Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Eccouncil 312-39 Exam - Topic 9 Question 57 Discussion
Actual exam question for
Eccouncil's
312-39 exam
Question #: 57
Topic #: 9
[All 312-39 Questions]
Topic #: 9
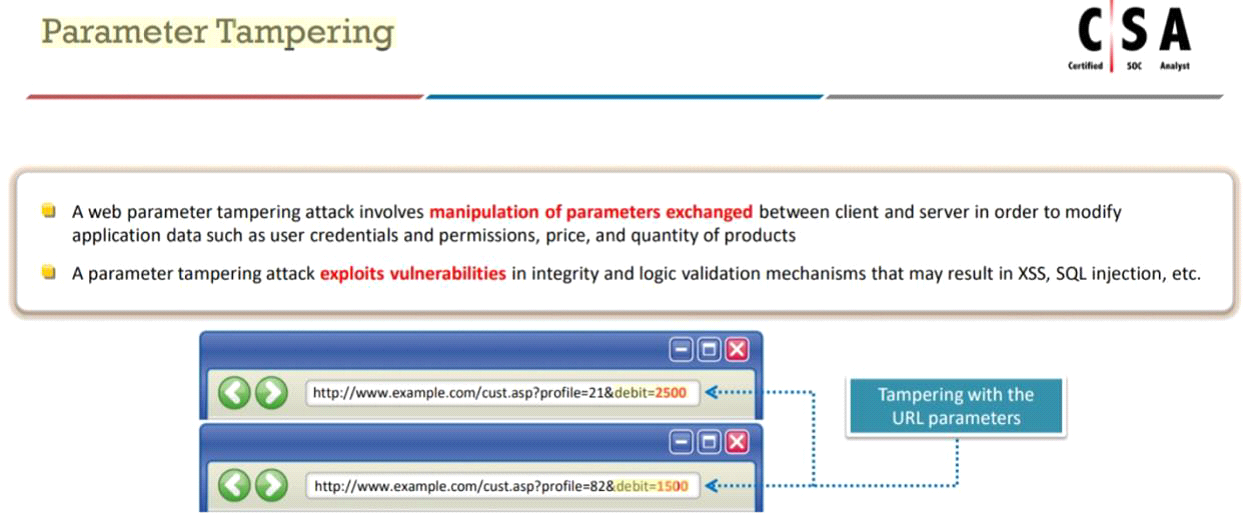
An attacker exploits the logic validation mechanisms of an e-commerce website. He successfully purchases a product worth $100 for $10 by modifying the URL exchanged between the client and the server.
Identify the attack depicted in the above scenario.
Suggested Answer:
C
Truman
7 months agoSelma
7 months agoDarnell
7 months agoLaticia
7 months agoPhuong
7 months agoGenevieve
8 months agoJacquelyne
8 months agoGail
8 months agoAlesia
8 months agoAleta
8 months agoKanisha
8 months ago