Arcitura Education S90.20 Exam - Topic 1 Question 29 Discussion
Topic #: 1
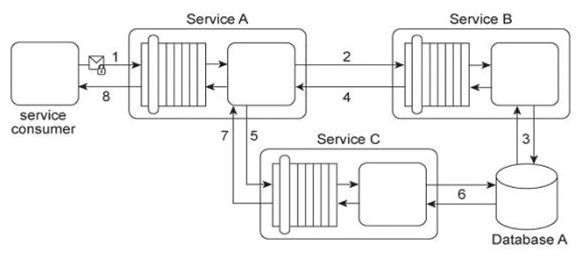
Service A provides a customized report generating capability. Due to infrastructure limitations, the number of service consumers permitted to access Service A concurrently is strictly controlled. Service A validates request messages based on the supplied credentials (1). If the authentication of the request message is successful, Service A sends a message to Service B (2) to retrieve the required data from Database A (3). Service A stores the response from Service B (4) in memory and then issues a request message to Service C (5). Service C retrieves a different set of data from Database A (6) and sends the result back to Service A (7). Service A consolidates the data received from Services B and C and sends the generated report in the response message to the service consumer (8). It has been discovered that attackers have been gaining access to confidential data exchanged between Service A and Service B, and between Service A and its service consumers. What changes can be made to this service composition architecture in order to counter this threat?
Alida
5 months agoLucy
6 months agoAlva
6 months agoHenriette
6 months agoMike
6 months agoDenny
6 months agoArlene
6 months agoReyes
6 months agoVannessa
6 months agoYolando
7 months agoMurray
7 months ago