CompTIA DS0-001 Exam Questions
- Topic 1: Database Fundamentals: This topic covers database structure types, SQL code development and modification based on scenarios, comparison of scripting methods and environments, and the impact of programming on database operations.
- Topic 2: Database Deployment: In this topic, you'll find discussions on database planning and design aspects. It also focuses on the implementation, testing, and deployment phases of databases.
- Topic 3: Database Management and Maintenance: Here, you'll learn about monitoring and reporting for database management and performance, common database maintenance processes, documentation production, and relevant tools usage. Lastly, the topic focuses on implementing data management tasks.
- Topic 4: Data and Database Security: This topic focuses on data security concepts, governance and regulatory compliance purposes, implementing authentication and authorization policies and best practices. Additionally, the topic discusses database infrastructure security, and understanding types of attacks and their effects on data systems.
- Topic 5: Business Continuity: Finally, this topic covers the importance of disaster recovery techniques. Moreover, the topic explains backup and restore best practices and processes.
Free CompTIA DS0-001 Exam Actual Questions
Note: Premium Questions for DS0-001 were last updated On Apr. 29, 2026 (see below)
A database administrator is migrating the information in a legacy table to a newer table. Both tables contain the same columns, and some of the data may overlap.
Which of the following SQL commands should the administrator use to ensure that records from the two tables are not duplicated?
The SQL command that the administrator should use to ensure that records from the two tables are not duplicated is option A. This command uses theUNIONclause to combine the records from the legacy table and the newer table into a single result set. TheUNIONclause also eliminates any duplicate records that may exist in both tables, and sorts the result by default. The other options either do not produce the desired result or have syntax errors. For example, option B would join the records from the two tables based on a common column, but not remove any duplicates; option C would return only the records that are common to both tables, but not the ones that are unique to each table; option D would produce a Cartesian product of the records from the two tables, which would increase the number of duplicates.Reference:CompTIA DataSys+ Course Outline, Domain 1.0 Database Fundamentals, Objective 1.2 Given a scenario, execute database tasks using scripting and programming languages.
A database administrator is creating a table, which will contain customer data, for an online business. Which of the following SQL syntaxes should the administrator use to create an object?
A)
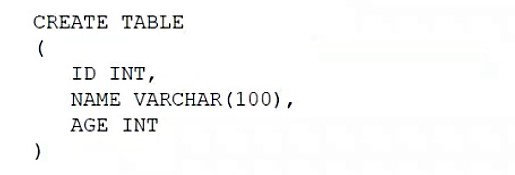
B)
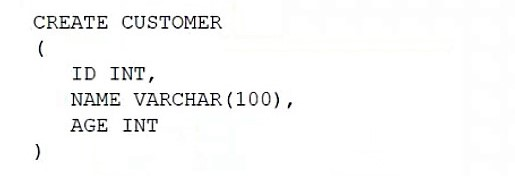
C)
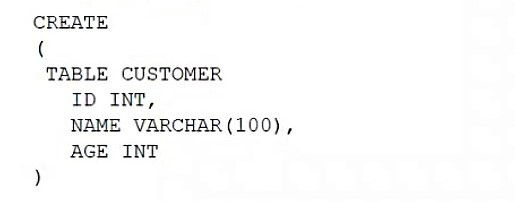
D)
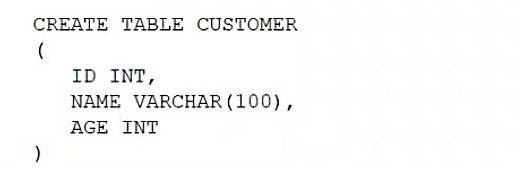
The SQL syntax that the administrator should use to create an object is option B. This syntax uses theCREATE TABLEstatement to define a new table namedcustomerwith four columns:customer_id,name,email, andphone. Each column has a data type and a constraint, such asNOT NULLorPRIMARY KEY. The other options either have syntax errors, use incorrect keywords, or do not specify the table name or columns correctly.Reference:CompTIA DataSys+ Course Outline, Domain 1.0 Database Fundamentals, Objective 1.1 Given a scenario, identify and apply database structure types.
Which of the following scripts would set the database recovery model for sys.database?
A)

B)

C)

