Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
GAQM PPM-001 Exam - Topic 10 Question 57 Discussion
Actual exam question for
GAQM's
PPM-001 exam
Question #: 57
Topic #: 10
[All PPM-001 Questions]
Topic #: 10
Draw the precedence diagram for the dependencies and activity times below to answer the question. Use AON or another technique to derive the answer using F-S relationships.
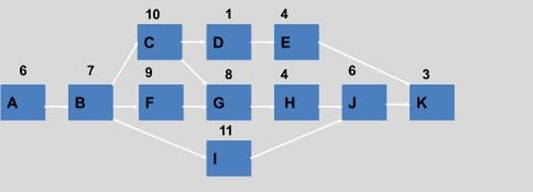
What is the critical path duration for the given schedule network?
Suggested Answer:
D
Erinn
6 months agoKati
6 months agoJeanice
7 months agoGolda
7 months agoTamesha
7 months agoShonda
7 months agoMarvel
7 months agoElmira
7 months agoRegenia
7 months agoMargurite
7 months agoSueann
7 months agoLemuel
7 months agoElbert
8 months ago