HPE6-A84 Exam Questions
- Topic 1: Integrate Aruba solutions with ecosystem partner solutions/ Define PKI best practices and implement certificate-based authentication
- Topic 2: Design a workflow for Network Analytic Engine (NAE) script development/ Interpret and respond to endpoint classification data, as well as use it to tune policies
- Topic 3: Explain the role of device profiling and risk scoring in a company's security efforts/ Explain and implement role-based access control
- Topic 4: Design and implement Dynamic Segmentation/ Implement Aruba Zero Trust Security for the unified infrastructure using ClearPass Policy Manager
- Topic 5: Design and deploy secure client-to-site access using Aruba Central and Aruba gateways/ Design and deploy Gateway IDS/IPS
- Topic 6: Perform a comprehensive analysis in a set timeframe/ Analyze logs, alerts, and other features at an expert level to detect threats
- Topic 7: Explain how Aruba solutions map to local compliance/ Describe Aruba CloudAuth capabilities and explain how to migrate to an Aruba CloudAuth-based solution
- Topic 8: Architect complex ACLs per wired interface and VLAN/ Design a detection strategy for rogue wireless devices and other wireless threats utilizing Aruba WIPS features
- Topic 9: Design enterprise-wide firewall policies/ Articulate the Aruba Zero Trust Security Strategy
- Topic 10: Implement endpoint classification and device profiling with CPDI/ Explain and implement forensic techniques
Free HP HPE6-A84 Exam Actual Questions
Note: Premium Questions for HPE6-A84 were last updated On 06-11-2025 (see below)
The customer needs a way for users to enroll new wired clients in Intune. The clients should have limited access that only lets them enroll and receive certificates. You plan to set up these rights in an AOS-CX role named ''provision.''
The customer's security team dictates that you must limit these clients' Internet access to only the necessary sites. Your switch software supports IPv4 and IPv6 addresses for the rules applied in the ''provision'' role.
What should you recommend?
This is because a downloadable user role (DUR) is a feature that allows the switch to use a central ClearPass server to download user-roles to the switch for authenticated users12A DUR can contain various attributes and rules that define the access level and privileges of the user, such as VLAN, ACL, PoE, reauthentication period, etc3A DUR can also be customized and updated on the ClearPass server without requiring any changes on the switch1
A DUR can be used to create a ''provision'' role that allows users to enroll new wired clients in Intune. The ''provision'' role can have limited access that only lets them enroll and receive certificates from the Intune service. The ''provision'' role can also have rules that restrict the Internet access of the users to only the necessary sites, such as the Intune portal and the certificate authority.The rules can be based on IPv4 or IPv6 addresses, depending on the network configuration and preference2
A) Configuring the rules for the ''provision'' role with IPv6 addresses, which tend to be more stable. This is not a valid recommendation because it does not address how to create and apply the ''provision'' role on the switch.Moreover, IPv6 addresses do not necessarily tend to be more stable than IPv4 addresses, as both protocols have their own advantages and disadvantages4
B) Enabling tunneling to the MCs on the ''provision'' role and then setting up the privileges on the MCs. This is not a valid recommendation because it does not explain how to enable tunneling or what MCs are.Moreover, tunneling is a technique that encapsulates one network protocol within another, which adds complexity and overhead to the network communication5
D) Assigning the ''provision'' role to a VLAN and then setting up the rules within a Layer 2 access control list (ACL). This is not a valid recommendation because it does not explain how to assign a role to a VLAN or how to create a Layer 2 ACL on the switch.Moreover, a Layer 2 ACL is limited in its filtering capabilities, as it can only match on MAC addresses or Ethernet types, which might not be sufficient for restricting Internet access to specific sites
Refer to the scenario.
A customer requires these rights for clients in the ''medical-mobile'' AOS firewall role on Aruba Mobility Controllers (MCs):
External devices should not be permitted to initiate sessions with ''medical-mobile'' clients, only send return traffic.
The exhibits below show the configuration for the role.
