Microsoft AZ-400 Exam Questions
Free Microsoft AZ-400 Exam Actual Questions
Note: Premium Questions for AZ-400 were last updated On Apr. 21, 2026 (see below)
You manage source code control and versioning by using GitHub.
A large file it committed to a repository accidentally.
You need to reduce the size of the repository. The solution must remove the file from the repository.
What should you use?
You have a GitHub repository named repol.
You commit a change to repol.
You need to update the commit message. The solution must ensure that the version number remains the same.
Which command should you run?
Your company hosts a web application in Azure. The company uses Azure Pipelines for the build and release management of the application.
Stakeholders report that the past few releases have negatively affected system performance.
You configure alerts in Azure Monitor.
You need to ensure that new releases are only deployed to production if the releases meet defined performance baseline criteria in the staging environment first
What should you use to prevent the deployment of releases that fail to meet the performance baseline?
https://docs.microsoft.com/en-us/azure/azure-monitor/continuous-monitoring
https://docs.microsoft.com/en-us/azure/devops/pipelines/release/approvals/gates?view=azure-devops
You plan to use a NuGet package in a project in Azure DevOps. The NuGet package is in a feed that requires authentication.
You needto ensure that the project can restore the NuGet package automatically.
What should the project use to automate the authentication?
The Azure Artifacts Credential Provider automates the acquisition of credentials needed torestore NuGet
packages as part of your .NET development workflow. It integrates with MSBuild, dotnet, and NuGet(.exe) and works on Windows, Mac, and Linux. Any time you want to use packages from an Azure Artifacts feed, the Credential Provider will automatically acquire and securely store a token on behalf of the NuGet client you're using.
https://github.com/Microsoft/artifacts-credprovider
SIMULATION
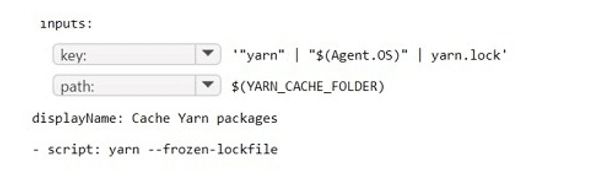
You have an Azure subscription that containsAzure DevOps build pipelines.
You to implement pipeline caching by using the cache task
HOW should you complete the YAML definition? TO answer, select the appropriate options in the answer area.
Answer is as below.
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Justin Walker
5 days agoLaura Ramirez
1 day agoMark Rivera
3 days agoJoni
20 days agoLottie
30 days agoShalon
1 month agoAmira
2 months agoAudrie
2 months agoLeonor
2 months agoRosina
2 months agoAntione
3 months agoSerina
3 months agoLucille
3 months agoShaun
3 months agoHyun
4 months agoViola
4 months agoAnnett
4 months agoCecily
4 months agoBettyann
5 months agoJaclyn
5 months agoMaurine
5 months agoTabetha
5 months agoFelton
6 months agoLaquanda
6 months agoSherrell
6 months agoGerald
6 months agoCarry
7 months agoXenia
7 months agoPortia
7 months agoValda
7 months agoGalen
8 months agoVeronika
8 months agoSantos
8 months agoEmiko
10 months agoLenita
10 months agoFlorinda
10 months agoVincent
11 months agoTimothy
11 months agoHershel
11 months agoAntonio
1 year agoErick
1 year agoXuan
1 year agoDwight
1 year agoGarry
1 year agoIzetta
1 year agoEdison
1 year agoDino
1 year agoJamey
1 year agoVilma
1 year agoTwanna
1 year agoTawna
1 year agoWilliam
1 year agoRicki
1 year agoKattie
1 year agoGeoffrey
1 year agoDulce
1 year agoCherelle
1 year agoBillye
1 year agoAmber
1 year agoTula
1 year agoThea
1 year agoBrittani
2 years agoRoy
2 years agoEttie
2 years agoJannette
2 years agoLindsay
2 years agoBev
2 years agoGwenn
2 years agoGlendora
2 years agoVernell
2 years agoAlison
2 years agoMarguerita
2 years agoLacresha
2 years agoSalley
2 years agoJanae
2 years agoYoulanda
2 years agoAmber
2 years agoTyisha
2 years ago