Free GAQM CPEH-001 Exam Dumps May 2026
Here you can find all the free questions related with GAQM Certified Professional Ethical Hacker (CPEH) Exam (CPEH-001) exam. You can also find on this page links to recently updated premium files with which you can practice for actual GAQM Certified Professional Ethical Hacker (CPEH) Exam . These premium versions are provided as CPEH-001 exam practice tests, both as desktop software and browser based application, you can use whatever suits your style. Feel free to try the Certified Professional Ethical Hacker (CPEH) Exam premium files for free, Good luck with your GAQM Certified Professional Ethical Hacker (CPEH) Exam .MultipleChoice
Which one of the following attacks will pass through a network layer intrusion detection system undetected?
OptionsMultipleChoice
Charlie is the network administrator for his company. Charlie just received a new Cisco router and wants to test its capabilities out and to see if it might be susceptible to a DoS attack resulting in its locking up. The IP address of the Cisco switch is 172.16.0.45. What command can Charlie use to attempt this task?
OptionsMultipleChoice
A security consultant is trying to bid on a large contract that involves penetration testing and reporting. The company accepting bids wants proof of work so the consultant prints out several audits that have been performed. Which of the following is likely to occur as a result?
OptionsMultipleChoice
In the context of Windows Security, what is a 'null' user?
OptionsMultipleChoice
Choose one of the following pseudo codes to describe this statement:
"If we have written 200 characters to the buffer variable, the stack should stop because it cannot hold any more data."
OptionsMultipleChoice
What will the following command produce on a website's login page if executed successfully? SELECT email, passwd, login_id, full_name FROM members WHERE email = 'someone@somewhere.com'; DROP TABLE members; --'
OptionsMultipleChoice
What is the outcome of the comm''nc -l -p 2222 | nc 10.1.0.43 1234"?
OptionsMultipleChoice
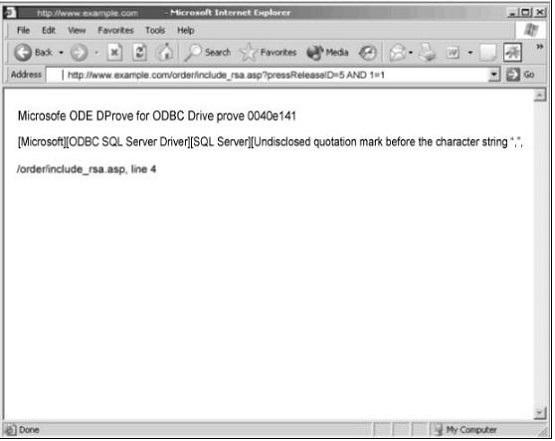
What is the main difference between a ''Normal'' SQL Injection and a ''Blind'' SQL Injection vulnerability?
OptionsMultipleChoice
What does the term ''Ethical Hacking'' mean?
OptionsMultipleChoice
To what does ''message repudiation'' refer to what concept in the realm of email security?
Options