Google Professional Security Operations Engineer Exam Questions
Free Google Professional Security Operations Engineer Exam Actual Questions
Note: Premium Questions for Professional Security Operations Engineer were last updated On May. 28, 2026 (see below)
Your organization has recently onboarded to Google Cloud with Security Command Center Enterprise (SCCE) and is now integrating it with your organization's SOC. You want to automate the response process within SCCE and integrate with the existing SOC ticketing system. You want to use the most efficient solution. How should you implement this functionality?
Comprehensive and Detailed Explanation
The correct answer is Option C. The prompt asks for the most efficient and automated solution for handling SCCE findings and integrating with a ticketing system. This is the primary use case for Google Security Operations SOAR.
The native workflow is as follows:
SCCE detects a finding.
The finding is automatically ingested into Google SecOps SIEM, which creates an alert.
The alert is automatically sent to SecOps SOAR, which creates a case.
The SOAR case automatically triggers a playbook.
Option C describes this process perfectly. An administrator would disable the default playbook and enable a specific playbook that uses a pre-built integration (from the Marketplace) for the organization's ticketing system (e.g., ServiceNow, Jira). This playbook would contain an automated step to generate a ticket, thus fulfilling the requirement efficiently.
Option B is a manual process. Options A and D describe complex, custom-built data engineering pipelines, which are far less efficient than using the built-in SOAR capabilities.
Exact Extract from Google Security Operations Documents:
SOAR Playbooks and Integrations: Google SecOps SOAR is designed to automate and orchestrate responses to alerts. When an alert from a source like Security Command Center (SCC) is ingested and creates a case, it can be configured to automatically trigger a playbook.
Ticketing Integration: A common playbook use case is integration with an external ticketing system. Using a pre-built integration from the SOAR Marketplace, an administrator can add a step to the playbook (e.g., Create Ticket). This action will automatically generate a ticket in the external system and populate it with details from the alert, such as the finding, the affected resources, and the recommended remediation steps. This provides a seamless, automated workflow from detection to ticketing.
Google Cloud Documentation: Google Security Operations > Documentation > SOAR > Use cases > Case Management
Google Cloud Documentation: Google Security Operations > Documentation > SOAR > Marketplace integrations
You are implementing Google Security Operations (SecOps) for your organization. Your organization has their own threat intelligence feed that has been ingested to Google SecOps by using a native integration with a Malware Information Sharing Platform (MISP). You are working on the following detection rule to leverage the command and control (C2) indicators that were ingested into the entity graph.
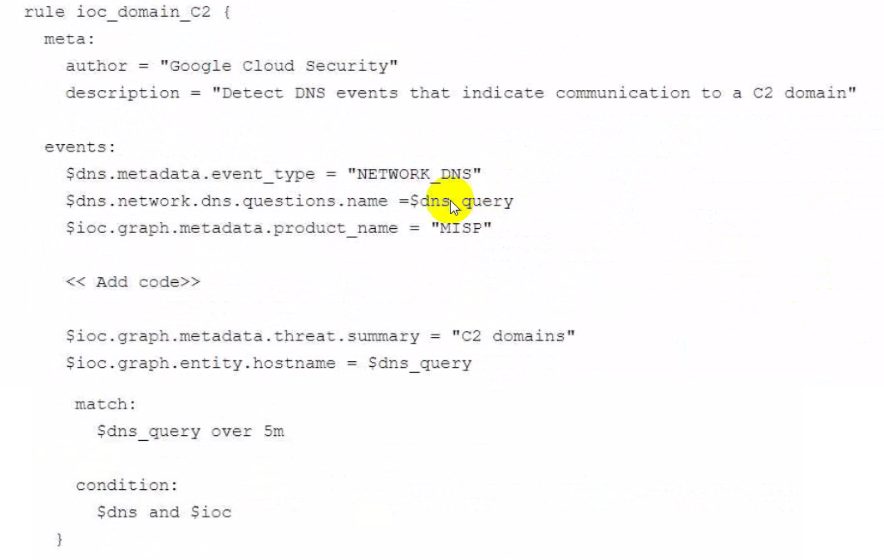
What code should you add in the detection rule to filter for the domain IOCS?
This YARA-L rule is designed to correlate a real-time event (a DNS query, $dns) with known-bad indicators stored in the Google SecOps entity graph ($ioc). The code must correctly filter the entity graph to find the specific indicators from the custom MISP feed.
