Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Microsoft SC-300 Exam - Topic 3 Question 61 Discussion
Actual exam question for
Microsoft's
SC-300 exam
Question #: 61
Topic #: 3
[All SC-300 Questions]
Topic #: 3
You implement the planned changes for SSPR.
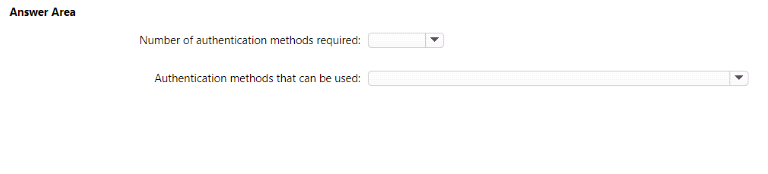
What occurs when User3 attempts to use SSPR? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Suggested Answer:
A
Lisbeth
5 months agoMargot
6 months agoGianna
6 months agoLynette
6 months agoLizbeth
6 months agoDarell
6 months agoThomasena
6 months agoLeah
6 months agoAileen
7 months agoLeota
7 months agoDerrick
7 months agoSabrina
7 months ago