Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
HPE6-A78 Exam - Topic 9 Question 25 Discussion
Actual exam question for
HP's
HPE6-A78 exam
Question #: 25
Topic #: 9
[All HPE6-A78 Questions]
Topic #: 9
Refer to the exhibit.
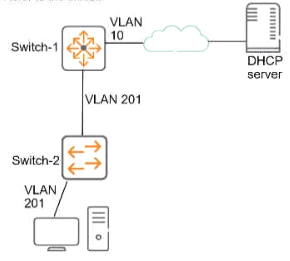
This company has ArubaOS-Switches. The exhibit shows one access layer switch, Swllcn-2. as an example, but the campus actually has more switches. The company wants to slop any internal users from exploiting ARP
What Is the proper way to configure the switches to meet these requirements?
Suggested Answer:
D
Brice
5 months agoCassandra
6 months agoEden
6 months agoLeota
6 months agoLorrine
6 months agoBev
6 months agoVi
6 months agoLouisa
6 months agoAlaine
6 months agoClare
7 months agoWerner
7 months agoStefan
7 months agoChanel
7 months agoIsidra
7 months ago