Splunk SPLK-2003 Exam Questions
- Topic 1: Deployment, Installation, and Initial Configuration: Splunk SOAR fundamentals are crucial for cybersecurity professionals preparing for the SPLK-2003 exam. This topic covers SOAR operation, installation, architecture, and configuration for effective implementation.
- Topic 2: User Management: User Management in the SPLK-2003 exam tests candidates on adding users, configuring authentication, and creating roles. SOC analysts and administrators who attempt the exam must manage user access and permissions.
- Topic 3: Apps, Assets, and Playbooks: Cybersecurity professionals should understand assets, configuring apps, and data ingestion for the SPLK-2003 exam. Proficiency in these areas enhances SOAR's automation and security tool integration.
- Topic 4: Analyst Queue: The Analyst Queue topic focuses on search features and filter creation. SOC analysts who attempt the Splunk SOAR Certified Automation Developer exam must prepare to manage and prioritize security events effectively within the SOAR platform.
- Topic 5: The Investigation Page: Candidates of the Splunk SPLK-2003 test are assessed on their investigation skills using SOAR's tools. This includes navigating the Investigation page, running actions and playbooks, and managing case files efficiently.
- Topic 6: Case Management and Workbooks: Case Management and Workbooks topic prepares Splunk analysts and administrators for managing complex security incidents using workbooks and marking evidence within the SOAR platform.
- Topic 7: Customizations: Candidates of the Splunk SOAR Certified Automation Developer test learn to tailor SOAR to meet organizational needs, covering customization of severity levels, CEF fields, and workbooks. This topic is essential for those aiming to take the SPLK-2003 exam.
- Topic 8: System Maintenance: The Splunk SPLK-2003 exam assesses candidates on their ability to monitor and maintain SOAR's performance. Understanding reports, system health, and logs is crucial for cybersecurity professionals to pass the test.
- Topic 9: Introduction to Playbooks: Sub-topics are about available app actions, automation best practices, I2A2 design methodology, and playbook capabilities. To pass the Splunk SPLK-2003 exam, applicant must get knowledge about these concepts to ensure success.
- Topic 10: Visual Playbook Editor: Sub-topics are about using the editor, executing actions from playbooks, and testing new playbooks. Cybersecurity professionals who attempt the Splunk SOAR Certified Automation Developer exam must learn how to create and modify automated workflows by using SOAR’s visual interface.
- Topic 11: Logic, Filters, and User Interaction: It focuses on usage of decision blocks, join options, filter blocks, and user interaction features. SOC analysts must get knowledge about interactive playbooks as well.
- Topic 12: Formatted Output and Data Access: Formatted Output and Data Access topic teaches structuring data, understanding action results, and composing datapaths. This knowledge enhances automation by manipulating and accessing data effectively.
- Topic 13: Modular Playbook Development: Designing modular solutions and invoking child playbooks for scalable and reusable components is the focus here. This enhances automation efficiency, a key skill for those aiming to take the SPLK-2003 exam.
- Topic 14: Custom Lists and Data Routing: Custom Lists and data routing are covered, including creating custom lists and using filters for data control. This topic ensures SOC analysts effectively manage custom data in SOAR.
- Topic 15: Configuring External Splunk Search: In this topic of the SPLK-2003 exam, cybersecurity professionals learn about using reindex and reporting features, configuring both SOAR and Splunk instances, and externalizing search to Splunk.
- Topic 16: Integrating SOAR into Splunk: You learn about installing and configuring necessary apps, using Splunk search from playbooks, and sending Enterprise Security notables to SOAR.
- Topic 17: Custom Coding: The primary focus of this topic is on writing custom SOAR code, using the global block, and custom function blocks.
- Topic 18: Using REST: Splunk Enterprise Security administrators and SOC analysts cover sub-topics related to accessing SOAR data from other systems, SOAR REST API capabilities, and Django queries.
Free Splunk SPLK-2003 Exam Actual Questions
Note: Premium Questions for SPLK-2003 were last updated On May. 26, 2026 (see below)
Which of the following is the best option for an analyst who wants to run a single action on an event?
The best option for an analyst who wants to run a single action on an event is to open the event and run the action directly from the Investigation View. The Investigation View allows users to interact with events directly, and provides the ability to execute specific actions without the need for playbook development or debugging. This is the most straightforward and efficient way to execute a single action on an event, without the overhead of creating or editing playbooks.
While creating a playbook and using the Playbook Debugger are viable options, they introduce unnecessary complexity for running just one action. The goal is to allow the analyst to act quickly and efficiently within the Investigation View.
Splunk SOAR Documentation: Investigation View Overview.
Splunk SOAR Best Practices for Running Actions on Events.
A user has written a playbook that calls three other playbooks, one after the other. The user notices that the second playbook starts executing before the first one completes. What is the cause of this behavior?
The correct answer is D because synchronous execution has not been configured. Synchronous execution is a feature that allows you to control the order of execution of playbook blocks. By default, Phantom executes playbook blocks asynchronously, meaning that it does not wait for one block to finish before starting the next one. This can cause problems when you have dependencies between blocks or when you call other playbooks. To enable synchronous execution, you need to use thesyncaction in therun playbookblock and specify the name of the next block to run after the called playbook completes. SeeSplunk SOAR Documentationfor more details.
