Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Microsoft AZ-500 Exam - Topic 10 Question 29 Discussion
Actual exam question for
Microsoft's
AZ-500 exam
Question #: 29
Topic #: 10
[All AZ-500 Questions]
Topic #: 10
You have an Azure subscription that contains an Azure key vault. The role assignments for the key vault are shown in the following exhibit.
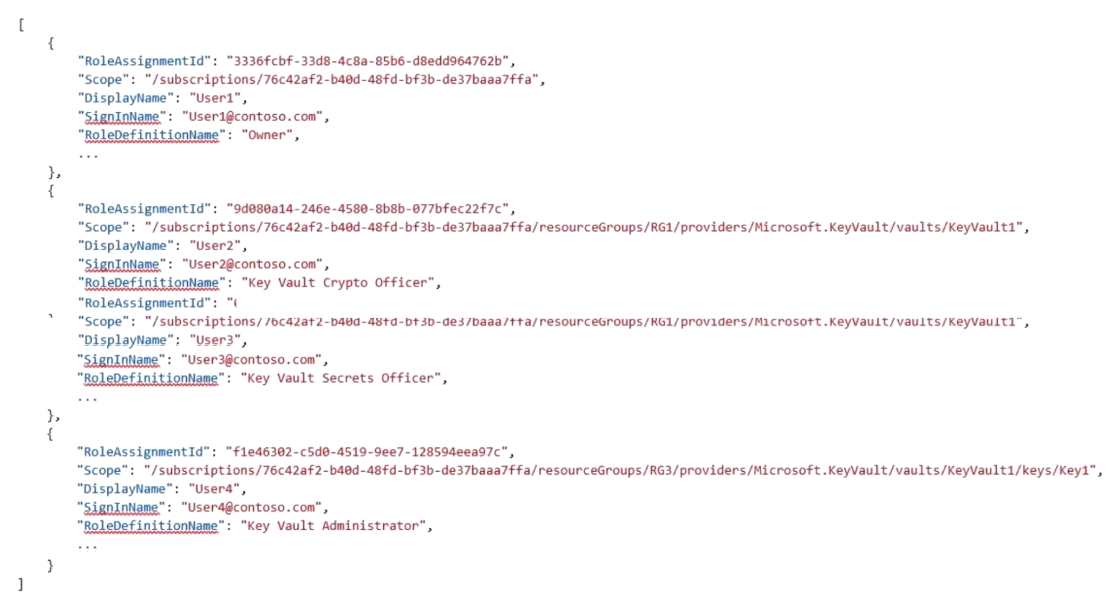
Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic. NOTE: Each correct selection is worth one point.
Suggested Answer:
A
Elenore
5 months agoParis
6 months agoGenevive
6 months agoGenevieve
6 months agoLina
6 months agoLeonor
6 months agoUna
6 months agoKris
6 months agoLenna
7 months agoCaren
7 months agoYoulanda
7 months agoGearldine
7 months agoDominga
7 months ago