Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Cisco 200-201 Exam - Topic 3 Question 45 Discussion
Actual exam question for
Cisco's
200-201 exam
Question #: 45
Topic #: 3
[All 200-201 Questions]
Topic #: 3
Refer to the exhibit.
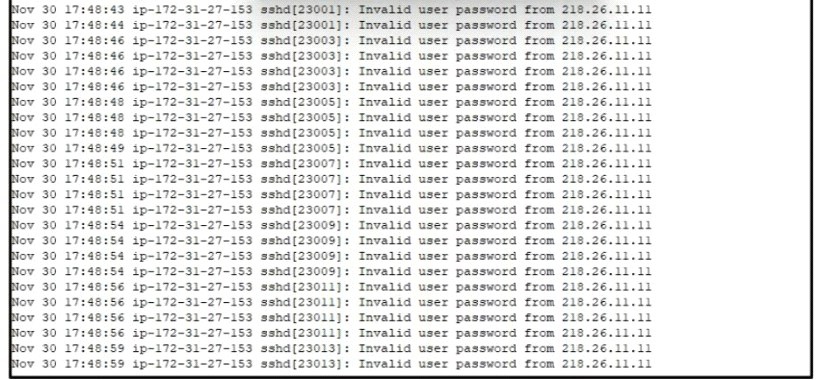
A security analyst is investigating unusual activity from an unknown IP address Which type of evidence is this file1?
Suggested Answer:
A
Brendan
4 months agoSkye
4 months agoGlory
4 months agoJohnetta
5 months agoLuz
5 months agoMerlyn
5 months agoBreana
5 months agoAnnamae
5 months agoDanica
5 months agoCyndy
6 months agoCherri
6 months agoAimee
6 months agoDoyle
6 months agoGlory
6 months ago