Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Huawei H12-891_V1.0 Exam - Topic 1 Question 18 Discussion
Actual exam question for
Huawei's
H12-891_V1.0 exam
Question #: 18
Topic #: 1
[All H12-891_V1.0 Questions]
Topic #: 1
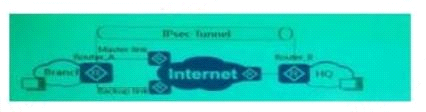
As shown in the figure, the use of redundant links between the branch and the headquarters to establish IPsecVPN, while turning on URLPF on the Router_B for traffic from branch l, which of the following options is correct?
Suggested Answer:
A, C
Pearline
5 months agoIdella
5 months agoHenriette
6 months agoJaime
6 months agoBernardo
6 months agoCeleste
6 months agoLouis
6 months agoFelix
6 months agoGerman
6 months agoFatima
6 months agoTommy
6 months agoDetra
6 months agoTegan
6 months agoNadine
7 months ago