Free CompTIA CAS-004 Exam Dumps - Page 2
MultipleChoice
A security analyst runs a vulnerability scan on a network administrator's workstation. The network administrator has direct administrative access to the company's SSO web portal. The vulnerability scan uncovers critical vulnerabilities with equally high CVSS scores for the user's browser, OS, email client, and an offline password manager. Which of the following should the security analyst patch FIRST?
OptionsMultipleChoice
A company hired a third party to develop software as part of its strategy to be quicker to market. The company's policy outlines the following requirements:
The credentials used to publish production software to the container registry should be stored in a secure location.
Access should be restricted to the pipeline service account, without the ability for the third-party developer to read the credentials directly.
Which of the following would be the BEST recommendation for storing and monitoring access to these shared credentials?
OptionsMultipleChoice
A security engineer is reviewing a record of events after a recent data breach incident that Involved the following:
* A hacker conducted reconnaissance and developed a footprint of the company s Internet-facing web application assets.
* A vulnerability in a third-party horary was exploited by the hacker, resulting in the compromise of a local account.
* The hacker took advantage of the account's excessive privileges to access a data store and exfilltrate the data without detection.
Which of the following is the BEST solution to help prevent this type of attack from being successful in the future?
OptionsMultipleChoice
A company's employees are not permitted to access company systems while traveling internationally. The company email system is configured to block logins based on geographic location, but some employees report their mobile phones continue to sync email traveling . Which of the following is the MOST likely ? (Select TWO.)
OptionsDragDrop
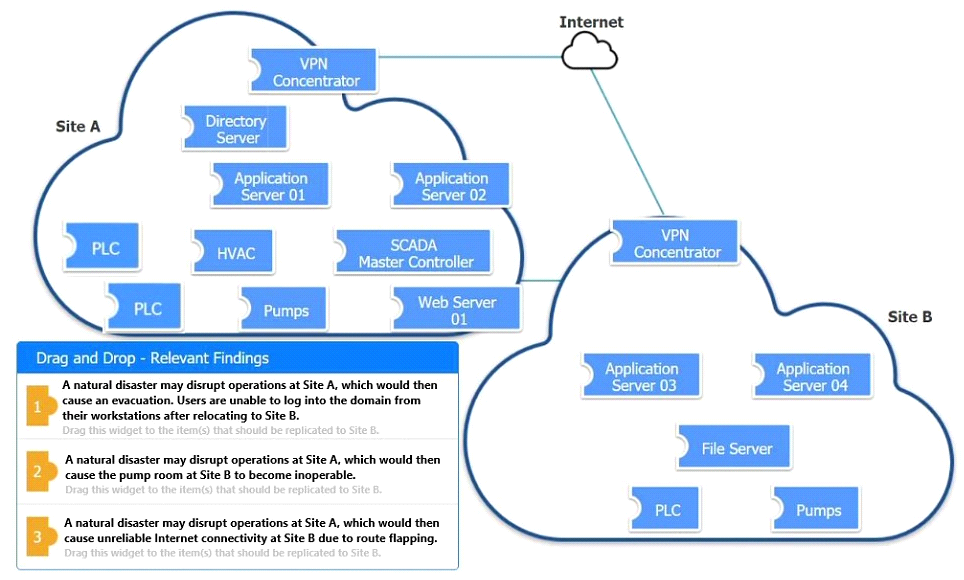
An organization is planning for disaster recovery and continuity of operations.
INSTRUCTIONS
Review the following scenarios and instructions. Match each relevant finding to the affected host.
After associating scenario 3 with the appropriate host(s), click the host to select the appropriate corrective action for that finding.
Each finding may be used more than once.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.









MultipleChoice
A company's employees are not permitted to access company systems while traveling internationally. The company email system is configured to block logins based on geographic location, but some employees report their mobile phones continue to sync email traveling . Which of the following is the MOST likely explanation? (Select TWO.)
OptionsMultipleChoice
An organization decided to begin issuing corporate mobile device users microSD HSMs that must be installed in the mobile devices in order to access corporate resources remotely Which of the following features of these devices MOST likely led to this decision? (Select TWO.)
Options
