Arcitura Education S90.20 Exam - Topic 1 Question 31 Discussion
Topic #: 1
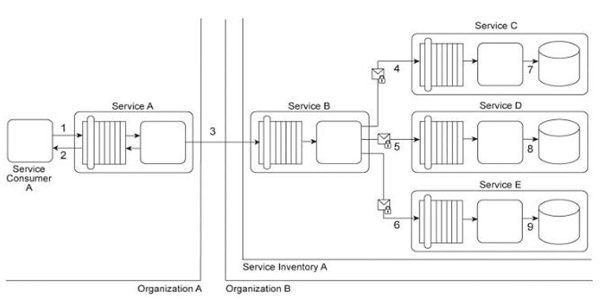
Service Consumer A sends a request to Service A (1). Service A replies with an acknowledgement message (2) and then processes the request and sends a request message to Service B (3). This message contains confidential financial data. Service B sends three different request messages together with its security credentials to Services C, D, and E (4, 5, 6). Upon successful authentication, Services C, D, and E store the data from the message in separate databases (7, 8, 9) Services B, C, D, and E belong to Service Inventory A, which further belongs to Organization B .Service Consumer A and Service A belong to Organization A .The service contracts of Services A and B both comply with the same XML schema. However, each organization employs different security technologies for their service architectures. To protect the confidential financial data sent by Service A to Service B, each organization decides to independently apply the Data Confidentiality and the Data Origin Authentication patterns to establish message-layer security for external message exchanges. However, when an encrypted and digitally signed test message is sent by Service A to Service B, Service B was unable to decrypt the message. Which of the following statements describes a solution that solves this problem?
Alyssa
5 months agoJohnathon
6 months agoLauna
6 months agoOliva
6 months agoHobert
6 months agoHubert
6 months agoChanel
6 months agoThora
6 months agoDouglass
6 months agoSalena
7 months agoWilda
7 months agoShelia
7 months agoBette
7 months ago