Juniper JN0-106 Exam Questions
- Topic 1: Networking Fundamentals: Covers core networking concepts including IP addressing, subnetting, Layer 2/3 operations, routing basics, and protocol types essential for understanding how networks function.
- Topic 2: Junos OS Fundamentals: Covers the architecture of Junos OS, focusing on the separation of control and forwarding planes and how traffic is processed by the routing and packet-forwarding engines.
- Topic 3: User Interfaces: Covers how to navigate and use the Junos CLI and J-Web interface, including configuration management, output filtering, and working with active versus candidate configurations.
- Topic 4: Configuration Basics: Covers the essential steps for configuring a Junos device from factory default, including user accounts, interfaces, authentication, system services like NTP and SNMP, and configuration archival.
- Topic 5: Operational Monitoring and Maintenance: Covers the tools and procedures used to monitor, maintain, and troubleshoot Junos devices, including show/monitor commands, network utilities, OS upgrades, and password recovery.
- Topic 6: Routing Fundamentals: Covers core routing concepts on Junos devices, including routing and forwarding tables, route preference, static routing, routing instances, and an introduction to dynamic routing protocols.
- Topic 7: Routing Policy and Firewall Filters: Covers how to control traffic flow on Junos devices using routing policies and firewall filters, including policy structure, match criteria, filter actions, and unicast RPF.
Free Juniper JN0-106 Exam Actual Questions
Note: Premium Questions for JN0-106 were last updated On May. 11, 2026 (see below)
Junos device and are configuring the system-related settings. You must configure this device for the current date and time on the US West coast. You have set the time zone to America/LosAngeles, however the time and date did not change. In this scenario, which two additional actions would satisfy this requirement? (Choose two.)
In Junos OS, configuring the time-zone (such as America/LosAngeles) within the [edit system] hierarchy establishes the offset from Coordinated Universal Time (UTC) and governs how the device displays timestamps for logs and system events. However, simply setting the timezone does not adjust the underlying system hardware clock; it only dictates how that clock's data is interpreted and presented. To ensure the device reflects the correct local time, the administrator must either synchronize the system with an external reference or manually input the current date and time.
Configuring a Network Time Protocol (NTP) server is the preferred professional method, as it allows the device to automatically synchronize its clock with a reliable stratum source, ensuring long-term accuracy and consistency across the network. Alternatively, the set date operational mode command can be used to manually define the current year, month, day, hour, and minute. While a DNS server is necessary for resolving the hostnames of NTP servers, it does not provide time data itself. Furthermore, rebooting the device will not correct a fundamentally unset or drifting clock. Therefore, combining the correct timezone with either NTP synchronization or a manual date setting is the standard procedure for establishing temporal accuracy on a Junos platform. Reference: Operational Monitoring and Maintenance, System Time and NTP.
Exhibit:
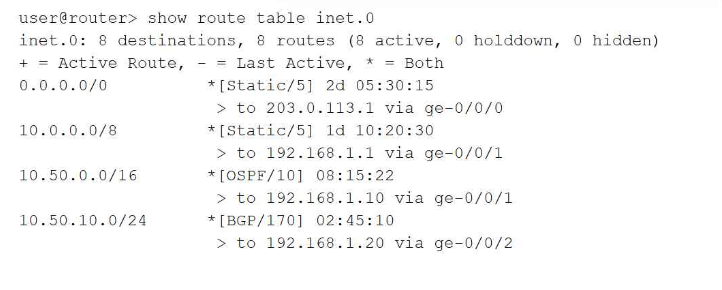
Referring to the exhibit, which route will be selected for a packet destined to IP address 10.50.10.55?
In Junos OS, the Routing Information Base (RIB) selection process follows a strict hierarchy where the Longest Prefix Match (LPM) is the absolute primary tie-breaker. When a packet is destined for 10.50.10.55, the Routing Engine searches the inet.0 table for all matching entries. In this exhibit, four routes match: the default route (0.0.0.0/0), a general static route (10.0.0.0/8), an OSPF route (10.50.0.0/16), and a BGP route (10.50.10.0/24).
