Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Nokia 4A0-105 Exam - Topic 5 Question 1 Discussion
Actual exam question for
Nokia's
4A0-105 exam
Question #: 1
Topic #: 5
[All 4A0-105 Questions]
Topic #: 5
Click on the exhibit below.
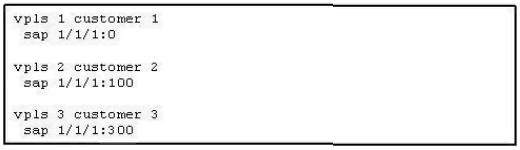
The following VPLS services and SAPs have been configured. Which of the following statements is true?
Suggested Answer:
E
Belen
6 months agoLeonora
6 months agoGlendora
6 months agoEttie
6 months agoAllene
7 months agoNarcisa
7 months agoMirta
7 months agoAndree
7 months agoMarguerita
7 months agoLaurel
7 months agoYvette
7 months agoArlyne
7 months agoJustine
7 months agoAlexis
7 months ago