Palo Alto Networks CloudSec-Pro Exam Questions
- Topic 1: Security Operations Center (SOC) Fundamentals: This domain covers the foundational components of a SOC, including team roles, tools, and technologies used in day-to-day security operations. It also addresses how AI/ML and threat intelligence support incident response, categorization, and prioritization.
- Topic 2: Cortex Fundamentals: This domain focuses on the core features of the Cortex Cloud platform, including indicator types, log management, asset inventory, compliance, and data protection. It also covers how to create reports and dashboards and how data sources are ingested into the platform.
- Topic 3: Cloud Posture Security: This domain examines the tools and practices used to assess and manage cloud security posture, spanning CSPM, KSPM, AI-SPM, and DSPM. It also covers agentless scanning, identity security, vulnerability management, unified compliance, and the role of Posture Security Management Modules.
- Topic 4: Cloud Runtime Security: This domain addresses the protection of cloud workloads during active operation, covering cloud workload protection, detection and response, web application and API security, and vulnerability management. It also includes the processes involved in deploying and managing security agents.
- Topic 5: Application Security: This domain covers security practices integrated throughout the software development lifecycle, including application security posture management, CI/CD pipeline security, software composition analysis, IaC security, and secrets scanning. It also explores real-world application security use cases and scan management.
Free Palo Alto Networks CloudSec-Pro Exam Actual Questions
Note: Premium Questions for CloudSec-Pro were last updated On May. 24, 2026 (see below)
Given the following audit event activity snippet:
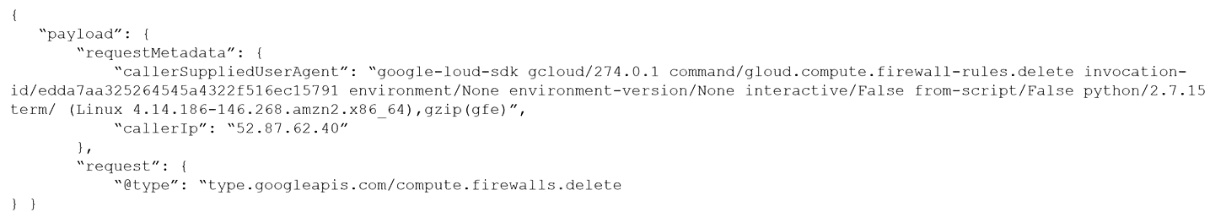
Which RQL will be triggered by the audit event?
A)
B)
C)
D)
Per security requirements, an administrator needs to provide a list of people who are receiving e-mails for Prisma Cloud alerts.
Where can the administrator locate this list of e-mail recipients?
In Prisma Cloud, the list of people who are receiving e-mails for alerts is managed within the configuration of individual Alert Rules.
Option D: Set Alert Notification section within an Alert Rule is where administrators can specify the e-mail recipients for alerts generated by Prisma Cloud. This section allows for the customization of alert notifications, including the selection of recipients who should receive email notifications when an alert is triggered. This granularity ensures that the right stakeholders are informed about specific security incidents or compliance violations, facilitating timely and appropriate responses.
Prisma Cloud Alert Configuration Documentation: Details the process of setting up alert rules in Prisma Cloud, including how to configure notification settings and specify recipients for email alerts.
Alert Management Best Practices: Offers insights into effective alert management strategies, highlighting the importance of targeted alert notifications in ensuring that critical security information reaches the relevant parties promptly.
A customer has a requirement to automatically protect all Lambda functions with runtime protection. What is the process to automatically protect all the Lambda functions?
Automatically protecting all Lambda functions with runtime protection in Prisma Cloud can be achieved by configuring a serverless auto-protect rule. This feature allows for the automatic application of runtime protection policies to all Lambda functions without the need for manual intervention or embedding defenders in each function. The auto-protect rule ensures that as new Lambda functions are deployed, they are automatically protected based on the predefined security policies, maintaining a consistent security posture across all serverless functions.
This approach leverages the capabilities of Prisma Cloud to integrate seamlessly with serverless architectures, providing a layer of security that is both comprehensive and adaptive to the dynamic nature of serverless computing. By automating the protection process, organizations can ensure that their serverless functions are always covered by the latest security policies, reducing the risk of vulnerabilities and attacks.
Which ban for DoS protection will enforce a rate limit for users who are unable to post five (5) ''. tar.gz" files within five (5) seconds?
In the context of DoS protection, enforcing a rate limit is a common strategy to prevent abuse and ensure service availability. The scenario described involves limiting the rate at which users can post '.tar.gz' files to five within five seconds. The correct ban configuration for this requirement would be one that specifies an average rate of 5 with a file extension match on ''.tar.gz' within the Web Application and API Security (WAAS) component of a security solution like Prisma Cloud. WAAS is designed to protect web applications and APIs from various threats, including DoS attacks, by applying policies that can limit actions based on specific criteria, such as file types and request rates. This configuration ensures that any attempt to upload more than five '.tar.gz' files within a five-second window would be detected and blocked, mitigating the risk of DoS attacks targeting this particular file upload functionality.
In which Console menu would an administrator verify whether a custom compliance check is failing or passing?
In Prisma Cloud, the 'Monitor > Compliance' menu is the centralized location where administrators can verify the status of custom compliance checks, along with predefined compliance standards and frameworks. This section provides a comprehensive view of the organization's compliance posture, displaying whether specific compliance checks are passing or failing. It allows for detailed insights into compliance status across cloud environments, helping administrators identify areas of non-compliance, understand the reasons behind compliance failures, and take corrective actions to address any identified issues.
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Linda Williams
3 days agoFrank Bailey
11 days agoKevin Gonzalez
27 days agoAdam Campbell
1 month agoKevin Clark
1 month agoJennifer Smith
25 days agoStephen Hill
1 month agoAmy Sanchez
19 days agoElizabeth Green
16 days agoBrynn
2 months agoNoel
2 months agoAngelica
2 months agoLonny
3 months agoValentin
3 months agoElli
3 months agoJosephine
3 months ago