Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Google Professional Cloud Developer Exam - Topic 6 Question 44 Discussion
Actual exam question for
Google's
Professional Cloud Developer exam
Question #: 44
Topic #: 6
[All Professional Cloud Developer Questions]
Topic #: 6
You have deployed an HTTP(s) Load Balancer with the gcloud commands shown below.
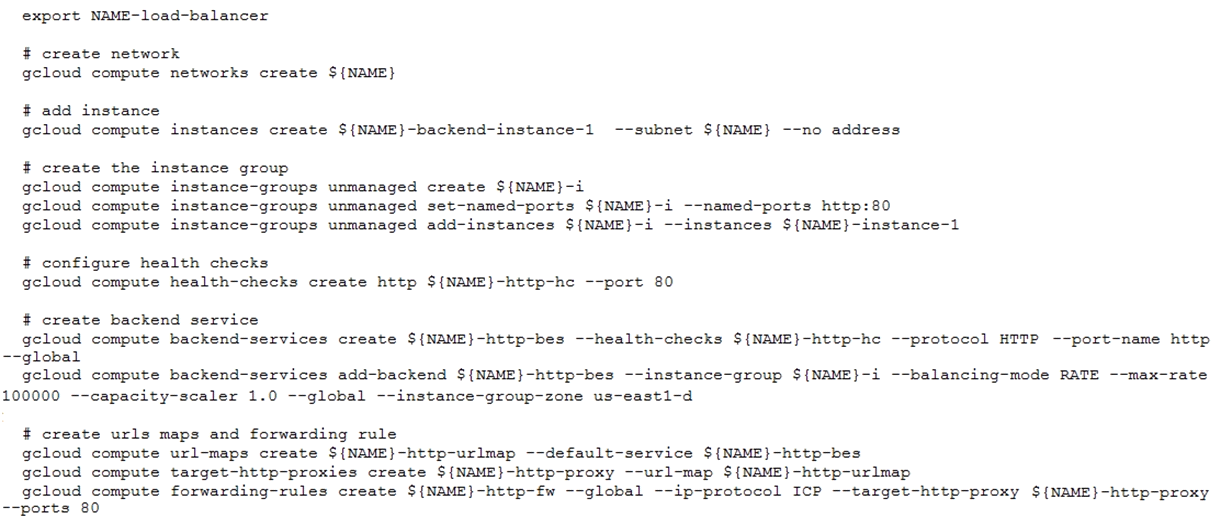
Health checks to port 80 on the Compute Engine virtual machine instance are failing and no traffic is sent to your instances. You want to resolve the problem.
Which commands should you run?
Suggested Answer:
C
Meghan
5 months agoBernardine
6 months agoAlayna
6 months agoJunita
6 months agoTawanna
6 months agoAlaine
6 months agoDesmond
6 months agoRuthann
6 months agoNickie
6 months agoElliot
6 months agoJerry
6 months agoArminda
7 months ago