D)
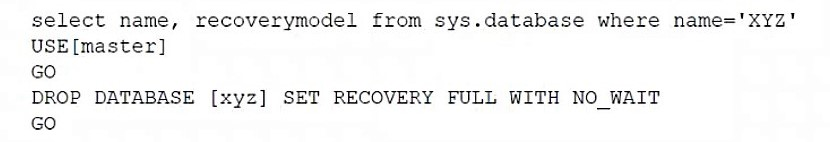
The script that would set the database recovery model for sys.database is option A. This script uses theALTER DATABASEstatement to modify the recovery model of the sys.database to full with no wait. The other options either have syntax errors, use incorrect keywords, or do not specify the recovery model correctly.Reference:CompTIA DataSys+ Course Outline, Domain 3.0 Database Management and Maintenance, Objective 3.1 Given a scenario, perform common database maintenance tasks.
Which of the following is an attack in which an attacker hopes to profit from locking the database software?
The attack in which an attacker hopes to profit from locking the database software is ransomware. Ransomware is a type of malware that encrypts the data or files on a system or network and demands a ransom from the victim to restore them. Ransomware can target database software and lock its access or functionality until the victim pays the ransom, usually in cryptocurrency. Ransomware can cause serious damage and loss to the victim, as well as expose them to further risks or threats. Ransomware can be delivered through various methods, such as phishing emails, malicious attachments, compromised websites, etc. The other options are either different types of attacks or not related to locking database software at all. For example, spear phishing is a type of phishing attack that targets a specific individual or organization with personalized or customized emails; SQL injection is a type of attack that inserts malicious SQL statements into an input field or parameter of a web application to manipulate or compromise the underlying database; on-path is a type of attack that intercepts and modifies the data in transit between two parties on a network.Reference:CompTIA DataSys+ Course Outline, Domain 4.0 Data and Database Security, Objective 4.4 Given a scenario, identify common types of attacks against databases
A database administrator needs to ensure that a newly installed corporate business intelligence application can access the company's transactional dat
a. Which of the following tasks should the administrator perform first?
The first task that the administrator should perform is to create a new service account exclusively for the business intelligence application. This will ensure that the application has the appropriate permissions and credentials to access the company's transactional data. The other options are either unnecessary, inefficient, or insecure. For example, building a separate data warehouse would require additional resources and time, setting up a nightly FTP data transfer would expose the data to potential breaches, sending the TNS names file would not guarantee that the application can connect to the database, and opening a new port on the database server would create a vulnerability for attackers.Reference:CompTIA DataSys+ Course Outline, Domain 2.0 Database Deployment, Objective 2.1 Given a scenario, install and configure database software and tools.
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Jennifer Nguyen
5 days agoJeffrey Torres
2 days agoLaura Green
2 days agoBarbara Martin
2 days agoDorothy Edwards
4 days agoAdelaide
23 days agoMargurite
30 days agoWhitley
1 month agoBrittney
1 month agoMalcom
2 months agoMaddie
2 months agoMalika
2 months agoJimmie
3 months agoCorinne
3 months agoFelicitas
3 months agoLeslee
3 months agoMica
3 months agoFrederic
4 months agoKristel
4 months agoMatilda
4 months agoJamal
5 months agoNana
5 months agoLoreen
5 months agoRosalyn
5 months agoReita
6 months agoLisha
6 months agoCristy
6 months agoLuke
6 months agoVincent
7 months agoMeghann
7 months agoGlenna
7 months agoAn
7 months agoJunita
7 months agoLili
8 months agoTasia
8 months agoLisha
8 months agoDomingo
10 months agoDiane
10 months agoCarlee
11 months agoRolland
11 months agoEdelmira
1 year agoDana
1 year agoMelvin
1 year agoTheron
1 year agoLatricia
1 year agoStacey
1 year agoRodrigo
1 year agoLavera
1 year agoRebecka
1 year agoAdelaide
1 year agoDonte
1 year agoMelvin
1 year agoGerald
1 year agoWilliam
1 year agoKate
1 year agoCatalina
1 year agoRachael
1 year agoChara
1 year agoNan
1 year agoEmogene
1 year agoRyan
1 year agoBrandee
1 year agoYuki
1 year agoMirta
2 years agoMyra
2 years agoFranchesca
2 years agoDaren
2 years agoFernanda
2 years agoDudley
2 years agoHoney
2 years agoJanna
2 years agoAn
2 years agoSommer
2 years agoTori
2 years agoGeraldo
2 years agoLeota
2 years agoJoye
2 years agoJoye
2 years agoMatt
2 years agoOzell
2 years agoLeonardo
2 years agoEileen
2 years agoKarol
2 years agoGery
2 years agoarmstrong
2 years agohekeho
2 years agomeezo
2 years agotokyo
2 years agobella chals
2 years ago