Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
GIAC GASF Exam - Topic 2 Question 11 Discussion
Actual exam question for
GIAC's
GASF exam
Question #: 11
Topic #: 2
[All GASF Questions]
Topic #: 2
Review the message database below.
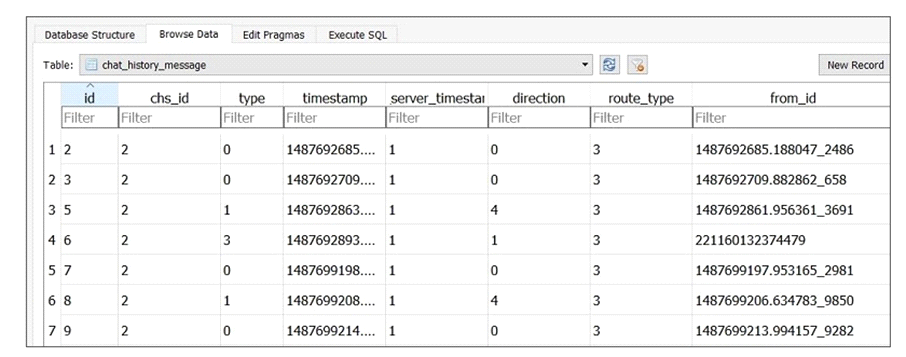
What can be determined based on the information provided?
Suggested Answer:
B
Regenia
7 months agoIrma
7 months agoHarley
7 months agoArdella
8 months agoStaci
8 months agoGeorgeanna
8 months agoArmanda
8 months agoBelen
8 months agoBulah
8 months agoJustine
8 months agoTyra
8 months agoMy
8 months ago