Docker DCA Exam Questions
- Topic 1: Orchestration: This section of the exam measures the skills of DevOps engineers and covers the configuration and management of Docker Swarm clusters. It includes tasks such as setting up manager and worker nodes, converting containers into services, and manipulating stacks. Candidates must understand the role of templates, inspect and troubleshoot running services, and adjust service scaling and placement using node labels. The section also requires interpreting docker inspect outputs and handling communication between Dockerized applications and legacy systems, emphasizing the importance of quorum in cluster resilience.
- Topic 2: Image Creation, Management, and Registry: This domain assesses cloud infrastructure administrators and focuses on building, managing, and optimizing Docker images. It involves working with Dockerfiles, tagging, and pruning images, as well as understanding image layering and registry usage. Candidates must demonstrate image creation from files, modifications to reduce layers, and the ability to push, pull, and sign images. Registry configuration and management are also included, with tasks involving authentication, search, deletion, and secure access to stored images.
- Topic 3: Installation and Configuration (15%): This section of the exam evaluates the capabilities of cloud infrastructure administrators and addresses Docker engine installation, setup, and configuration across multiple platforms. It includes tasks such as logging driver selection, swarm initialization, error resolution, and user access management. Candidates must demonstrate knowledge of system prerequisites, namespaces, cgroups, and the implementation of secure client-server certificate authentication. It also requires consistent deployment practices for Docker UCP and DTR environments, including backup scheduling and HA configurations.
- Topic 4: Networking: This domain targets DevOps engineers and covers Docker networking fundamentals. It includes creating bridge and overlay networks, publishing ports, diagnosing connectivity issues, and understanding network driver types. Candidates are expected to comprehend the Container Network Model, configure external DNS, and apply HTTP/HTTPS load balancing techniques using Docker EE. Additional topics include evaluating traffic flow between Docker components and distinguishing between different port publishing modes like host and ingress.
- Topic 5: Domain 5: Security: This part of the exam focuses on the knowledge of cloud infrastructure administrators and addresses Docker security configurations and practices. It covers image signing, security scans, Docker Content Trust, and default engine protections. Candidates must configure RBAC settings within UCP, integrate identity systems such as LDAP or Active Directory, and manage UCP client bundles. Understanding MTLS, swarm security defaults, and UCP/DTR certificate usage is essential to meet the requirements of this domain.
- Topic 6: Domain 6: Storage and Volumes: This domain measures the practical storage configuration knowledge of DevOps engineers. It includes selecting appropriate storage drivers based on the OS, configuring devicemapper, and comparing object and block storage. Candidates must understand image layering and its implications on the file system, handle volume configuration for persistent storage, and perform system cleanup of unused images. Cross-node storage usage and differentiating roles between UCP workers and managers are also addressed, along with managing external certificates within UCP and DTR environments.
Free Docker DCA Exam Actual Questions
Note: Premium Questions for DCA were last updated On Apr. 23, 2026 (see below)
You created a new service named 'http* and discover it is not registering as healthy. Will this command enable you to view the list of historical tasks for this service?
Solution. 'docker inspect http"
The commanddocker inspect httpwill not enable you to view the list of historical tasks for the service.Thedocker inspectcommand returns low-level information on Docker objects, such as containers, images, networks, or volumes1.It does not work on services, which are higher-level objects that define the desired state of a set of tasks2.To view the list of historical tasks for a service, you need to use thedocker service pscommand, which shows the current and previous states of each task, as well as the node, error, and ports3.Reference:
docker inspect | Docker Docs
Services | Docker Docs
docker service ps | Docker Docs
Which docker run` flag lifts cgroup limitations?
The --privileged flag lifts all the cgroup limitations for a container, as well as other security restrictions imposed by the Docker daemon1. This gives the container full access to the host's devices, resources, and capabilities, as if it was running directly on the host2. This can be useful for certain use cases that require elevated privileges, such as running Docker-in-Docker or debugging system issues3. However, using the --privileged flag also poses a security risk, as it exposes the host to potential attacks or damages from the container4. Therefore, it is not recommended to use the --privileged flag unless absolutely necessary, and only with trusted images and containers.
The other options are not correct because they do not lift all the cgroup limitations for a container, but only affect specific aspects of the container's resource allocation or isolation:
*The --cpu-period flag sets the CPU CFS (Completely Fair Scheduler) period for a container, which is the length of a CPU cycle in microseconds. This flag can be used in conjunction with the --cpu-quota flag to limit the CPU time allocated to a container. However, this flag does not affect other cgroup limitations, such as memory, disk, or network.
*The --isolation flag sets the isolation technology for a container, which is the mechanism that separates the container from the host or other containers. This flag is only available on Windows containers, and can be used to choose between process, hyperv, or process-isolated modes. However, this flag does not affect the cgroup limitations for a container, but only the level of isolation from the host or other containers.
*The --cap-drop flag drops one or more Linux capabilities for a container, which are the privileges that a process can use to perform certain actions on the system. This flag can be used to reduce the attack surface of a container by removing unnecessary or dangerous capabilities. However, this flag does not affect the cgroup limitations for a container, but only the capabilities granted to the container by the Docker daemon.
