Fortinet NSE4_FGT_AD-7.6 Exam Questions
- Fortinet Certified Professional Certifications
- Fortinet FCP Fortinet Certified Professional Security Operations Certifications
- Topic 1: Deployment and System Configuration: This domain covers initial FortiGate setup, logging configuration and troubleshooting, FGCP HA cluster configuration, resource and connectivity diagnostics, FortiGate cloud deployments (CNF and VM), and FortiSASE administration with user onboarding.
- Topic 2: Firewall Policies and Authentication: This domain focuses on creating firewall policies, configuring SNAT and DNAT for address translation, implementing various authentication methods, and deploying FSSO for user identification.
- Topic 3: Content Inspection: This domain addresses inspecting encrypted traffic using certificates, understanding inspection modes and web filtering, configuring application control, deploying antivirus scanning modes, and implementing IPS for threat protection.
- Topic 4: Routing: This domain covers configuring static routes for packet forwarding and implementing SD-WAN to load balance traffic across multiple WAN links.
- Topic 5: VPN: This domain focuses on implementing meshed or partially redundant IPsec VPN topologies for secure connections.
Free Fortinet NSE4_FGT_AD-7.6 Exam Actual Questions
Note: Premium Questions for NSE4_FGT_AD-7.6 were last updated On May. 30, 2026 (see below)
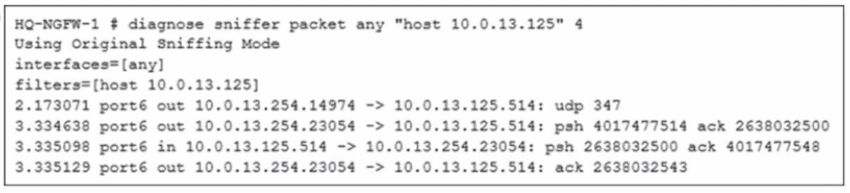
The FortiGate device HQ-NGFW-1 with the IP address 10.0.13.254 sends logs to the FortiAnalyzer device with the IP address 10.0.13.125. The administrator wants to verify that reliable logging is enabled on HQ-NGFW-1.
Which exhibit helps with the verification?
A)
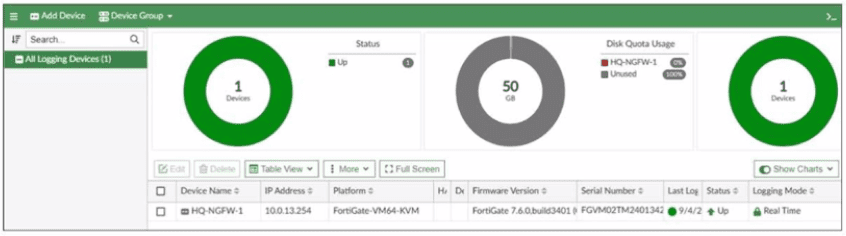
B)
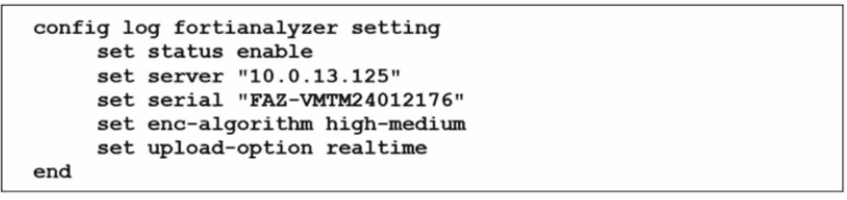
C)
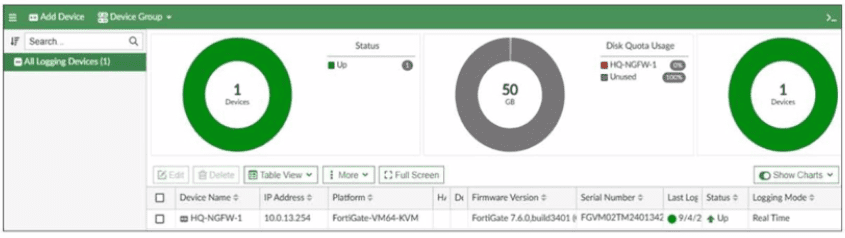
D)
An administrator wants to address shadow IT visibility challenges and prevent users from sending sensitive files outside the organization without proper approval. Which FortiSASE method should the administrator implement to achieve these goals? (Choose one answer)
''FortiSASE provides secure access to remote users for the following use cases:
* SIA enables secure web browsing for remote users to protect from known and unknown threats
* SPA enables explicit application access under a zero-trust access or with SD-WAN integration to ensure secure application access
* SSA addresses shadow IT visibility challenges and safeguards data loss prevention''
''FortiCASB provides cloud-based and API-based features to enable deep inspection of SaaS applications to enable detailed monitoring, analysis, and reporting features... Data loss prevention (DLP) helps to identify, monitor, and protect organizational data at rest and in motion.''
