Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Google Professional Cloud Developer Exam - Topic 7 Question 60 Discussion
Actual exam question for
Google's
Professional Cloud Developer exam
Question #: 60
Topic #: 7
[All Professional Cloud Developer Questions]
Topic #: 7
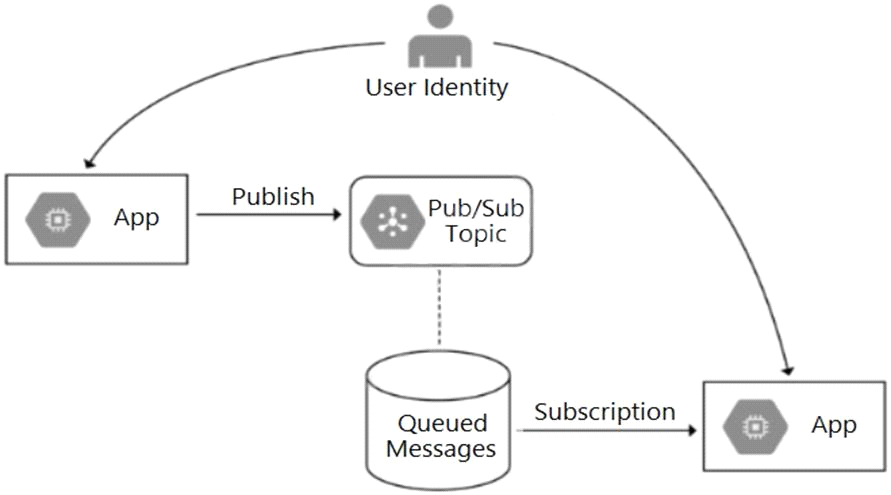
Your team is developing an application in Google Cloud that executes with user identities maintained by Cloud Identity. Each of your application's users will have an associated Pub/Sub topic to which messages are published, and a Pub/Sub subscription where the same user will retrieve published messages. You need to ensure that only authorized users can publish and subscribe to their own specific Pub/Sub topic and subscription. What should you do?
Suggested Answer:
C
Ettie
5 months agoChandra
5 months agoStevie
6 months agoTy
6 months agoChaya
6 months agoRobt
6 months agoLeatha
6 months agoClaudio
6 months agoTashia
6 months agoKati
6 months agoMalinda
6 months agoGraham
6 months agoBelen
6 months ago