The LPM rule dictates that the router must select the most specific route available, which is defined as the entry with the highest number of matching bits in the subnet mask. The 10.50.10.0/24 route matches 24 bits of the destination address, making it more specific than the 16-bit, 8-bit, or 0-bit alternatives. It is critical to understand that route preference (e.g., Static at 5, OSPF at 10, or BGP at 170) is only evaluated if there are multiple paths to the exact same prefix and length. Because these prefixes vary in length, the length takes precedence over the protocol preference. Therefore, the BGP-learned route via 192.168.1.20 is selected as the active path, ensuring traffic follows the most granular routing information provided to the device. Reference: Routing Fundamentals, Routing Table Selection, Longest Prefix Match.
You want to redeploy a Junos device by clearing the existing configuration and resetting it to factory defaults. In this scenario, which command would help to accomplish this task?
When a network architect needs to completely sanitize a Junos device for redeployment or decommissioning, the request system zeroize command is the most thorough tool available. Unlike simply loading the factory default configuration, which only resets the configuration database, the zeroize command performs a deep wipe of the system.
Specifically, this command removes all user-created data, including all configuration files (active and rollback), log files, license keys, and any locally stored files in the /var/tmp or /home directories. It essentially restores the device to its 'pristine' out-of-box state. Once the command is initiated, the device reboots and goes through a sanitization process. This is a critical security measure to ensure that sensitive information---such as encrypted passwords, proprietary routing policies, or SNMP community strings---does not leave the organization when hardware is transferred.
In contrast, the request system storage cleanup command is a maintenance utility used to delete temporary files and old log entries to free up disk space, but it does not affect the running configuration or user accounts. Therefore, for a total system reset that includes configuration deletion, zeroize is the mandatory operational command.
Which interface type prefix represents a 10-Gigabit Ethernet interface?
In Junos OS, the naming convention for physical interfaces is highly structured, providing immediate information regarding the media type, hardware location, and port number. The prefix of an interface name is a two-letter or three-letter code that identifies the speed and physical transmission characteristics of the interface. For 10-Gigabit Ethernet (GbE) interfaces, the correct prefix is xe. This prefix is a standard identifier across Junos platforms, regardless of whether the interface is fixed or modular.
Understanding these prefixes is essential for navigating the Junos configuration hierarchy and performing operational monitoring. For comparison, other common prefixes include fe for Fast Ethernet (10/100 Mbps), ge for Gigabit Ethernet (1 Gbps), and et for higher-speed interfaces such as 40-GbE or 100-GbE. When an administrator views the output of commands like show interfaces terse, identifying the xe prefix allows for the quick verification of high-bandwidth links within the network fabric. This standardized nomenclature ensures consistency across different hardware families, such as the EX, MX, and QFX series, facilitating easier management and troubleshooting for network architects. This concludes the provided set of questions from the Junos Associate (JNCIA-Junos) curriculum. Reference: Junos OS Fundamentals, Interface Naming Conventions.
Which two statements about firewall filters are correct? (Choose two.)
In Junos OS, standard firewall filters operate as a primary security and traffic management tool within the forwarding plane. These filters are fundamentally stateless, meaning they evaluate each packet individually and in isolation without maintaining a session table or tracking the state of network connections. This stateless nature allows the Packet Forwarding Engine (PFE) to process filters at hardware speeds, ensuring minimal latency for transit traffic. This distinguishes them from the stateful security policies found on Junos security devices like the SRX Series, which track the entire lifecycle of a flow.
Furthermore, firewall filters are designed to inspect and match header information up to Layer 4 of the OSI model. This capability allows administrators to define terms based on parameters such as source and destination IP addresses (Layer 3) as well as TCP or UDP port numbers and protocol types (Layer 4). While they provide granular control over packet flow, they do not natively inspect Layer 7 application payloads, which is typically reserved for advanced services like Intrusion Detection and Prevention (IDP). By combining stateless execution with Layer 4 matching, Junos firewall filters provide an efficient method for implementing transit protection, rate limiting through policing, and protecting the local Routing Engine through loopback interface filtering. Reference: Routing Policy and Firewall Filters, Firewall Filter Framework.
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Currently there are no comments in this discussion, be the first to comment!