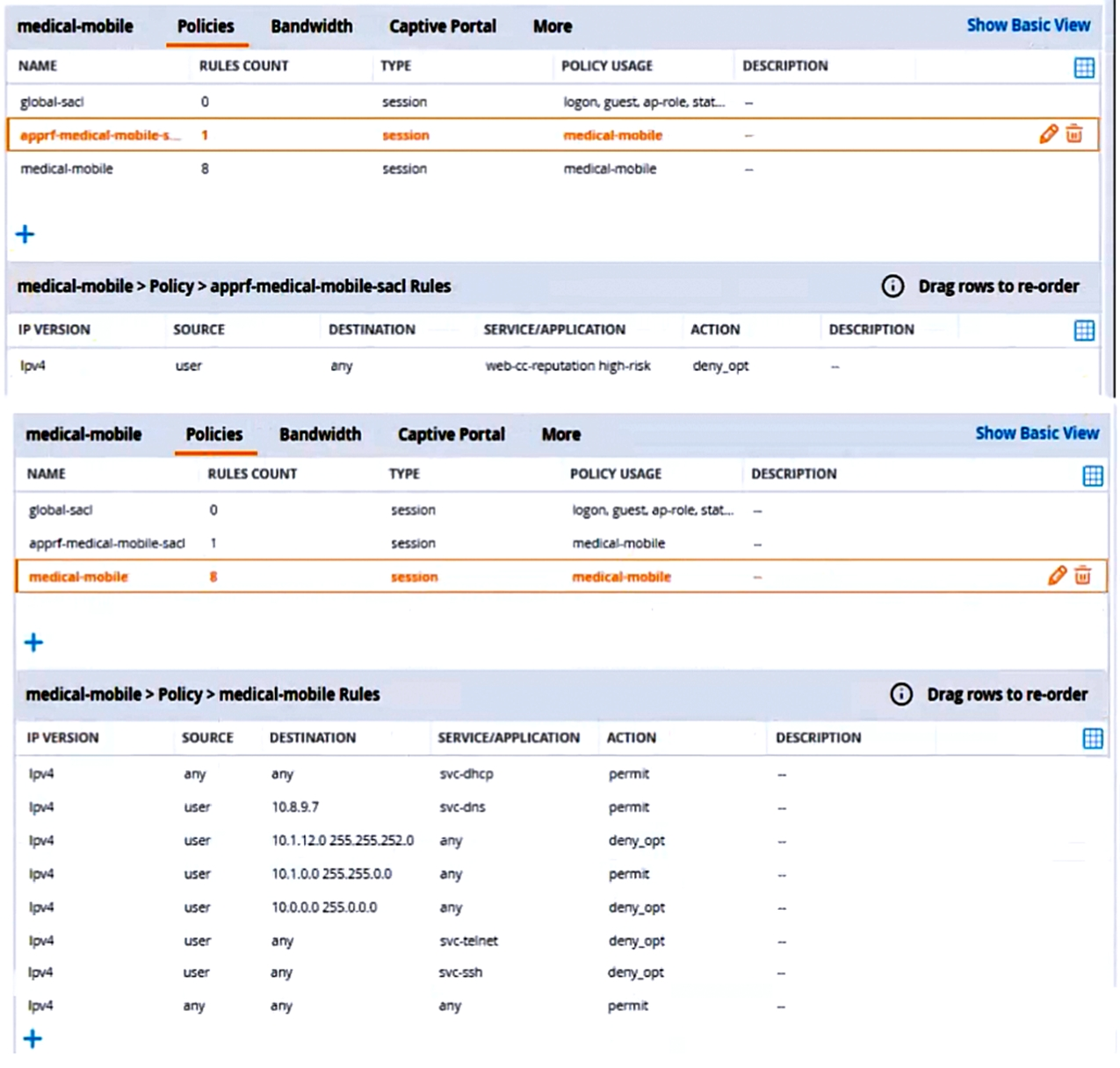
There are multiple issues with this configuration. What is one change you must make to meet the scenario requirements? (In the options, rules in a policy are referenced from top to bottom. For example, ''medical-mobile'' rule 1 is ''ipv4 any any svc-dhcp permit,'' and rule 8 is ''ipv4 any any any permit''.)
The subnet mask in rule 3 of the ''medical-mobile'' policy is currently 255.255.252.0, which means that the rule denies access to the 10.1.12.0/22 subnet as well as the adjacent 10.1.16.0/22 subnet1. This is not consistent with the scenario requirements, which state that only the 10.1.12.0/22 subnet should be denied access, while the rest of the 10.1.0.0/16 range should be permitted access.
To fix this issue, the subnet mask in rule 3 should be changed to 255.255.248.0, which means that the rule only denies access to the 10.1.8.0/21 subnet, which includes the 10.1.12.0/22 subnet1. This way, the rule matches the scenario requirements more precisely.
