Eccouncil 312-38 Exam Questions
- Topic 1: Risk Anticipation with Risk Management/ Technical Network Security
- Topic 2: Threat Prediction with Cyber Threat Intelligence/ Network Attacks and Defense Strategies
- Topic 3: Business Continuity and Disaster Recovery/ Endpoint Security-Windows Systems
- Topic 4: Threat Assessment with Attack Surface Analysis/ Administrative Network Security
- Topic 5: Incident Response and Forensic Investigation/ Endpoint Security-IoT Devices
- Topic 6: Network Logs Monitoring and Analysis/ Network Perimeter Security
- Topic 7: Network Traffic Monitoring and Analysis/ Administrative Application Security
- Topic 8: Enterprise Wireless Network Security/ Endpoint Security- Mobile Devices
- Topic 9: Enterprise Cloud Network Security/ Endpoint Security-Linux Systems
- Topic 10: Enterprise Virtual Network Security/ Data Security
Free Eccouncil 312-38 Exam Actual Questions
Note: Premium Questions for 312-38 were last updated On May. 06, 2026 (see below)
Which firewall technology provides the best of both packet filtering and application-based filtering and is used in Cisco Adaptive Security Appliances?
Stateful multilayer inspection (SMLI) firewalls provide a robust security mechanism that combines the features of both packet filtering and application-based filtering. They are capable of inspecting the state of active connections and make decisions based on the context of the traffic. Cisco Adaptive Security Appliances (ASA) utilize this technology to offer an integrated approach to network security, which includes application-aware firewall capabilities, intrusion prevention, and content security services. This technology is particularly effective as it not only looks at the state and attributes of the packets but also examines the data within the packet, enabling it to provide more comprehensive protection against various types of network threats.
John has planned to update all Linux workstations in his network. The organization is using various Linux distributions including Red hat, Fedora and Debian. Which of following commands will he use to
update each respective Linux distribution?
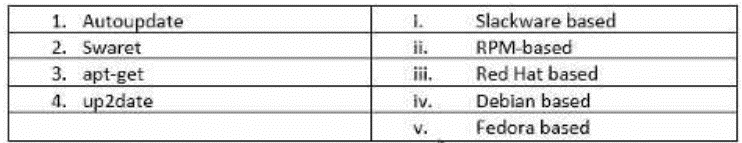
The correct commands to update the respective Linux distributions are as follows:
Red Hat: Uses theyumcommand or the newerdnfcommand for package management and updates.
Fedora: Originally usedyumbut now has transitioned todnfas the default package manager.
Debian: Utilizes theapt-getcommand for package management tasks, including updates.
The matching from the options provided would be:
1-v: Slackware based systems useAutoupdate.
2-iii: RPM-based systems, which include Fedora, useSwaret.
3-i: Debian based systems useapt-get.
4-iv: Red Hat based systems useup2date.
Which of the following is consumed into SIEM solutions to take control of chaos, gain in-depth knowledge of threats, eliminate false positives, and implement proactive intelligence-driven defense?
SIEM (Security Information and Event Management) solutions are designed to provide a comprehensive view of an organization's security status by collecting and analyzing security-related data from various sources. To enhance their capabilities, SIEM solutions consume threat intelligence feeds, which are streams of data that provide information about current and potential security threats. These feeds include details such as indicators of compromise (IoCs), tactics, techniques, and procedures (TTPs) used by cybercriminals, and vulnerabilities in software or systems. By integrating threat intelligence feeds, SIEM solutions can improve real-time threat detection, reduce false positives, and support proactive, intelligence-driven defense strategies.This integration allows organizations to stay one step ahead of emerging threats and advisories, providing insights into the attacker's TTPs and associated IoCs that can accelerate investigation and response efforts1.
Damian is the chief security officer of Enigma Electronics. To block intruders and prevent any environmental accidents, he needs to set a two-factor authenticated keypad lock at the entrance, rig a fire
suppression system, and link any video cameras at various corridors to view the feeds in the surveillance room. What layer of network defense-in-depth strategy is he trying to follow?
The measures Damian is implementing are part of thePhysicallayer of network defense-in-depth strategy. This layer involves securing the physical infrastructure of the organization, which includes controlling physical access to the building through mechanisms like two-factor authenticated locks and monitoring the environment with video surveillance. Additionally, implementing fire suppression systems is a part of safeguarding the physical premises against environmental hazards.These measures are essential to prevent unauthorized physical access and to protect against physical threats that could harm the network's infrastructure.Reference: The Certified Network Defender (CND) program by EC-Council covers a defense-in-depth security strategy that includes the Physical layer as one of its core components12.
Which among the following control and manage the communication between VNF with computing, storage, and network resources along with virtualization?
In the context of Network Function Virtualization (NFV), the Virtualized Infrastructure Manager (VIM) is responsible for controlling and managing the NFV infrastructure (NFVI), which includes compute, storage, and network resources. The VIM operates within one operator's infrastructure domain and is a key component of the Management and Orchestration (MANO) framework. It ensures that the virtualized resources are appropriately allocated and managed to support the deployment and operation of Virtual Network Functions (VNFs).
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Donald Thompson
6 days agoMark Thomas
19 days agoEdward Ramirez
10 days agoJohn Sanchez
3 days agoRichard Smith
15 days agoAnglea
1 month agoDenny
1 month agoKaron
2 months agoVallie
2 months agoIsabella
2 months agoErnie
2 months agoIvan
3 months agoGary
3 months agoRasheeda
3 months agoGerri
3 months agoElly
4 months agoJulieta
4 months agoDominga
4 months agoPamella
4 months agoJina
5 months agoSheron
5 months agoRosendo
5 months agoMartina
5 months agoAllene
6 months agoLevi
6 months agoAmber
6 months agoLavera
6 months agoDean
7 months agoRonald
7 months agoJuliann
7 months agoWynell
7 months agoLarae
8 months agoSherita
8 months agoVerdell
8 months agoGary
8 months agoStanton
10 months agoCharisse
11 months agoFranchesca
1 year agoZona
1 year agoVicki
1 year agoFallon
1 year agoNieves
1 year agoAltha
1 year agoCristy
1 year agoCoral
1 year agoDwight
1 year agoZona
1 year agoNilsa
1 year agoMarg
1 year agoChi
1 year agoTammi
1 year agoCruz
1 year agoRolande
1 year agoAntione
1 year agoFelicidad
1 year agoDottie
2 years agoSharan
2 years agoSabra
2 years agoBreana
2 years agoAllene
2 years agoYan
2 years agoAdell
2 years agoWillow
2 years agoDudley
2 years agoMagnolia
2 years agoLilli
2 years agoDolores
2 years agoTheodora
2 years agoRoyal
2 years agoVirgina
2 years agoErick
2 years agoVanna
2 years agoCharlene
2 years ago