Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Pegasystems PEGAPCRSA80V1_2019 Exam - Topic 3 Question 29 Discussion
Actual exam question for
Pegasystems's
PEGAPCRSA80V1_2019 exam
Question #: 29
Topic #: 3
[All PEGAPCRSA80V1_2019 Questions]
Topic #: 3
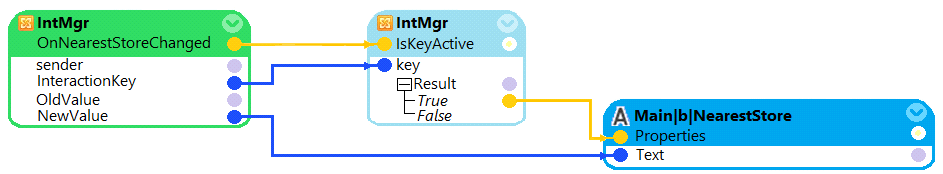
Which two statements are valid for the given automation? (Choose two.)
Suggested Answer:
B, D
Mica
5 months agoElmira
5 months agoHorace
6 months agoSvetlana
6 months agoFlo
6 months agoNaomi
6 months agoDana
6 months agoCheryl
6 months agoRaul
6 months agoLouisa
6 months agoMalinda
6 months agoMozell
6 months agoIrma
6 months ago