Refer to the scenario.
A customer has an AOS10 architecture that is managed by Aruba Central. Aruba infrastructure devices authenticate clients to an Aruba ClearPass cluster.
In Aruba Central, you are examining network traffic flows on a wireless IoT device that is categorized as ''Raspberry Pi'' clients. You see SSH traffic. You then check several more wireless IoT clients and see that they are sending SSH also.
You want a relatively easy way to communicate the information that an IoT client has used SSH to Aruba CPPM.
What is one prerequisite?
The customer needs a way for users to enroll new wired clients in Intune. The clients should have limited access that only lets them enroll and receive certificates. You plan to set up these rights in an AOS-CX role named ''provision.''
The customer's security team dictates that you must limit these clients' Internet access to only the necessary sites. Your switch software supports IPv4 and IPv6 addresses for the rules applied in the ''provision'' role.
What should you recommend?
This is because a downloadable user role (DUR) is a feature that allows the switch to use a central ClearPass server to download user-roles to the switch for authenticated users12A DUR can contain various attributes and rules that define the access level and privileges of the user, such as VLAN, ACL, PoE, reauthentication period, etc3A DUR can also be customized and updated on the ClearPass server without requiring any changes on the switch1
A DUR can be used to create a ''provision'' role that allows users to enroll new wired clients in Intune. The ''provision'' role can have limited access that only lets them enroll and receive certificates from the Intune service. The ''provision'' role can also have rules that restrict the Internet access of the users to only the necessary sites, such as the Intune portal and the certificate authority.The rules can be based on IPv4 or IPv6 addresses, depending on the network configuration and preference2
A) Configuring the rules for the ''provision'' role with IPv6 addresses, which tend to be more stable. This is not a valid recommendation because it does not address how to create and apply the ''provision'' role on the switch.Moreover, IPv6 addresses do not necessarily tend to be more stable than IPv4 addresses, as both protocols have their own advantages and disadvantages4
B) Enabling tunneling to the MCs on the ''provision'' role and then setting up the privileges on the MCs. This is not a valid recommendation because it does not explain how to enable tunneling or what MCs are.Moreover, tunneling is a technique that encapsulates one network protocol within another, which adds complexity and overhead to the network communication5