Technical Deep Dive:
The correct answer is C. Secure SaaS access (SSA).
The question gives two very specific requirements:
Shadow IT visibility
Prevent sensitive files from leaving the organization without approval
The study guide maps both directly to SSA. In FortiSASE, SSA aligns with SaaS governance and CASB-style controls. That is the right architecture when you need visibility into sanctioned and unsanctioned SaaS usage, plus DLP controls for uploads, sharing, and file movement.
Why the other options are wrong:
SIA focuses on securing internet browsing and remote web traffic.
SPA is for explicit zero-trust access to private applications.
SSD-WAN is not the FortiSASE method for SaaS visibility/DLP control.
In practice, SSA is the choice because it combines SaaS visibility, activity monitoring, and DLP-style enforcement. That lets an administrator detect shadow SaaS usage and apply controls such as blocking uploads, monitoring sharing events, or restricting file transfers based on policy. This is a CASB-oriented use case, not just generic web security.
Refer to the exhibit.
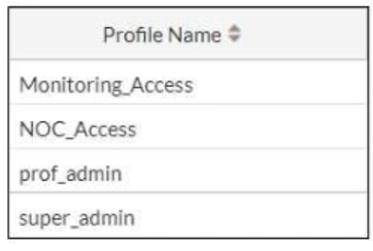
The NOC team connects to the FortiGate GUI with the NOC_Access admin profile. They request that their GUI sessions do not disconnect too early during inactivity. What must the administrator configure to answer this specific request from the NOC team? (Choose one answer)
According to the FortiOS 7.6 Administrator Study Guide, while there is a global administrative idle timeout setting that applies to all users by default (typically 5 minutes), FortiOS allows for granular control through Administrator Profiles. The Override Idle Timeout feature is specifically designed to allow different timeout values for different access profiles, which is ide1al for environments like a Network Operations Center (NOC) where persistent monitoring is required.23
To implement this, the administrator must modify the s4pecific access profile settings. By using the command config system accprofile 5and editing the NOC_Access profile, the administrator can enable the admintimeout-override and then increase the admintimeout value (Statement D). This configuration ensures that only the users assigned to that specific profile benefit from the extended session duration, maintaining a higher security posture for other administrative accounts that still follow the global timeout. Other options, such as changing the profile order (A) or assigning the super_admin role (C), do not address the specific requirement for inactivity timeout management. Option B is incorrect as 'offline value' is not a standard parameter for this feature.
Refer to the exhibit, which shows a partial configuration from the remote authentication server.
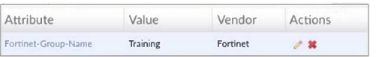
Why does the FortiGate administrator need this configuration? (Choose one answer)
''With this method, you must create a user group and add the preconfigured remote server to the group. This setup allows you to select one or more pre-existing groups from the Radius server, enabling any user within those groups to be authenticated.''
''The response from the server reports success, failure, and group membership details.''
''Note that Fortinet has a vendor-specific attributes (VSA) dictionary to identify the Fortinet-proprietary RADIUS attributes. This capability allows you to extend the basic functionality of RADIUS.''
Technical Deep Dive:
The attribute shown in the exhibit is Fortinet-Group-Name = Training. This is a Fortinet RADIUS Vendor-Specific Attribute (VSA) used to return group membership information to FortiGate. FortiGate uses that returned value to match the authenticated user to the corresponding FortiGate user group, in this case Training.