Two filters are required:
$ioc.graph.metadata.entity_type = 'DOMAIN_NAME': This line is essential to filter the entity graph for IoCs that are domains. The rule is trying to match a DNS query ($dns_query) to a known C2 domain, so the entity type must be DOMAIN_NAME.
$ioc.graph.metadata.source_type = 'ENTITY_CONTEXT': This is the key differentiator. The Google SecOps entity graph has multiple context sources. GLOBAL_CONTEXT (Option B) is for threat intelligence provided by Google (e.g., Google Threat Intelligence, Mandiant). DERIVED_CONTEXT (Option C) is for context inferred from UDM events. The prompt explicitly states the IoC feed is the organization's own 'threat intelligence feed... ingested... with... MISP.' This type of customer-provided, third-party intelligence is classified as ENTITY_CONTEXT. Adding this line ensures the rule only uses the custom MISP feed for its IoC data, as intended.
The other lines in the $ioc block, such as product_name = 'MISP', further refine this ENTITY_CONTEXT search.
(Reference: Google Cloud documentation, 'YARA-L 2.0 language syntax'; 'Context-aware detections with entity graph'; 'Populate the entity graph')
You are an incident responder at your organization using Google Security Operations (SecOps) for monitoring and investigation. You discover that a critical production server, which handles financial transactions, shows signs of unauthorized file changes and network scanning from a suspicious IP address. You suspect that persistence mechanisms may have been installed. You need to use Google SecOps to immediately contain the threat while ensuring that forensic data remains available for investigation. What should you do first?
Comprehensive and Detailed Explanation
The correct answer is Option C. The prompt specifies two critical, simultaneous requirements: immediate containment and preservation of forensic data.
Immediate Containment: The server is actively scanning the network, so it must be taken offline to prevent lateral movement and further compromise.
Forensic Preservation: The suspicion of persistence mechanisms means a full investigation is required. This investigation relies on volatile data (running processes, memory, active network connections) that must not be destroyed.
Option C is the only action that satisfies both requirements. Using a Google SecOps SOAR playbook to trigger the EDR integration's 'quarantine' action instructs the EDR agent on the server to block all its network connections. This immediately contains the threat. However, the server itself remains running, which preserves all volatile forensic data for the investigation.
Option B (reboot) is incorrect because it is an eradication step that would destroy all volatile forensic evidence. Options A and D are incomplete containment or investigation steps that do not fully isolate the compromised host.
Exact Extract from Google Security Operations Documents:
Incident Response and Containment: When a critical asset is compromised, the first priority is containment. Google SecOps SOAR playbooks integrate with Endpoint Detection and Response (EDR) tools to automate this step.
EDR Integration Actions: The most common containment action is 'Quarantine Host' or 'Isolate Asset.' This action instructs the EDR agent on the endpoint to block all network communications, effectively isolating it from the rest of the network. This step immediately stops the threat from spreading or communicating with a C2 server. A key benefit of this approach, as opposed to a shutdown or reboot, is that the host remains powered on, which preserves volatile memory and process data for forensic investigation.
Google Cloud Documentation: Google Security Operations > Documentation > SOAR > Playbooks > Playbook Actions
Google Cloud Documentation: Google Security Operations > Documentation > SOAR > Marketplace integrations > (e.g., CrowdStrike, SentinelOne, Microsoft Defender)
Your organization has recently onboarded to Google Cloud with Security Command Center Enterprise (SCCE) and is now integrating it with your organization's SOC. You want to automate the response process within SCCE and integrate with the existing SOC ticketing system. You want to use the most efficient solution. How should you implement this functionality?
Comprehensive and Detailed Explanation
The correct answer is Option C. The prompt asks for the most efficient and automated solution for handling SCCE findings and integrating with a ticketing system. This is the primary use case for Google Security Operations SOAR.
The native workflow is as follows:
SCCE detects a finding.
The finding is automatically ingested into Google SecOps SIEM, which creates an alert.
The alert is automatically sent to SecOps SOAR, which creates a case.
The SOAR case automatically triggers a playbook.
Option C describes this process perfectly. An administrator would disable the default playbook and enable a specific playbook that uses a pre-built integration (from the Marketplace) for the organization's ticketing system (e.g., ServiceNow, Jira). This playbook would contain an automated step to generate a ticket, thus fulfilling the requirement efficiently.