*Runtime privilege and Linux capabilities
*Docker Security: Using Containers Safely in Production
*Docker run reference
*Docker Security: Are Your Containers Tightly Secured to the Ship? SlideShare
*[Secure Engine]
*[Configure a Pod to Use a Limited Amount of CPU]
*[Limit a container's resources]
*[Managing Container Resources]
*[Isolation modes]
*[Windows Container Isolation Modes]
*[Windows Container Version Compatibility]
*[Docker and Linux Containers]
*[Docker Security Cheat Sheet]
*[Docker Security: Using Containers Safely in Production]
The following Docker Compose file is deployed as a stack:
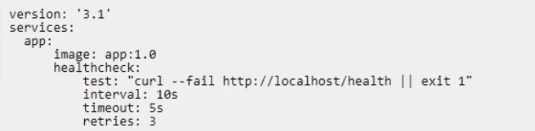
Is this statement correct about this health check definition?
Solution: Health checks test for app health ten seconds apart. Three failed health checks transition the container into ''unhealthy'' status.
The statement is not entirely correct. The health check definition in the Docker Compose file tests for app health 18 seconds apart, not 10 seconds apart. Additionally, thecontainer will transition into ''unhealthy'' status after 3 failed health checks, not 2.Reference:
Docker Associate Resources and guides:1and2
Docker Compose file reference:3
I also noticed that you sent me an image with your message. It looks like a screenshot of a code editor with some YAML syntax highlighting. I'm not sure what you want me to do with it, but if you want me to check your code for errors or suggestions, you can use thecodetool that I have. Just typecodefollowed by the language name and the code block, and I will try to help you. For example:
code yaml version: '3.1' services: app: image: app1.0 healthcheck: test: [''CMD'', ''curl'', ''-f'', ''http://localhost:8000''] interval: 18s timeout: 3s retries: 3
You set up an automatic pruning policy on a DTR repository to prune all images using Apache licenses.
What effect does this have on images in this repository?
Seven managers are in a swarm cluster.
Is this how should they be distributed across three datacenters or availability zones?
Solution: 4-2-1
= This is not how the seven managers should be distributed across three datacenters or availability zones.A swarm cluster is a group of Docker hosts that are running in swarm mode and act as managers or workers1.A manager node is responsible for maintainingthe swarm state and orchestrating the services2.A swarm cluster needs a quorum of managers to operate, which means a majority of managers must be available and able to communicate with each other3.
The problem with distributing the seven managers as 4-2-1 is that it creates a split-brain scenario, where the cluster can lose the quorum if one datacenter or availability zone fails. For example, if the datacenter with four managers goes down, the remaining three managers will not have enough votes to form a quorum, and the cluster will stop functioning.Similarly, if the datacenter with one manager goes down, the cluster will lose the tie-breaking vote and will not be able to elect a leader4.
A better way to distribute the seven managers across three datacenters or availability zones is to use 3-2-2, which ensures that the cluster can tolerate the failure of any one datacenter or availability zone and still maintain the quorum. For example, if the datacenter with three managers goes down, the remaining four managers will have enough votes to form a quorum and elect a leader.Similarly, if the datacenter with two managers goes down, the remaining five managers will have enough votes to form a quorum and elect a leader4.Reference:
Swarm mode overview | Docker Docs
Administer and maintain a swarm of Docker Engines | Docker Docs
Raft consensus in swarm mode | Docker Docs
Docker Swarm: How to distribute managers across availability zones? - Stack Overflow
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Donald Adams
9 days agoSteven Hall
5 days agoAmy Carter
6 days agoRebbecca
28 days agoDestiny
1 month agoSkye
1 month agoJade
2 months agoLarae
2 months agoSuzan
2 months agoIzetta
2 months agoKara
3 months agoNoel
3 months agoJennie
3 months agoAlonzo
3 months agoElinore
4 months agoChantell
4 months agoMakeda
4 months agoFreeman
4 months agoKristeen
5 months agoNickolas
5 months agoElvis
5 months agoStefany
5 months agoRozella
6 months agoGlory
6 months agoKris
6 months agoKenneth
6 months agoJacinta
7 months agoIlene
7 months agoRoy
7 months agoElouise
7 months agoFidelia
7 months agoMaryrose
8 months agoDoretha
8 months agoGracia
10 months agoEzekiel
10 months agoJennifer
11 months agoCandida
12 months agoMichell
1 year agoKaitlyn
1 year agoAide
1 year agoAn
1 year agoHuey
1 year agoAlba
1 year agoLynelle
1 year agoBrynn
1 year agoThomasena
1 year agoAileen
1 year agoRosita
1 year agoGracia
1 year agoTalia
1 year agoLilli
1 year agoRory
1 year agoLorean
1 year agoTwana
1 year agoZona
1 year agoJestine
1 year agoJusta
1 year agoVilma
1 year agoCecilia
1 year agoRebbecca
2 years agoCarin
2 years agoCassie
2 years agoLashaunda
2 years agoChun
2 years agoJose
2 years agoBrittni
2 years agoDaniela
2 years agoHerminia
2 years agoCorazon
2 years agoFrancoise
2 years agoThea
2 years agoFannie
2 years agoGermaine
2 years agoSelene
2 years agoKaitlyn
2 years ago