F5 Networks F5CAB3 Exam Questions
- Topic 1: Apply procedural concepts required to modify and manage virtual servers: This domain covers managing virtual servers including applying persistence, encryption, and protocol profiles, identifying iApp objects, reporting iRules, and showing pool configurations.
- Topic 2: Apply procedural concepts required to modify and manage pools: This domain addresses managing server pools including health monitors, load balancing methods, priority groups, and service port configurations.
Free F5 Networks F5CAB3 Exam Actual Questions
Note: Premium Questions for F5CAB3 were last updated On Apr. 24, 2026 (see below)
Refer to the exhibit.
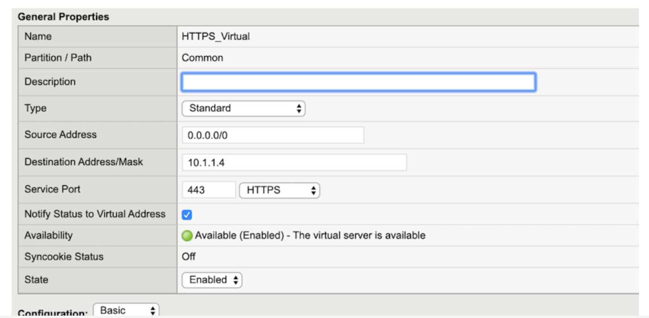
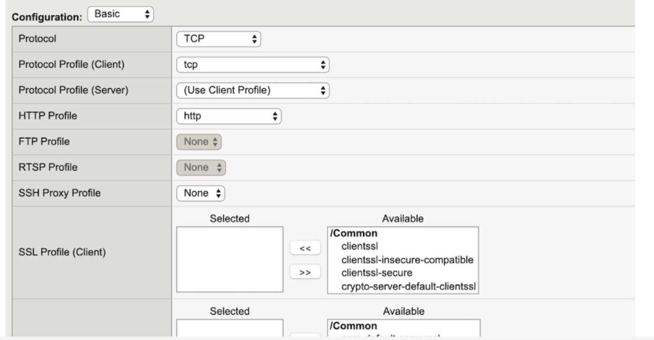
A BIG-IP Administrator configures a Virtual Server to handle HTTPS traffic. Users report that the application is NOT working. Which additional configuration is required to resolve this issue?
According to the provided exhibit, the 'SSL Profile (Client)' section in the Virtual Server configuration is empty. For a BIG-IP system to process HTTPS traffic, it must act as an SSL/TLS endpoint. This process, known as SSL Termination or SSL Offload, requires the assignment of a Client SSL Profile to the Virtual Server. Without this profile, the BIG-IP does not have the necessary certificate and private key information to perform the SSL handshake with the client's browser. Consequently, when a user attempts to connect via HTTPS, the TCP connection may establish, but the SSL handshake will fail because the BIG-IP will not know how to decrypt the incoming encrypted packets.
A Client SSL profile defines the ciphers, certificates, and keys that the BIG-IP uses to communicate securely with the client. In a standard HTTPS deployment, the BIG-IP decrypts the traffic and can then send it to the backend pool members either as plain text (header insertion/manipulation) or re-encrypt it using a Server SSL profile. While a Server SSL profile (Option C) is needed if the backend servers themselves require HTTPS, the initial failure for a user reaching a Virtual Server is almost always the lack of a Client SSL profile to terminate the user's connection. Changing the Service Port to HTTP (Option D) would be incorrect because the goal is to handle HTTPS traffic (typically port 443). Assigning the 'clientssl' or a custom client-side profile from the 'Available' list to the 'Selected' list in the GUI is the mandatory step to make the Virtual Server operational for secure web traffic.
For a given Virtual Server, the BIG-IP must perform SSL Offload and negotiate secure communication over TLSv1.2 only. What should the BIG-IP Administrator do to meet this requirement?
To fulfill the requirement of 'SSL Offload' limited to 'TLSv1.2 only,' the administrator must focus on the client-side of the connection. SSL Offload means the BIG-IP terminates the encrypted connection from the user, processes the traffic (often as plain text internally), and optionally sends it to the backend. The profile responsible for this termination and the initial negotiation with the client's browser is the Client SSL Profile.
