Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
SAS A00-215 Exam - Topic 3 Question 9 Discussion
Actual exam question for
SAS's
A00-215 exam
Question #: 9
Topic #: 3
[All A00-215 Questions]
Topic #: 3
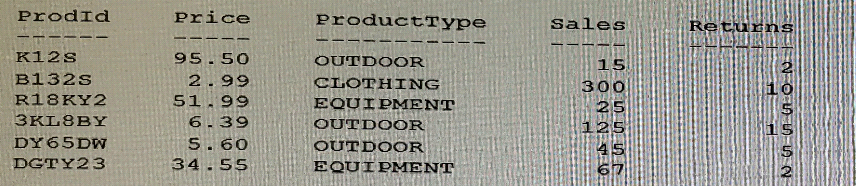
Given the SAS data set WORK PRODUCTS:
The following SAS program is submitted:
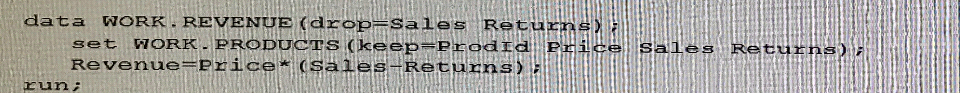
How many variables does the WORK REVENUE data set contains?
Suggested Answer:
D
Juan
6 months agoTegan
6 months agoNicolette
6 months agoCarrol
6 months agoPaz
6 months agoWeldon
7 months agoReita
7 months agoWilliam
7 months agoAnnalee
7 months agoDexter
7 months agoChantay
7 months agoJaime
7 months ago