Option B is a manual process. Options A and D describe complex, custom-built data engineering pipelines, which are far less efficient than using the built-in SOAR capabilities.
Exact Extract from Google Security Operations Documents:
SOAR Playbooks and Integrations: Google SecOps SOAR is designed to automate and orchestrate responses to alerts. When an alert from a source like Security Command Center (SCC) is ingested and creates a case, it can be configured to automatically trigger a playbook.
Ticketing Integration: A common playbook use case is integration with an external ticketing system. Using a pre-built integration from the SOAR Marketplace, an administrator can add a step to the playbook (e.g., Create Ticket). This action will automatically generate a ticket in the external system and populate it with details from the alert, such as the finding, the affected resources, and the recommended remediation steps. This provides a seamless, automated workflow from detection to ticketing.
Google Cloud Documentation: Google Security Operations > Documentation > SOAR > Use cases > Case Management
Google Cloud Documentation: Google Security Operations > Documentation > SOAR > Marketplace integrations
You are responsible for identifying suspicious activity and security events in your organization's environment. You discover that some detection rules are generating false positives when the principal.ip field contains one or more IP addresses in the 192.168.2.0/24 subnet. You want to improve these detection rules using the principal.ip repeated field. What should you add to the YARA-L detection rules?
Comprehensive and Detailed Explanation
The correct solution is Option D. The goal is to exclude events (i.e., stop false positives) when the principal.ip field contains any IP from the trusted 192.168.2.0/24 subnet.
The principal.ip field in UDM is a repeated field, meaning it can hold an array of values (e.g., ['1.2.3.4', '192.168.2.5']). YARA-L provides the any and all quantifiers to handle repeated fields.9
any $e.principal.ip: This checks if at least one IP in the array meets the condition.
all $e.principal.ip: This checks if every IP in the array meets the condition.
The function net.ip_in_range_cidr(...) returns true if an IP is in the specified range.
Therefore, the logic we need is: 'do not trigger this rule if any of the IPs in the principal.ip field are in the 192.168.2.0/24 range.'
This translates directly to the YARA-L syntax: not net.ip_in_range_cidr(any $e.principal.ip, '192.168.2.0/24')
Option B would only find events from that subnet.
Option A would only find events where all associated IPs are in that subnet.
Option C is the logical inverse of A and would incorrectly filter out events that might be malicious (e.g., ['1.2.3.4', '192.168.2.5'] would not be excluded because all IPs are not in the range).
Exact Extract from Google Security Operations Documents:
YARA-L 2.0 language syntax > Repeated fields and boolean expressions: When a boolean expression, such as a function call, is applied to a repeated field, you can use the any or all keywords to specify how the expression should be evaluated.10
any <repeated_field>: The expression evaluates to true if it is true for at least one of the values in the repeated field.
all <repeated_field>: The expression evaluates to true only if it is true for all of the values in the repeated field.
Functions > net.ip_in_range_cidr: The net.ip_in_range_cidr function is useful to bind rules to specific parts of the network.11 To exclude all private netblocks as defined in RFC1918, you can add a not to the start of the criteria:
and not (net.ip_in_range_cidr(any $e.principal.ip, '10.0.0.0/8') or net.ip_in_range_cidr(any $e.principal.ip, '172.16.0.0/12') or net.ip_in_range_cidr(any $e.principal.ip, '192.168.0.0/16'))
Google Cloud Documentation: Google Security Operations > Documentation > Detections > YARA-L 2.0 language syntax
Google Cloud Documentation: Google Security Operations > Documentation > Detections > YARA-L 2.0 functions > net.ip_in_range_cidr
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Carol Flores
5 days agoCharles Cooper
14 days agoSusan Anderson
29 days agoDennis Campbell
1 month agoBetty Davis
1 month agoMark Johnson
20 days agoDaniel Perez
18 days agoElizabeth Morgan
1 month agoLisa Hill
25 days agoVerona
2 months agoAlberto
2 months agoCarma
3 months agoFelix
3 months agoDyan
3 months agoKirk
3 months agoMaybelle
4 months agoHelaine
4 months agoStacey
4 months agoMitsue
4 months agoRaymon
5 months agoRene
5 months agoTyisha
5 months agoSage
5 months agoAudrie
6 months agoVincenza
6 months agoKrystina
6 months agoKristel
6 months agoGussie
7 months agoJuliann
7 months agoCasey
7 months agoJean
7 months agoMelita
7 months ago