That is why A is correct: the administrator needs this so FortiGate can authenticate users and place or match them into the Training group for identity-based policy control.
Why the others are wrong:
* B is wrong because the RADIUS secret is configured separately as the shared secret between FortiGate and the RADIUS server, not as a Fortinet-Group-Name attribute.
* C is wrong because OU matching is an LDAP concept, not standard RADIUS group matching.
* D is wrong because this attribute is not for ''any'' group; it is explicitly returning the specific group name Training.
In practice, this lets FortiGate apply firewall policies such as:
```bash
config user group
edit 'Training'
set member 'RADIUS_Server'
next
end
```
Then the RADIUS server returns Fortinet-Group-Name=Training, and FortiGate matches the user into that group for policy enforcement.
Refer to the exhibit.
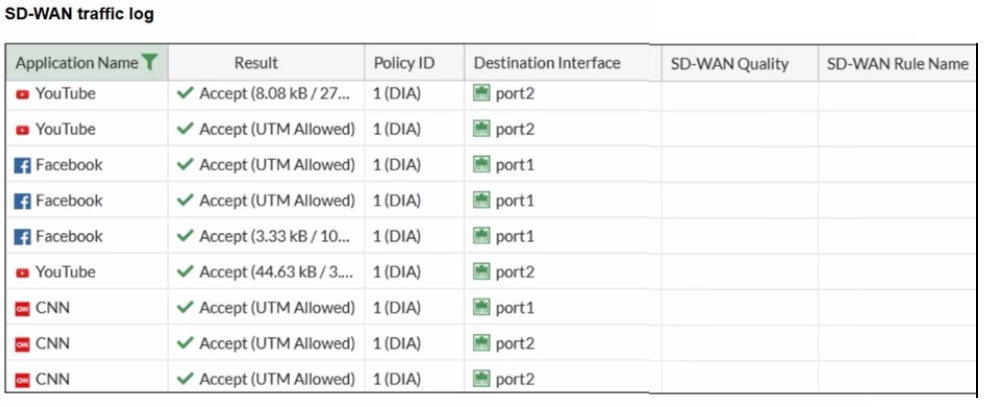
The administrator configured SD-WAN rules and set the FortiGate traffic log page to display SD-WAN-specific columns: SD-WAN Quality and SD-WAN Rule Name
FortiGate allows the traffic according to policy ID 1 placed at the top. This is the policy that allows SD-WAN traffic. Despite these settings, the traffic logs do not show the name of the SD-WAN rule used to steer those traffic flows
What could be the reason?
In FortiOS 7.6, SD-WAN steering decisions are recorded in traffic logs only when traffic matches an explicit SD-WAN rule (SD-WAN service rule). When no configured SD-WAN rule matches a session, FortiGate uses the implicit (default) SD-WAN rule/behavior to select a member (often resulting in load-balancing or default selection based on the configured SD-WAN algorithm).
In the exhibit, traffic is permitted by firewall policy ID 1, and the Destination Interface alternates between port1 and port2, but SD-WAN Rule Name remains empty. This is consistent with the sessions being forwarded by the implicit SD-WAN rule, which does not populate a named rule in the log columns.
Why the other options are not correct:
A: SD-WAN rule name logging is not a ''delayed display'' behavior requiring refresh; it is populated per-session when an explicit rule matches.
B: Application Control is not required for SD-WAN rule name to appear. Rule name logging depends on SD-WAN rule match, not on whether Application Control is enabled.
C: Feature visibility affects GUI display options, but the exhibit already shows the SD-WAN columns enabled; the issue is that no explicit SD-WAN rule is being hit.
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Deborah Lopez
4 days agoAndrew Rogers
22 days agoOlivia Baker
1 month agoRachel Flores
27 days agoBetty Bell
27 days agoTiffany Walker
21 days agoTimothy Campbell
27 days agoJohn Hill
1 month agoPaz
2 months agoShaniqua
2 months agoEliseo
2 months agoAleisha
3 months agoRikki
3 months agoFanny
3 months agoLaquita
3 months agoElfrieda
4 months agoJenise
4 months agoLeota
4 months agoDarnell
4 months agoMicaela
5 months agoSusana
5 months agoSimona
5 months agoStevie
5 months ago