Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Cisco Exam 350-501 Topic 19 Question 82 Discussion
Actual exam question for
Cisco's
350-501 exam
Question #: 82
Topic #: 19
[All 350-501 Questions]
Topic #: 19
Simulation 7
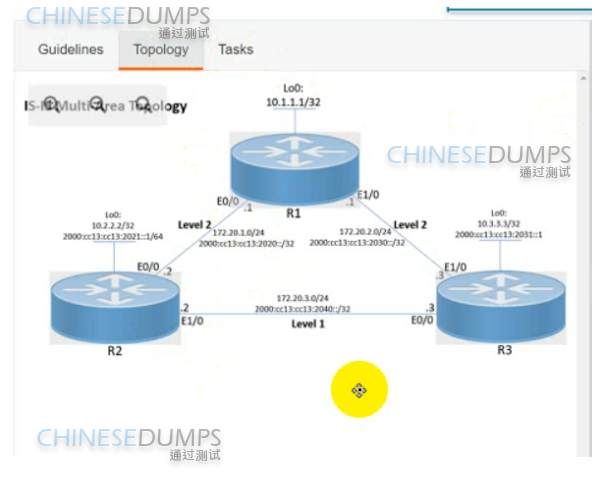
Refer to the exhibit.

Suggested Answer:
A
R1
key chain AUTH_ISIS
key 2
key-string C1sco!
exit
int range et0/0 , et1/0
isis authen key-chain AUTH_ISIS
ip isis
isis metric 15
Copy run start
R2
key chain AUTH_ISIS
key 2
key-string C1sco!
exit
int range et0/0 , et1/0
isis authen key-chain AUTH_ISIS
ip isis
isis metric 20
Copy run start
R3
key chain AUTH_ISIS
key 2
key-string C1sco!
exit
int range et0/0 , et1/0
isis authen key-chain AUTH_ISIS
ip isis
isis metric 25
Copy run start
Alona
3 days agoEttie
4 days agoTitus
5 days agoVenita
6 days ago