Microsoft AZ-104 Exam Questions
Free Microsoft AZ-104 Exam Actual Questions
Note: Premium Questions for AZ-104 were last updated On May. 01, 2026 (see below)
You have an Azure subscription that contains the resources shown in the following table.
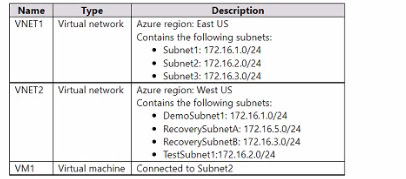
You configure Azure Site Recovery to replicate VM1 between the East US and Wt US regions.
You perform a test failove of VM1 and specify VNET2 as the target v>riual network.
When the test version of VM1 is created, to which subnet will the virtual machine be connected?
https://learn.microsoft.com/en-us/azure/site-recovery/azure-to-azure-network-mapping
The subnet of the target VM is selected based on the name of the subnet of the source VM.
- If a subnet with the same name as the source VM subnet is available in the target network, that subnet is set for the target VM.
- If a subnet with the same name doesn't exist in the target network, the first subnet in the alphabetical order is set as the target subnet.
You have an Azure subscription named Subscription1 that is used be several departments at your company. Subscription1 contains the resources in the following table:

Another administrator deploys a virtual machine named VM1 and an Azure Storage account named Storage2 by using a single Azure Resource Manager template.
You need to view the template used for the deployment.
From which blade can you view the template that was used for the deployment?
1. View template from deployment history
Go to the resource group for your new resource group. Notice that the portal shows the result of the last deployment. Select this link.

2. You see a history of deployments for the group. In your case, the portal probably lists only one deployment. Select this deployment.
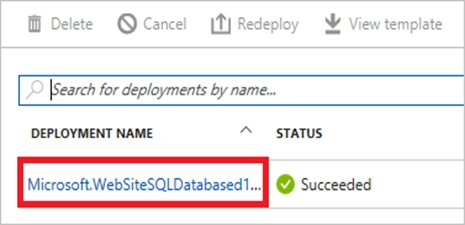
The portal displays a summary of the deployment. The summary includes the status of the deployment and its operations and the values that you provided for parameters. To see the template that you used for the deployment, select View template.

You have an Azure subscription named Subscription1.
You have 5 TB of data that you need to transfer to Subscription1.
You plan to use an Azure Import/Export job.
What can you use as the destination of the imported data?
Azure Import/Export service is used to securely import large amounts of data to Azure Blob storage and Azure Files by shipping disk drives to an Azure datacenter.
The maximum size of an Azure Files Resource of a file share is 5 TB.
https://docs.microsoft.com/en-us/azure/storage/common/storage-import-export-service
You have an Azure subscription named Subscription1 that contains a virtual network named VNet1. VNet1 is in a resource group named RG1.
Subscription1 has a user named User1. User1 has the following roles;
* Reader
* Security Admin
* Security Reader
You need to ensure that User1 can assign the Reader role for VNet1 to other users. What should you do?
https://docs.microsoft.com/en-us/azure/role-based-access-control/rbac-and-directory-admin-roles#:~:text=The%20User%20Access%20Administrator%20role%20enables%20the%20user%20to%20grant,Azure%20subscriptions%20and%20management%20groups.
You have an Azure subscription that contains 10 virtual networks. The virtual networks are hosted in separate resource groups.
Another administrator plans to create several network security groups (NSGs) in the subscription.
You need to ensure that when an NSG is created, it automatically blocks TCP port 8080 between the virtual networks.
Solution: You configure a custom policy definition, and then you assign the Azure policy to the subscription.
Does this meet the goal?
In Azure, Azure Policy is a governance tool used to enforce organizational standards and assess compliance across Azure resources. It allows administrators to define and assign policy definitions that automatically audit, deny, or modify resource configurations at deployment or runtime.
In this scenario, the requirement is that every time a Network Security Group (NSG) is created, it should automatically contain a rule that blocks TCP port 8080 traffic between virtual networks.
The Microsoft Azure Policy documentation confirms that you can create a custom policy definition using the Microsoft.Network/networkSecurityGroups/securityRules resource type. Within the policy's JSON definition, you can specify conditions such as:
The resource type to which the policy applies (networkSecurityGroups).
The enforcement mode (deny or deployIfNotExists).
The required configuration, such as a specific inbound or outbound rule (in this case, a rule denying TCP 8080).
By using the DeployIfNotExists effect in the policy, Azure automatically ensures that the NSG includes the required rule. If the rule does not exist, Azure deploys it automatically during resource creation.
Assigning this custom policy definition at the subscription level ensures it is inherited by all resource groups and applies to all virtual networks created in that subscription. This meets the goal because the requirement is to enforce a security configuration across all NSGs, regardless of which resource group or virtual network they belong to.
Therefore, configuring and assigning a custom Azure Policy to the subscription fully satisfies the requirement.
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Brenda Wilson
11 days agoCrystal Hall
5 days agoMichael Nguyen
8 days agoGerald Allen
1 day agoLinda Baker
8 days agoDennis Flores
8 days agoDaniel
1 month agoLashandra
1 month agoJulio
2 months agoJolene
2 months agoOzell
2 months agoLaurena
2 months agoEric
3 months agoCarole
3 months agoKimbery
3 months agoGeoffrey
3 months agoCarman
3 months agoElza
4 months agoCristy
4 months agoStevie
4 months agoMagdalene
4 months agoNadine
5 months agoJustine
5 months agoDerrick
5 months agoStephen
5 months agoPolly
6 months agoLizbeth
6 months agoNobuko
6 months agoJannette
6 months agoNicolette
7 months agoGaynell
7 months agoStefania
7 months agoHuey
7 months agoRanee
7 months agoOmega
8 months agoLuis
8 months agoSonia
8 months agoJanna
10 months agoAlyce
10 months agoMauricio
10 months agoLaine
11 months agoJohnna
1 year agoMicaela
1 year agoBettina
1 year agoDorsey
1 year agoStephanie
1 year agoHoward
1 year agoDonette
1 year agoBritt
1 year agoMicaela
1 year agoMireya
1 year agoDeandrea
1 year agoKenneth
1 year agoLashon
1 year agoCecil
1 year agoIola
1 year agoRebecka
1 year agoRhea
1 year agoDesiree
1 year agoChuck
1 year agoGail
1 year agoTerry
2 years agoCorrinne
2 years agoGwenn
2 years agoGianna
2 years agoEmogene
2 years agoJuliana
2 years agoAja
2 years agoLindsey
2 years agoDevorah
2 years agoFelix
2 years agoCiara
2 years agoRessie
2 years agoOretha
2 years agoAdelaide
2 years agoMari
2 years agoLetha
2 years agoalizabeth
2 years agoMark james
2 years agoJAZZY
2 years agolivingston
2 years agohamim
2 years agopelvis
2 years agosijag
2 years agogarey
2 years ago