New Year Sale 2026! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Microsoft AZ-400 Exam - Topic 6 Question 70 Discussion
Actual exam question for
Microsoft's
AZ-400 exam
Question #: 70
Topic #: 6
[All AZ-400 Questions]
Topic #: 6
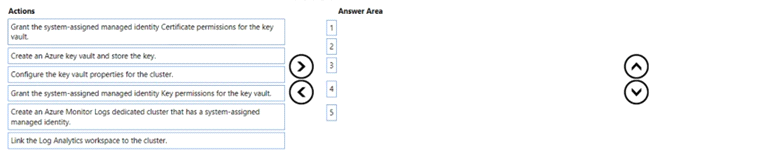
You have an Azure subscription that uses Azure Monitor and contains a Log Analytics workspace.
You have an encryption key.
You need to configure Azure Monitor to use the key to encrypt log data
Suggested Answer:
Create an Azure key vault and store the key.
Configure the key vault properties for the cluster.
Grant the system-assigned managed identity Key permission for the key vault.
Create an Azure Monitor Logs dedicated cluster that has a system-assigned managed identity.
Link the log Analytics workspace to the cluster.
Dorcas
4 months agoAshlee
4 months agoGail
4 months agoTerrilyn
4 months agoRaina
5 months agoAdolph
5 months agoKristofer
5 months agoShantay
5 months agoLinwood
5 months agoMagda
5 months agoSabine
5 months agoAshton
5 months agoShala
5 months agoLaine
5 months ago