Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Eccouncil 312-96 Exam - Topic 1 Question 22 Discussion
Actual exam question for
Eccouncil's
312-96 exam
Question #: 22
Topic #: 1
[All 312-96 Questions]
Topic #: 1
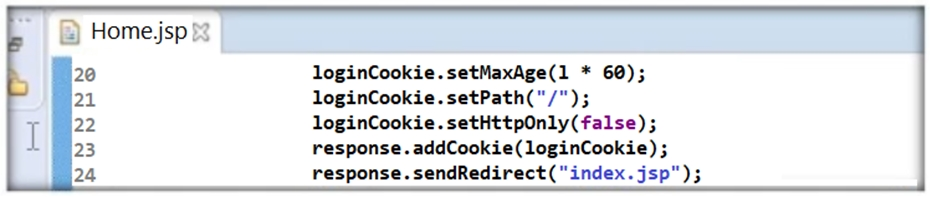
Thomas is not skilled in secure coding. He neither underwent secure coding training nor is aware of the consequences of insecure coding. One day, he wrote code as shown in the following screenshot. He passed 'false' parameter to setHttpOnly() method that may result in the existence of a certain type of vulnerability. Identify the attack that could exploit the vulnerability in the above case.
Suggested Answer:
B
Antonio
6 months agoElbert
6 months agoSherron
6 months agoAileen
7 months agoAlysa
7 months agoAlberto
7 months agoPamella
7 months agoSherell
7 months agoAlishia
8 months agoWhitley
8 months agoCammy
8 months agoEmelda
8 months agoLou
8 months agoRosendo
8 months agoColette
8 months agoMaile
2 years agoJustine
2 years agoJani
2 years agoArlette
2 years agoEladia
2 years agoGlynda
2 years agoCharolette
2 years agoJenelle
2 years agoOren
2 years agoHelene
2 years agoDella
2 years agoLavonda
2 years agoElke
2 years agoAshley
2 years agoShannan
2 years agoLuis
2 years agoVilma
2 years agoChantay
2 years ago