Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
CIPS L5M3 Exam - Topic 1 Question 5 Discussion
Actual exam question for
CIPS's
L5M3 exam
Question #: 5
Topic #: 1
[All L5M3 Questions]
Topic #: 1
Which of the following will you put into box 1?
Suggested Answer:
B
The correct answers are as follows:
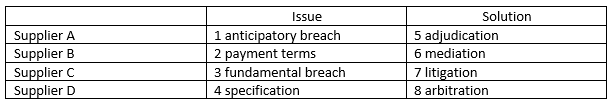
This is arbitration as it involves a panel.
Miles
7 months agoLinette
7 months agoLaquita
7 months agoBulah
7 months agoKris
7 months agoMonroe
8 months agoAdolph
8 months agoMarla
8 months agoCarin
8 months agoAshton
8 months agoGary
8 months agoTalia
8 months agoJolanda
1 year agoTabetha
1 year agoGracia
1 year agoRaina
11 months agoRonny
11 months agoCarlee
12 months agoAshanti
1 year agoRia
11 months agoCassie
12 months agoYuriko
1 year agoCasey
1 year agoLavonna
11 months agoOra
11 months agoLashawn
11 months agoEvangelina
11 months agoDeandrea
11 months agoKattie
11 months agoDorathy
11 months agoTalia
12 months agoZena
1 year agoEdda
1 year agoNichelle
1 year agoDiane
1 year agoCathern
1 year agoDenny
1 year agoHubert
1 year ago