Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Trend Deep-Security-Professional Exam - Topic 1 Question 13 Discussion
Actual exam question for
Trend's
Deep-Security-Professional exam
Question #: 13
Topic #: 1
[All Deep-Security-Professional Questions]
Topic #: 1
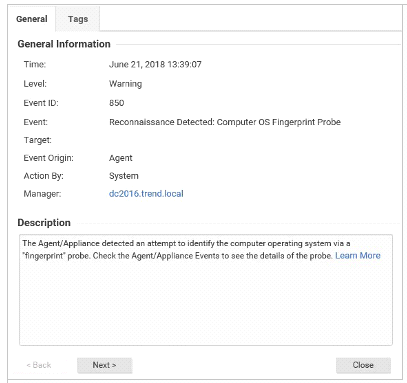
Based on the details of event displayed in the exhibit, which of the following statements is false?
Suggested Answer:
C
Rodrigo
6 months agoElroy
6 months agoDiane
6 months agoBettina
6 months agoJules
6 months agoCarli
7 months agoFannie
7 months agoErnie
7 months agoRashad
7 months agoRosendo
7 months agoOmega
7 months agoNarcisa
7 months ago