ISC2 ISSMP Exam Questions
- Topic 1: Leadership and Organizational Management: Covers establishing and managing the security program's strategic direction, governance structures, and leadership responsibilities across the organization.
- Topic 2: Systems Lifecycle Management: Focuses on integrating security throughout the entire lifecycle of systems, from design and development to deployment, operation, and decommissioning.
- Topic 3: Risk Management: Addresses identifying, assessing, and treating security risks to ensure informed decision-making and protection of organizational assets.
- Topic 4: Security Operations: Encompasses the day-to-day management and oversight of security controls, monitoring, and operational processes to maintain a secure environment.
- Topic 5: Contingency Management: Covers planning, developing, and maintaining business continuity and disaster recovery strategies to ensure organizational resilience during disruptions.
- Topic 6: Law, Ethics, and Security Compliance Management: Addresses adherence to relevant laws, regulations, ethical standards, and compliance frameworks that govern information security practices.
Free ISC2 ISSMP Exam Actual Questions
Note: Premium Questions for ISSMP were last updated On May. 22, 2026 (see below)
You are the project manager of the GHE Project. You have identified the following risks with the characteristics as shown in the following figure:
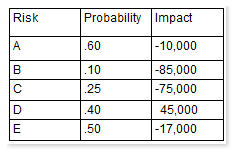
How much capital should the project set aside for the risk contingency reserve?
Which of the following statements is related with the second law of OPSEC?
Which of the following models uses a directed graph to specify the rights that a subject can transfer to an object or that a subject can take from another subject?
In which of the following contract types, the seller is reimbursed for all allowable costs for performing the contract work and receives a fixed fee payment which is calculated as a percentage of the initial estimated project costs?
Which of the following are the process steps of OPSEC? Each correct answer represents a part of the solution. Choose all that apply.
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Lisa Lee
3 days agoBrian Roberts
25 days agoCynthia Williams
1 month agoSandra Walker
1 month agoJoshua Young
1 month agoTimothy Collins
22 days agoSharon Lewis
1 month agoChristopher Roberts
1 month agoDenae
2 months agoDalene
2 months agoKent
2 months agoMeaghan
3 months agoAracelis
3 months agoElise
3 months agoAn
3 months agoNathalie
4 months agoMelissia
4 months agoVeronica
4 months agoStefan
4 months agoCathrine
5 months agoJaleesa
5 months agoKerry
5 months agoMalcolm
5 months agoAshlyn
6 months agoTyisha
6 months agoDorothy
6 months agoKristel
6 months agoTheola
7 months agoGail
7 months agoStephaine
7 months agoFernanda
7 months agoVincent
8 months agoLeota
8 months agoHerman
8 months agoSalena
8 months agoHoa
9 months agoFidelia
9 months agoAlfred
11 months agoGeorgene
11 months agoMireya
11 months agoVerdell
12 months agoFranchesca
1 year agoJacklyn
1 year agoThaddeus
1 year agoKami
1 year agoLauran
1 year agoDoretha
1 year agoLeana
1 year agoTiara
1 year agoUla
1 year agoCathrine
1 year agoYuki
1 year agoRoxane
1 year agoTalia
1 year agoLaquita
1 year agoLashon
1 year agoHuey
1 year agoTamar
1 year agoEden
2 years agoMabel
2 years agoSylvie
2 years agoTamekia
2 years agoCamellia
2 years agoBarabara
2 years agoRia
2 years agoLashawna
2 years agoWhitley
2 years agoZena
2 years agoAlesia
2 years agoArthur
2 years agoJohnna
2 years agoRemedios
2 years agoRupert
2 years agoMi
2 years agoErick
2 years agoKattie
2 years agoMickie
2 years agoAimee
2 years agoGregoria
2 years agoVeronika
2 years ago