New Year Sale 2026! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Microsoft SC-100 Exam - Topic 13 Question 9 Discussion
Actual exam question for
Microsoft's
SC-100 exam
Question #: 9
Topic #: 13
[All SC-100 Questions]
Topic #: 13
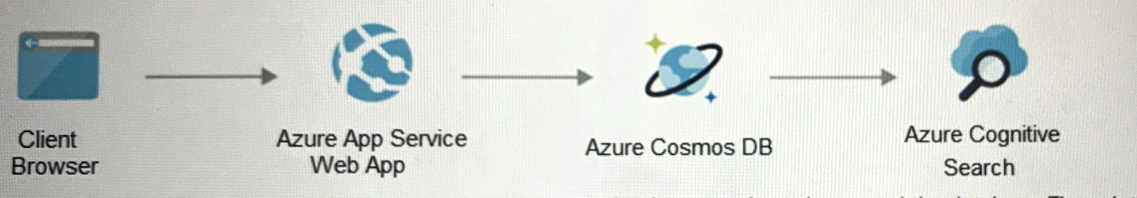
Your on-premises network contains an e-commerce web app that was developed in Angular and Nodejs. The web app uses a MongoDB database. You plan to migrate the web app to Azure. The solution architecture team proposes the following architecture as an Azure landing zone.
You need to provide recommendations to secure the connection between the web app and the database. The solution must follow the Zero Trust model.
Solution: You recommend implementing Azure Key Vault to store credentials.
Suggested Answer:
B
Hillary
4 months agoCarmen
4 months agoCatherin
4 months agoSharita
5 months agoDevon
5 months agoMarya
5 months agoCelia
5 months agoGladis
5 months agoXuan
5 months agoLouann
5 months agoJunita
5 months agoEttie
5 months agoAnissa
5 months ago