D) Assigning the ''provision'' role to a VLAN and then setting up the rules within a Layer 2 access control list (ACL). This is not a valid recommendation because it does not explain how to assign a role to a VLAN or how to create a Layer 2 ACL on the switch.Moreover, a Layer 2 ACL is limited in its filtering capabilities, as it can only match on MAC addresses or Ethernet types, which might not be sufficient for restricting Internet access to specific sites
Refer to the scenario.
A customer requires these rights for clients in the ''medical-mobile'' AOS firewall role on Aruba Mobility Controllers (MCs):
External devices should not be permitted to initiate sessions with ''medical-mobile'' clients, only send return traffic.
The exhibits below show the configuration for the role.
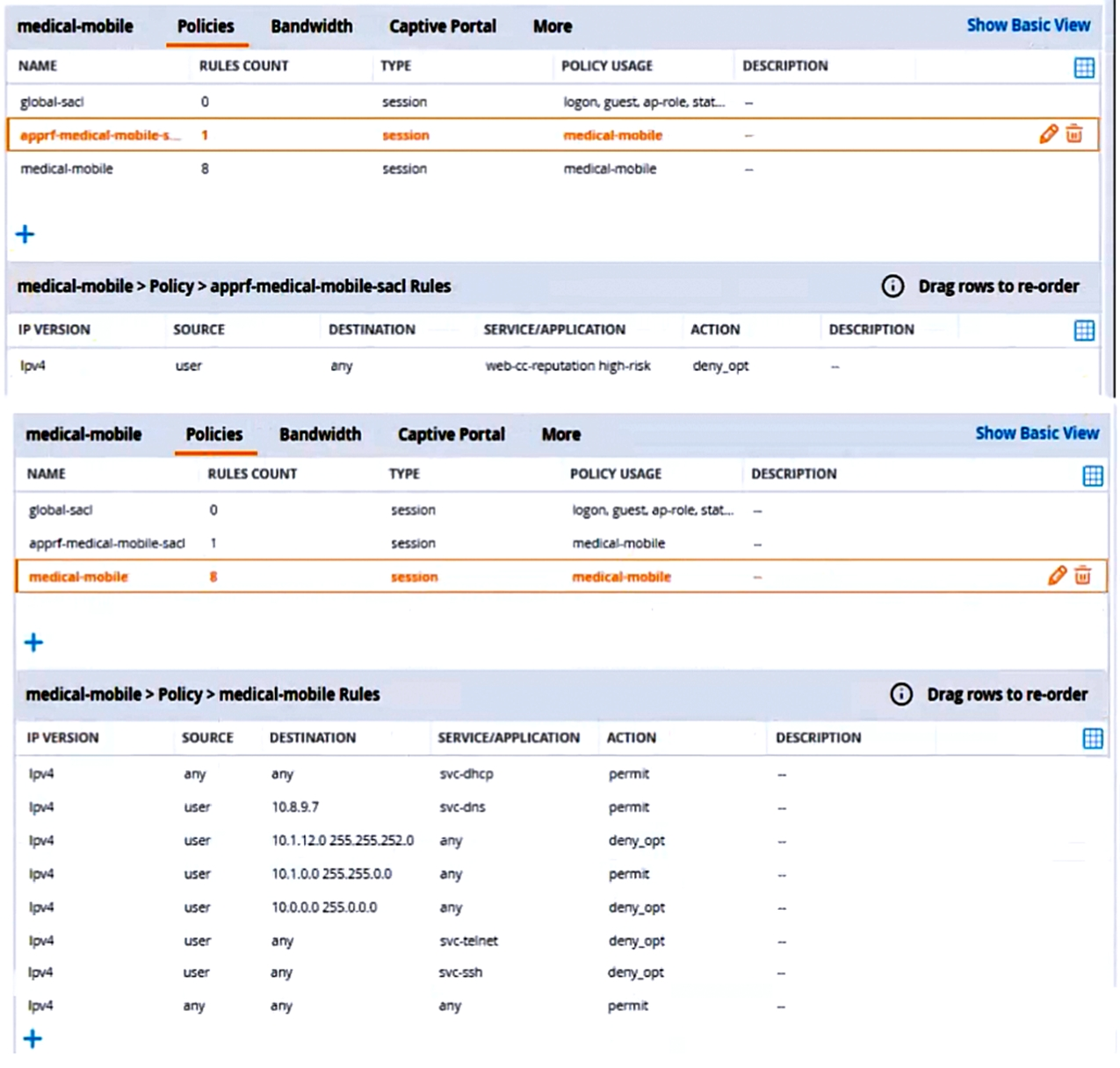
There are multiple issues with this configuration. What is one change you must make to meet the scenario requirements? (In the options, rules in a policy are referenced from top to bottom. For example, ''medical-mobile'' rule 1 is ''ipv4 any any svc-dhcp permit,'' and rule 8 is ''ipv4 any any any permit''.)
The subnet mask in rule 3 of the ''medical-mobile'' policy is currently 255.255.252.0, which means that the rule denies access to the 10.1.12.0/22 subnet as well as the adjacent 10.1.16.0/22 subnet1. This is not consistent with the scenario requirements, which state that only the 10.1.12.0/22 subnet should be denied access, while the rest of the 10.1.0.0/16 range should be permitted access.
To fix this issue, the subnet mask in rule 3 should be changed to 255.255.248.0, which means that the rule only denies access to the 10.1.8.0/21 subnet, which includes the 10.1.12.0/22 subnet1. This way, the rule matches the scenario requirements more precisely.
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Fausto
7 months agoChu
7 months agoGlory
8 months agoArlie
8 months agoCoral
8 months agoLeonie
9 months agoDetra
9 months agoTerina
11 months agoDahlia
12 months agoJoana
1 year agoLinwood
1 year agoVallie
1 year agoLatia
1 year agoPeter
1 year agoKizzy
1 year agoDierdre
1 year agoIlona
1 year agoRana
2 years agoMelissia
2 years agoKatina
2 years agoRolf
2 years agoHelga
2 years agoDetra
2 years agoGoldie
2 years agoCecil
2 years agoCecilia
2 years agoNatalie
2 years agoCecilia
2 years agoEthan
2 years agoMitsue
2 years agoEvangelina
2 years agoEladia
2 years agoBlondell
2 years agoMike
2 years agoWinifred
2 years agoLavonna
2 years agoLorrine
2 years agoBrittani
2 years ago