Free ISC2 CISSP Exam Dumps - Page 3
MultipleChoice
Which of the following is the MOST important activity an organization performs to ensure that securiy is part of the overall organization culture? A. Ensue security policies are issued to all employees
OptionsMultipleChoice
Which of the following BEST describles a protection profile (PP)?
OptionsMultipleChoice
Which of the following is the BEST statement for a professional to include as port of businees continuity (BC) procedure?
OptionsMultipleChoice
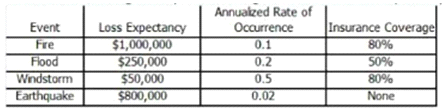
Which of the following would present the highert annualized loss expectancy (ALE)?
MultipleChoice
What balance MUST be considered when web application developers determine how information application error message should be constructed?
OptionsMultipleChoice
Which of the following is a peor entity authentication method for Point-to-Point Protocol (PPP)?
OptionsMultipleChoice
Which of the following practices provides the development team with a definition of security and identification of threats in designing software?
OptionsMultipleChoice
An organization is considering outsourcing applications and data to a Cloud Service Provider (CSP). Which of the following is the MOST important concern regarding privacy?
OptionsMultipleChoice
Assume that a computer was powered off when an information security professional arrived at a crime scene. Which of the following actions should be performed after the crime scene is isolated?
OptionsMultipleChoice
An organization has implemented a new backup process which protects confidential data by encrypting the information stored on backup tapes. Which of the following is a MAJOR data confidentiality concern after the implementation of this new backup process?
Options
