Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Nokia 4A0-C04 Exam - Topic 1 Question 23 Discussion
Actual exam question for
Nokia's
4A0-C04 exam
Question #: 23
Topic #: 1
[All 4A0-C04 Questions]
Topic #: 1
Click the exhibit.
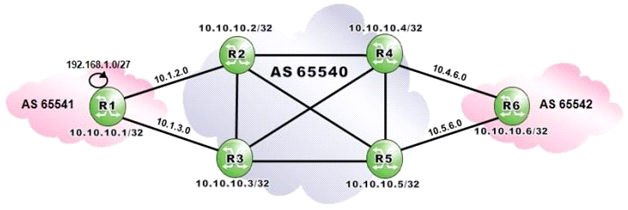
AS 65540 routers are iBGP fully-meshed. Assume routers R4, R5 and R6 are configured with addpaths ipv4 send 2 receive". Which routes to 192.168.0.1/27 is router R6 expected to have in its BGP routing table?
Suggested Answer:
D
Paola
5 months agoLoren
6 months agoRebecka
6 months agoStephanie
6 months agoMacy
6 months agoCarli
6 months agoKate
6 months agoEladia
6 months agoAilene
6 months agoTish
7 months agoLong
7 months agoMattie
7 months agoTracey
7 months agoAimee
7 months ago