In Splunk SOAR, playbooks can be executed either synchronously or asynchronously. Synchronous execution ensures that a playbook waits for a called playbook to complete before proceeding to the next step. If the second playbook starts executing before the first one completes, it indicates that synchronous execution was not configured for the playbooks. Without synchronous execution, playbooks will execute independently of each other's completion status, leading to potential overlaps in execution. This behavior can be controlled by properly configuring the playbook execution settings to ensure that dependent playbooks complete their tasks in the desired order.
What is the default embedded search engine used by SOAR?
the default embedded search engine used by SOAR is the SOAR search engine, which is powered by the PostgreSQL database built-in to Splunk SOAR (Cloud). A Splunk SOAR (Cloud) Administrator can configure options for search from the Home menu, in Search Settings under Administration Settings. The SOAR search engine has been modified to accept the * wildcard and supports various operators and filters. For search syntax and examples, see Search within Splunk SOAR (Cloud)2.
Option A is incorrect, because the embedded Splunk search engine was used in earlier releases of Splunk SOAR (Cloud), but not in the current version. Option C is incorrect, because Django is a web framework, not a search engine. Option D is incorrect, because Elastic is a separate search engine that is not embedded in Splunk SOAR (Cloud).
1: Configure search in Splunk SOAR (Cloud) 2: Search within Splunk SOAR (Cloud)
Splunk SOAR utilizes its own embedded search engine by default, which is tailored to its security orchestration and automation framework. While Splunk SOAR can integrate with other search engines, like the Embedded Splunk search engine, for advanced capabilities and log analytics, its default setup comes with an embedded search engine optimized for the typical data and search patterns encountered within the SOAR platform.
Two action blocks, geolocate_ip 1 and file_reputation_2, are connected to a decision block. Which of the following is a correct configuration for making a decision on the action results from one of the given blocks?
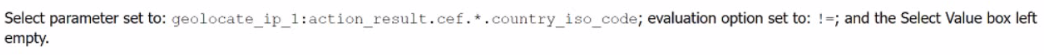
A.
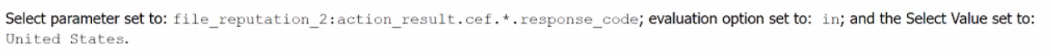
B.
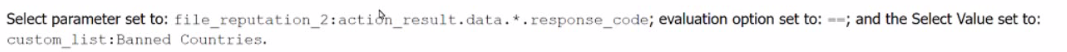
C.
D.
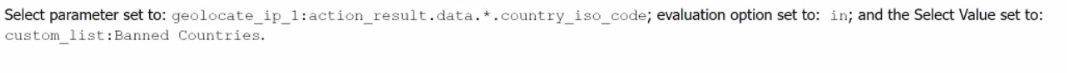
In the given decision block, you are trying to evaluate the results of two action blocks: geolocate_ip_1 and file_reputation_2. The correct configuration for making a decision based on the result of geolocate_ip_1 is by checking the country_iso_code field from the action result and setting the evaluation option to != (not equal), with no specific value provided in the 'Select Value' box. This essentially checks whether a valid country ISO code exists in the action result and proceeds if it's not empty or different from a specific value. This is a common check when working with geolocation results to see if a response has been returned.
Other options (B, C, and D) include response codes or list comparisons, which do not align with the decision structure mentioned, which needs to operate based on a country_iso_code field.
Splunk SOAR Playbook Development Guide.
Splunk SOAR Documentation on Decision Blocks and Action Result Evaluation.
When analyzing events, a working on a case, significant items can be marked as evidence. Where can ail of a case's evidence items be viewed together?
In Splunk SOAR, when working on a case and analyzing events, items marked as significant evidence are aggregated for review. These evidence items can be collectively viewed on the Investigation page under the Evidence tab. This centralized view allows analysts to easily access and review all marked evidence related to a case, facilitating a streamlined analysis process and ensuring that key information is readily available for investigation and decision-making.
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Harold Young
10 days agoEric Nguyen
15 days agoSteven Adams
1 month agoEdward Rogers
27 days agoNathan Evans
29 days agoJeffrey Johnson
17 days agoDavid Lee
1 month agoCrystal Turner
21 days agoMaryanne
2 months agoBarabara
2 months agoElly
2 months agoReed
3 months agoFiliberto
3 months agoMy
3 months agoAileen
3 months agoEura
4 months agoYolande
4 months agoKerrie
4 months agoJudy
4 months agoMoira
5 months agoRory
5 months agoCory
5 months agoJosephine
5 months agoDalene
6 months agoBettina
6 months agoYuette
6 months agoSean
6 months agoKimbery
7 months agoLatanya
7 months agoFelice
7 months agoMabel
7 months agoBettina
8 months agoSerita
8 months agoVinnie
8 months agoJoni
8 months agoMilly
9 months agoMaynard
9 months agoTiera
11 months agoHaydee
12 months agoLauna
1 year agoFabiola
1 year agoSherrell
1 year agoJaclyn
1 year agoPatria
1 year agoMarta
1 year agoTammy
1 year agoBarabara
2 years agoAlesia
2 years agoErnest
2 years agoCassie
2 years agoTiffiny
2 years agoArlene
2 years agoMarsha
2 years agoDean
2 years agoShawnna
2 years agoValene
2 years agoAriel
2 years agoGlory
2 years agoCassandra
2 years ago