Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Eccouncil ECSS Exam - Topic 3 Question 3 Discussion
Actual exam question for
Eccouncil's
ECSS exam
Question #: 3
Topic #: 3
[All ECSS Questions]
Topic #: 3
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He is using a tool to crack the wireless encryption keys. The description of the tool is as follows:
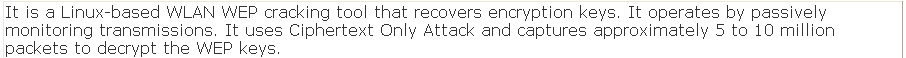
Which of the following tools is John using to crack the wireless encryption keys?
Suggested Answer:
A
Lindy
7 months agoCiara
7 months agoTula
7 months agoHenriette
8 months agoDominga
8 months agoSharika
8 months agoKristeen
8 months agoGwenn
8 months agoFabiola
8 months agoCandra
8 months agoLuann
8 months agoArlene
8 months ago