Fortinet NSE7_ZTA-7.2 Exam Questions
- Fortinet Certified Solution Specialist Certifications
- Fortinet FCSS Fortinet Certified Solution Specialist Zero Trust Access Certifications
- Topic 1: Zero trust access (ZTA) methodology and components: This domain covers how to define the legacy perimeter-based security architecture, what is ZTA architecture, and how to identify the ZTA components.
- Topic 2: Network access control: This domain covers how to implement FortiNAC, set up and manage FortiNAC, and utilize device onboarding.
- Topic 3: Zero trust network access (ZTNA) deployment: This section comprises how to identify the ZTNA components, configure the ZTNA solution, and to oversee access to protected resources.
- Topic 4: Endpoint compliance: This domain covers how to configure FortiNAC agents, explain endpoint compliance and workflow, how to incorporate and link FortiClient EMS with FortiNAC, and monitor endpoints.
- Topic 5: Incident response: This domain covers how to configure FortiAnalyzer playbooks, set up FortiNAC incident response, and utilize FortiClient EMS quarantine management.
Free Fortinet NSE7_ZTA-7.2 Exam Actual Questions
Note: Premium Questions for NSE7_ZTA-7.2 were last updated On 21-07-2025 (see below)
An administrator has to configure LDAP authentication tor ZTNA HTTPS access proxy Which authentication scheme can the administrator apply1?
LDAP (Lightweight Directory Access Protocol) authentication for ZTNA (Zero Trust Network Access) HTTPS access proxy is effectively implemented using a Form-based authentication scheme. This approach allows for a secure, interactive, and user-friendly means of capturing credentials. Form-based authentication presents a web form to the user, enabling them to enter their credentials (username and password), which are then processed for authentication against the LDAP directory. This method is widely used for web-based applications, making it a suitable choice for HTTPS access proxy setups in a ZTNA framework. Reference: FortiGate Security 7.2 Study Guide, LDAP Authentication configuration sections.
Exhibit.
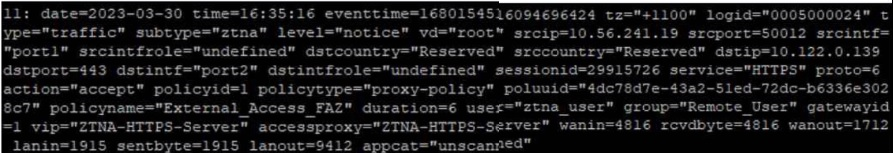
Based on the ZTNA logs provided, which statement is true?
Based on the ZTNA logs provided, the true statement is:
A) The Remote_user ZTNA tag has matched the ZTNA rule: The log includes a user tag 'ztna_user' and a policy name 'External_Access_FAZ', which suggests that the ZTNA tag for 'Remote_User' has successfully matched the ZTNA rule defined in the policy to allow access.
The other options are not supported by the information in the log:
B) An authentication scheme is configured: The log does not provide details about an authentication scheme.
C) The external IP for ZTNA server is 10.122.0.139: The log entry indicates 'dstip=10.122.0.139' which suggests that this is the destination IP address for the traffic, not necessarily the external IP of the ZTNA server.
D) Traffic is allowed by firewall policy 1: The log entry 'policyid=1' indicates that the traffic is matched to firewall policy ID 1, but it does not explicitly state that the traffic is allowed; although the term 'action=accept' suggests that the action taken by the policy is to allow the traffic, the answer option D could be considered correct as well.
Interpretation of FortiGate ZTNA Log Files.
Analyzing Traffic Logs for Zero Trust Network Access.
An administrator has to configure LDAP authentication tor ZTNA HTTPS access proxy Which authentication scheme can the administrator apply1?
LDAP (Lightweight Directory Access Protocol) authentication for ZTNA (Zero Trust Network Access) HTTPS access proxy is effectively implemented using a Form-based authentication scheme. This approach allows for a secure, interactive, and user-friendly means of capturing credentials. Form-based authentication presents a web form to the user, enabling them to enter their credentials (username and password), which are then processed for authentication against the LDAP directory. This method is widely used for web-based applications, making it a suitable choice for HTTPS access proxy setups in a ZTNA framework. Reference: FortiGate Security 7.2 Study Guide, LDAP Authentication configuration sections.
FortiNAC has alarm mappings configured for MDM compliance failure, and FortiClient EMS is added as a MDM connector When an endpoint is quarantined by FortiClient EMS, what action does FortiNAC perform?
In the scenario where FortiNAC has alarm mappings configured for MDM (Mobile Device Management) compliance failure and FortiClient EMS (Endpoint Management System) is integrated as an MDM connector, the typical response when an endpoint is quarantined by FortiClient EMS is to isolate the host in the registration VLAN. This action is consistent with FortiNAC's approach to network access control, focusing on ensuring network security and compliance. By moving the non-compliant or quarantined host to a registration VLAN, FortiNAC effectively segregates it from the rest of the network, mitigating potential risks while allowing for further investigation or remediation steps. Reference: FortiNAC documentation, MDM Compliance and Response Actions.
Which two statements are true regarding certificate-based authentication for ZTNA deployment? (Choose two.)
Certificate-based authentication is a method of verifying the identity of a device or user by using a digital certificate issued by a trusted authority. For ZTNA deployment, certificate-based authentication is used to ensure that only authorized devices and users can access the protected applications or resources.
B) The default action for empty certificates is block. This is true because ZTNA requires both device and user verification before granting access. If a device does not have a valid certificate issued by the ZTNA CA, it will be blocked by the ZTNA gateway. This prevents unauthorized or compromised devices from accessing the network.
D) Client certificate configuration is a mandatory component for ZTNA. This is true because ZTNA relies on client certificates to identify and authenticate devices. Client certificates are generated by the ZTNA CA and contain the device ID, ZTNA tags, and other information. Client certificates are distributed to devices by the ZTNA management server (such as EMS) and are used to establish a secure connection with the ZTNA gateway.
A) FortiGate signs the client certificate submitted by FortiClient. This is false because FortiGate does not sign the client certificates. The client certificates are signed by the ZTNA CA, which is a separate entity from FortiGate. FortiGate only verifies the client certificates and performs certificate actions based on the ZTNA tags.
C) Certificate actions can be configured only on the FortiGate CLI. This is false because certificate actions can be configured on both the FortiGate GUI and CLI. Certificate actions are the actions that FortiGate takes based on the ZTNA tags in the client certificates. For example, FortiGate can allow, block, or redirect traffic based on the ZTNA tags.
1: Technical Tip: ZTNA for Corporate hosts with SAML authentication and FortiAuthenticator as IDP
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Glory
7 months agoAltha
7 months agoOmega
9 months agoGregoria
10 months agoDarell
11 months agoAlberto
1 year agoDomonique
1 year agoMeghann
1 year agoMarget
1 year agoShantay
1 year agoGiuseppe
1 year agoColette
1 year agoNorah
1 year agoColton
1 year agoAudrie
1 year agoEdna
1 year agoCyril
1 year agoJulene
2 years agoRuthann
2 years agoRefugia
2 years agoColeen
2 years agoAlesia
2 years agoNenita
2 years agoAmber
2 years agoMendy
2 years agoIsreal
2 years agoKayleigh
2 years agoCarin
2 years agoFlorinda
2 years agoMarshall
2 years agoJeniffer
2 years agoBrock
2 years ago