separate backup procedures
Log files- Not typically included in system backups
Why Other Options Are Incorrect:
A . Switch Plugin version 8.7.0 and above- Plugin versions are not individually backed up; plugins are part of the module installation, not system configuration backup
C . Hostname and IP address- While these are part of system configuration, they are covered under 'Configuration' not listed separately in backup contents
D . Failover Clustering plugin- Plugin software itself is not backed up; configuration related to plugins is backed up
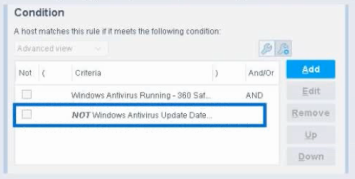
When configuring policies, which of the following statements is true regarding the indicated property?
Select one:
Based on the policy condition image provided showing theNOT checkbox on 'Windows Antivirus Update Data', the correct statement is that theNOT operator negates the criteria inside the property.
Understanding the NOT Operator:
When theNOT checkbox is selectedon a policy condition property, it performs alogical negation (NOT operation) on the criteria evaluation. According to the Forescout Administration Guide:
The NOT operator creates an inverted evaluation:
Without NOT:'Windows Antivirus Update Data = [value]'
Result: Matches endpoints where the property equals the specified value
With NOT (as shown in the image):'NOT (Windows Antivirus Update Data = [value])'
Result: Matches endpoints where the property does NOT equal the specified value
How the NOT Operator Works:
The NOT operator negatesthe criteria inside the property:
Criteria Evaluation- The property condition is evaluated normally first
Negation Applied- The result is then inverted (TRUE becomes FALSE, FALSE becomes TRUE)
Final Result- The endpoint matches only if the negated condition is true
Example from the Image:
The image shows:
First criterion: 'Windows Antivirus Running - 360 Sat' (AND)
Second criterion: 'NOTWindows Antivirus Update Data' (checked)
This means:
The endpoint must have Windows Antivirus Running = True (360 Sat)
ANDthe endpoint must NOT have the Windows Antivirus Update Data property value (whatever was specified)
The NOT negates the criteriainsidethe property condition
NOT vs. 'Evaluate Irresolvable As':
According to the documentation, these areindependent settings:
Setting
Purpose
NOT Checkbox
Negates the criteria evaluation (inverts the match logic)
Evaluate Irresolvable As
Defines how to handle unresolvable properties (when data cannot be determined)
The NOT operator worksinsidethe property evaluation, while 'Evaluate Irresolvable As' is a separate setting that determines behavior when a property cannot be resolved.
Why Other Options Are Incorrect:
A . Irresolvable hosts would match the condition- The NOT operator doesn't specifically affect how irresolvable properties are handled
C . Negates the criteria outside the property- The NOT operator is internal to the property; it negates the criteria inside, not outside
D . Modifies the irresolvable condition to TRUE- The NOT operator doesn't modify the 'Evaluate Irresolvable As' setting; these are independent
E . Negates the 'evaluate irresolvable as' setting- The NOT operator and 'Evaluate Irresolvable As' are separate; NOT doesn't affect or negate that setting
Policy Condition Structure:
According to the Forescout Administration Guide:
A policy condition is structured as:
text
[NOT] [Property Name] [Operator] [Value]
Where:
[NOT]- Optional negation operator (what the checkbox controls)
[Property Name]- The property being evaluated
[Operator]- The comparison operator (equals, contains, greater than, etc.)
[Value]- The value to match against
When NOT is checked, it negates the entire criteria evaluationinsidethat property condition.
Referenced Documentation:
Forescout Administration Guide v8.3
Forescout Administration Guide v8.4
Define policy scope documentation
Forescout eyeSight policy sub-rule advanced options
Which two of the following are main uses of the User Directory plugin? (Choose Two)
Comprehensive and Detailed Explanation From Exact Extract of Forescout Platform Administration and Deployment:
According to theForescout User Directory Plugin documentation, the two main uses of the User Directory plugin are:Verify authentication credentials (A) and Query user details (D).
Main Functions of User Directory Plugin:
According to the official documentation:
'The User Directory plugin resolves endpoint user details and performs user authentication via configured internal and external directory servers.'
The plugin's two primary functions are:
Authenticate Users- Verify/validate authentication credentials
Resolve User Information- Query and retrieve user details from directory servers
Verifying Authentication Credentials:
According to the documentation:
The User Directory plugin:
Validates user credentials against configured directory servers (Active Directory, LDAP, etc.)
Performs authentication for:
Endpoint user authentication
Console login authentication
Guest user registration
RADIUS authentication
Querying User Details:
According to the documentation:
The User Directory plugin:
Resolves endpoint user information including:
User name and identity
Group membership
User properties and attributes
Department and organizational unit information
Retrieves details via LDAP queries when 'Use as directory' is enabled
Why Other Options Are Incorrect:
B . Define authentication traffic- The plugin doesn't define traffic; it queries authentication servers for user information
C . Perform Radius authorization- This is the function of the RADIUS Plugin, not the User Directory plugin (though they work together)
E . Populate the Dashboard- Dashboard population is not a primary function of the User Directory plugin
User Directory vs. RADIUS Plugin:
According to the documentation:
Function
User Directory
RADIUS
Authenticate credentials
Yes
Yes (primary)
Query user details
Yes (primary)
No
802.1X authentication
No
Yes
Authorization
Partial
Yes (primary)
Referenced Documentation:
User Directory plugin overview
About the User Directory Plugin
Initial Setup -- User Directory
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Crystal Nguyen
9 hours agoStephanie Taylor
24 days agoCharles Perez
1 month agoJennifer Martin
28 days agoAmy Allen
1 month agoSusan Stewart
1 month agoWilliam Murphy
26 days agoRebecca Mitchell
21 days agoAmber
2 months agoKimbery
2 months agoMickie
2 months agoKip
3 months agoKimi
3 months agoLouisa
3 months agoJohnetta
3 months agoLuis
4 months agoValene
4 months agoHolley
4 months agoJustine
4 months agoCandra
5 months agoMarge
5 months agoDerick
5 months agoChanel
5 months agoHoa
6 months agoDong
6 months agoJanna
6 months agoYolande
6 months agoKing
7 months agoIra
7 months agoAdell
7 months agoAlberto
7 months agoVirgina
7 months ago