GIAC GSLC Exam Questions
- Topic 1: Demonstrate an understanding of security architecture concepts/ Remediating both technical and physical system vulnerabilities
- Topic 2: Demonstrate an understanding of the phases of incident response and the business continuity process/ Management of a Security Operations Center
- Topic 3: Understanding of how symmetric, asymmetric, and hashing encryption works/ Demonstrate an understanding of using symmetric
- Topic 4: Demonstrate an understanding of effective negotiation and vendor management techniques/ Baselines in meeting an organization's security needs and risk appetite
- Topic 5: Demonstrate knowledge of common cryptographic terminology/ Understanding of the top threats to application code and software-based infrastructure
- Topic 6: Understanding of how to build a vulnerability management program for identifying/ Demonstrate an understanding of the components, structure
- Topic 7: Demonstrate an understanding of the role played by security policies/ Demonstrate an understanding of centralized logging and monitoring strategies
- Topic 8: Understanding of organizational culture and reporting structures/ integrating security into the software development lifecycle and DevOps processes
Free GIAC GSLC Exam Actual Questions
Note: Premium Questions for GSLC were last updated On May. 29, 2026 (see below)
John works as a network security officer in Gentech Inc. The company uses a TCP/IP network. While working on the network, a problem occurs related to the DNS resolution. Which of the following utilities can he use to diagnose the problem?
Eric is the project manager of the NQQ Project and has hired the ZAS Corporation to complete part of the project work for Eric's organization. Due to a change request the ZAS Corporation is no longer needed on the project even though they have completed nearly all of the project work. Is Eric's organization liable to pay the ZAS Corporation for the work they have completed so far on the project?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He is using a tool to crack the wireless encryption keys. The description of the tool is as follows:
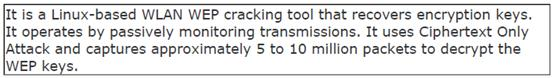
Which of the following tools is John using to crack the wireless encryption keys?
Managerial wisdom is the combination of knowledge as well as experience. It is the ability of the leaders to understand the members of the team. Which of the following are the characteristics that come under managerial wisdom?
Each correct answer represents a complete solution. Choose all that apply.
You have configured a virtualized Internet browser on your Windows XP professional computer. Using the virtualized Internet browser, you can protect your operating system from which of the following?
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Rebecca Scott
1 day agoMonica Martinez
25 days agoJason Morgan
1 month agoMaria Lewis
27 days agoEdward Flores
1 month agoJennifer Perez
21 days agoMaria Cooper
17 days agoCrystal Martinez
1 month agoStefanie
2 months agoSamira
2 months agoMary
2 months agoTeddy
3 months agoLindsey
3 months agoCecily
3 months agoLashawnda
4 months agoEva
4 months agoMerrilee
4 months agoTracey
4 months agoCiara
5 months agoMonte
5 months agoLindsay
5 months agoGalen
5 months agoDonette
6 months agoBlair
6 months agoIzetta
6 months agoBarney
6 months agoSarina
7 months agoRoyal
7 months agoRoselle
7 months agoCrissy
7 months agoWinfred
8 months agoBlair
8 months agoTiera
8 months agoRonald
8 months agoRuby
9 months agoDannie
9 months agoGregoria
11 months agoKate
1 year agoMelissa
1 year agoAileen
1 year agoKallie
1 year agoRosenda
1 year agoBettina
1 year agoBrendan
1 year agoPearlie
1 year agoNoe
1 year agoMa
1 year agoDoyle
2 years agoSina
2 years agoGlory
2 years agoIvan
2 years agoArlette
2 years agoEthan
2 years agoLenora
2 years agoLashawn
2 years agoLuisa
2 years agoTony
2 years agoJoseph
2 years agoSherrell
2 years agoAdell
2 years agoSharen
2 years agoJenifer
2 years agoFrancine
2 years agoErasmo
2 years agoJacob
2 years ago