CrowdStrike CCFH-202b Exam Questions
- Topic 1: ATT&CK Frameworks: This domain covers understanding the cyber kill chain and using the MITRE ATT&CK Framework to model threat actor behaviors and communicate findings to non-technical audiences.
- Topic 2: Detection Analysis: This domain focuses on analyzing Host and Process Timelines in Falcon to understand events and detections, and pivoting to additional investigative tools.
- Topic 3: Search and Investigation Tools: This domain covers analyzing file and process metadata, using Investigate Module tools, performing various searches, and interpreting dashboard results.
- Topic 4: Event Search: This domain focuses on using CrowdStrike Query Language to build queries, format and filter event data, understand process relationships and event types, and create custom dashboards.
- Topic 5: Reports and References: This domain covers using built-in Hunt and Visibility reports and leveraging Events Full Reference documentation for event information.
- Topic 6: Hunting Analytics: This domain focuses on recognizing malicious behaviors, evaluating information reliability, decoding command line activity, identifying infection patterns, distinguishing legitimate from adversary activity, and identifying exploited vulnerabilities.
- Topic 7: Hunting Methodology: This domain covers conducting active hunts, performing outlier analysis, testing hunting hypotheses, constructing queries, and investigating process trees.
Free CrowdStrike CCFH-202b Exam Actual Questions
Note: Premium Questions for CCFH-202b were last updated On Apr. 11, 2026 (see below)
You want to produce a list of all event occurrences along with selected fields such as the full path, time, username etc. Which command would be the appropriate choice?
The table command is used to produce a list of all event occurrences along with selected fields such as the full path, time, username etc. It takes one or more field names as arguments and displays them in a tabular format. The fields command is used to keep or remove fields from search results, not to display them in a list. The distinct_count command is used to count the number of distinct values of a field, not to display them in a list. The values command is used to display a list of unique values of a field within each group, not to display all event occurrences.
Adversaries commonly execute discovery commands such as netexe, ipconfig.exe, and whoami exe. Rather than query for each of these commands individually, you would like to use a single query with all of them. What Splunk operator is needed to complete the following query?
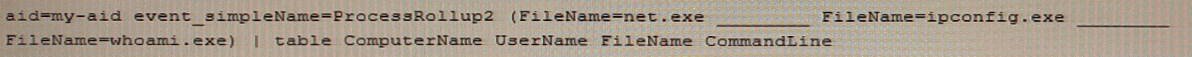
The OR operator is needed to complete the following query, as it allows to search for events that match any of the specified values. The query would look like this:
event_simpleName=ProcessRollup2 FileName=net.exe OR FileName=ipconfig.exe OR FileName=whoami.exe
The OR operator is used to combine multiple search terms or expressions and return events that match at least one of them. The IN, NOT, and AND operators are not suitable for this query, as they have different functions and meanings.
Which of the following queries will return the parent processes responsible for launching badprogram exe?
This query will return the parent processes responsible for launching badprogram.exe by using a subsearch to find the processrollup2 events where FileName is badprogram.exe, then renaming the TargetProcessld_decimal field to ParentProcessld_decimal and using it as a filter for the main search, then using stats to count the occurrences of each FileName by _time. The other queries will either not return the parent processes or use incorrect field names or syntax.
Lateral movement through a victim environment is an example of which stage of the Cyber Kill Chain?
Lateral movement through a victim environment is an example of the Command & Control stage of the Cyber Kill Chain. The Cyber Kill Chain is a model that describes the phases of a cyber attack, from reconnaissance to actions on objectives. The Command & Control stage is where the adversary establishes and maintains communication with the compromised systems and moves laterally to expand their access and control.
Which of the following is a way to create event searches that run automatically and recur on a schedule that you set?
Scheduled Searches are a way to create event searches that run automatically and recur on a schedule that you set. You can use Scheduled Searches to monitor your environment for specific conditions or patterns, generate reports or alerts, or enrich your data with additional fields or tags. Workflows, Event Search, and Scheduled Reports are not ways to create event searches that run automatically and recur on a schedule.
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Allene
12 days agoEdna
19 days agoJame
26 days agoNelida
1 month agoMargo
1 month agoAudry
2 months agoFrank
2 months agoLaura
2 months agoAnika
3 months agoLennie
3 months agoGarry
3 months agoAntonette
3 months ago