A custom Client SSL Profile must be created because the default clientssl profile typically allows a broad range of protocols for compatibility (including TLS 1.0, 1.1, and 1.2). To restrict communication specifically to TLS 1.2, the administrator modifies the Ciphers string within the profile. Using a string such as DEFAULT:!SSLv3:!TLSv1:!TLSv1.1 or specifically defining TLSv1.2-only suites ensures that the BIG-IP will reject any handshake attempts from older, less secure protocols.
Server SSL Profiles (Options B and C) are used for the encryption between the BIG-IP and the backend nodes, which is not what is requested here. Simply selecting 'no TLSv1' in an options list (Option D) is insufficient and often refers to older versions of the software; the modern and standard way to control protocol negotiation on a BIG-IP is through the precise application of Cipher Strings within the Client SSL profile. This ensures compliance with security standards like PCI-DSS while providing the offloading benefits to the backend infrastructure.
The BIG-IP Administrator has to provide encrypted communication between the users and the virtual server they access. Multiple hostnames are configured in DNS with the same IP address. Which profile type and setting in the profile should be used? (Choose one answer)
To provide encrypted communication between users and a virtual server, the BIG-IP system acts as a transparent SSL/TLS proxy. The administrative configuration required for this is a Client SSL profile.
When multiple hostnames (FQDNs) are associated with a single IP address, the system must determine which SSL certificate to present to the client during the initial TLS handshake. This is achieved using an extension of the TLS protocol called Server Name Indication (SNI).
The configuration logic is as follows:
Profile Type: The Client SSL profile is responsible for terminating the SSL connection from the client (the user) to the BIG-IP system.
The Setting: Within the Client SSL profile (under the 'Advanced' view), there is a field specifically called Server Name. By entering the specific hostname (e.g., www.example.com) in this field, the BIG-IP system can match the hostname requested by the client in the ClientHello message to the correct profile.
Implementation: The administrator typically creates multiple Client SSL profiles---one for each hostname---and assigns them all to the same virtual server. One of these profiles must be designated as the Default SSL Profile for SNI to handle requests where the client does not provide a hostname or provides one that does not match any specific profile.
By using the Client SSL profile and the Server Name setting, the BIG-IP system ensures that each user receives the correct certificate for the specific site they are trying to reach, even though all sites share a single virtual server IP.
All pool members are online. All other virtual server settings are at default.
What might alter the load balancing behavior? (Choose one answer)
By default, BIG-IP load balancing algorithms (such as Round Robin) distribute connections evenly across all available pool members. However, persistence profiles override normal load balancing decisions by forcing subsequent connections from a client to be sent to the same pool member.
According to the BIG-IP Administration: Data Plane Configuration documentation:
Persistence creates a client-to-server mapping that is honored before load balancing algorithms are applied.
When persistence is enabled, BIG-IP may repeatedly select the same pool member even if others are available.
This directly alters load balancing behavior.
Why the other options are incorrect:
A . Adding a OneConnect profile
OneConnect optimizes server-side TCP connections but does not change which pool member is selected.
B . Enabling SNAT automap
SNAT affects source address translation, not pool member selection.
C . Enabling a fallback host in the HTTP profile
A fallback host is only used when no pool members are available.
Correct Resolution:
Adding a persistence profile alters load balancing behavior by maintaining client affinity to a specific pool member.
A BIG-IP Administrator creates a new Virtual Server to load balance SSH traffic. Users are unable to log on to the servers.
What should the BIG-IP Administrator do to resolve the issue?
SSH is a TCP Layer 4 protocol. Applying an HTTP profile causes BIG-IP to expect HTTP headers, breaking SSH sessions. Removing the HTTP profile allows raw TCP forwarding.
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Currently there are no comments in this discussion, be the first to comment!
Abel
19 days agoElliot
26 days agoAsuncion
1 month agoFloyd
1 month agoMaryann
2 months agoMargret
2 months agoMarisha
2 months agoCordelia
2 months agoMicaela
3 months agoLeandro
3 months agoCammy
3 months agoColeen
3 months agoCharisse
4 months agoClaudio
4 months agoDylan
4 months ago