New Year Sale 2026! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
LPI 202-450 Exam - Topic 10 Question 19 Discussion
Actual exam question for
LPI's
202-450 exam
Question #: 19
Topic #: 10
[All 202-450 Questions]
Topic #: 10
NO: 99
A BIND server should be upgraded to use TSIG. Which configuration parameters should be added if the server should use the algorithm hmac-md5 and the key skrKc4DoTzi/takIlPi7JZA==?
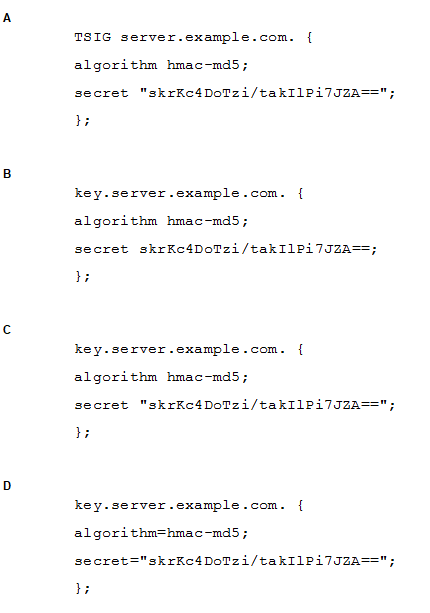
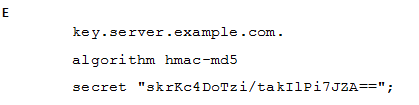
Suggested Answer:
C
Vanda
4 months agoJerry
4 months agoSimona
5 months agoOmer
5 months agoGlory
5 months agoCheryl
5 months agoCurt
5 months agoLuke
5 months agoSlyvia
5 months agoLeandro
5 months agoTrina
5 months ago