CompTIA 220-1202 Exam Questions
- Topic 1: Operating Systems: This section of the exam measures skills of a Desktop Support Technician and covers essential concepts around different types of operating systems and their specific purposes. It includes desktop and mobile platforms such as Windows, macOS, Linux, Android, and iOS. Candidates are expected to understand installation and upgrade methods, the use of system partitions, file system types like NTFS and exFAT, and how to work within vendor limitations. It also includes recognizing compatibility concerns across operating systems, configuring Windows editions, and utilizing various built-in Windows tools and features.
- Topic 2: Security: This section of the exam measures skills of a Technical Support Specialist and focuses on implementing basic security measures to protect devices and data. Topics include identifying and removing malware, configuring security settings like firewalls and access controls, and understanding authentication techniques. Candidates should also be familiar with securing wireless and wired networks, using encryption, recognizing social engineering attacks, and applying best practices for physical security and data disposal.
- Topic 3: Software Troubleshooting: This section of the exam measures skills of a Desktop Support Technician and evaluates the ability to troubleshoot common software-related issues. Candidates must identify and resolve problems related to system crashes, application errors, slow performance, and boot issues. The domain also covers mobile OS troubleshooting and the use of diagnostic tools to ensure system stability and reliability across different platforms and environments.
- Topic 4: Operational Procedures: This section of the exam measures skills of a Technical Support Specialist and involves understanding standard operating procedures in IT environments. It covers the documentation process, incident response, change management, and disaster recovery planning. Candidates also need to be familiar with safety procedures, environmental controls, and professionalism in customer communication. The section highlights the importance of following organizational policies and using remote support tools effectively.
Free CompTIA 220-1202 Exam Actual Questions
Note: Premium Questions for 220-1202 were last updated On Apr. 22, 2026 (see below)
Technicians are failing to document user contact information, device asset tags, and a clear description of each issue in the ticketing system. Which of the following should a help desk management team implement for technicians to use on every call?
Comprehensive and Detailed Explanation From Exact Extract:
Standard Operating Procedures (SOPs) define the mandatory steps and expectations technicians must follow during support calls. This includes documentation standards such as logging user info, asset details, and issue descriptions in the ticketing system. Implementing SOPs ensures consistency and accountability.
A . SLAs define response/resolution times but not documentation practices.
B . Call categories organize types of issues but don't guide technician actions.
D . Knowledge base articles provide solutions to known problems but don't ensure proper ticket documentation.
CompTIA A+ 220-1102 Objective 4.2: Summarize best practices associated with types of documentation and support systems information.
Study Guide Section: Documentation practices, SOPs, ticketing protocols
===========================
A technician inspects the following workstation configuration:
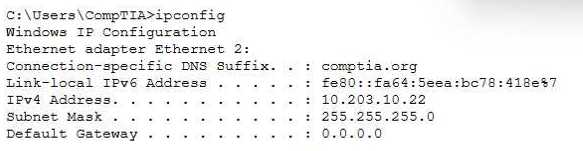
The workstation is unable to open any external websites. The browser displays an error message that says that the site cannot be reached.
The correct answer is C. The default gateway is not set, and this is clearly indicated by the ipconfig output showing the Default Gateway: 0.0.0.0. In TCP/IP networking, the default gateway is the router address that allows a workstation to communicate with networks outside its local subnet, including the internet. Without a valid default gateway, a device can only communicate with other devices on the same local network.
According to the Quentin Docter -- CompTIA A+ Complete Study Guide, a missing or incorrect default gateway is one of the most common causes of a system being unable to access external resources. The guide explains that when a destination IP address is outside the local subnet, the workstation forwards the traffic to the default gateway. If no gateway is defined, the traffic has nowhere to go and is dropped.
The Travis Everett & Andrew Hutz -- CompTIA A+ All-in-One Exam Guide reinforces that an IP address such as 10.203.10.22 with a subnet mask of 255.255.255.0 is valid for internal communication. The DNS suffix comptia.org is also not responsible for routing failures. DNS resolves names to IP addresses, but routing still requires a gateway.
The Mike Meyers / Mark Soper Lab Manual further clarifies that a subnet mask error would prevent even local communication, which is not indicated here. Because only external websites are unreachable, the absence of a default gateway is the definitive root cause.
An end user wants to have a sales printer added to their computer. The printer is on the domain. Which of the following is the best method for the technician to add the printer?
Comprehensive and Detailed Explanation From Exact Extract:
In a domain environment, printers are typically deployed via a print server. Users can browse available printers on the server and install them directly.
All-in-One Exam Guidementions:
''In a corporate domain, printers are managed via a centralized print server. Users can select the desired printer from the server's shared list.''
A technician reviews an organization's incident management policy. The organization uses a third-party vendor with multiple tools to protect its assets. What service type is this?
Comprehensive and Detailed Explanation From Exact Extract:
Managed Detection and Response (MDR)involves outsourcing security monitoring to a third-party that uses multiple tools and analytics.
FromTravis Everett -- All-in-One Exam Guide:
''MDR providers handle threat detection and response using a combination of advanced tools, analytics, and expert personnel.''
Which of the following malware types typically has very high computing resource usage?
Comprehensive and Detailed Explanation From Exact Extract:
Cryptominersexploit system resources to mine cryptocurrency, often without user consent, leading to high CPU and GPU usage.
FromQuentin Docter -- CompTIA A+ Complete Study Guide:
''Cryptomining malware can cause significant performance degradation by monopolizing system resources like CPU and GPU to mine digital currency.''
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Sharon Baker
5 days agoJason Mitchell
59 minutes agoMaria Davis
4 days agoCharlette
25 days agoJanella
1 month agoRaymon
1 month agoCammy
2 months agoMiles
2 months agoLilli
2 months agoKenneth
2 months agoBrent
3 months agoJerry
3 months agoMarsha
3 months agoDaren
3 months agoAlana
4 months agoHyman
4 months agoLorrie
4 months agoLisbeth
4 months agoDorthy
5 months agoThaddeus
5 months agoDella
5 months agoMargurite
5 months agoLaurene
6 months agoAlecia
6 months agoElin
6 months agoSilvana
6 months agoGarry
7 months agoFrancine
7 months agoMitsue
7 months agoJudy
7 months agoTheodora
7 months agoAnnmarie
8 months agoDorothea
8 months agoParis
10 months agoDevon
10 months agoIrma
10 months agoJerry
11 months agoRoy
11 months agoMa
12 months agoLeonor
1 year agoBenedict
1 year ago